Whether you work in the tech sector or not, you’ve probably heard of the term “cybersecurity” at least once in your life. Cybersecurity plays an important role in people’s lives, especially now with how everything is easily accessible online.
It can help to educate yourself on the basics of cybersecurity and what it entails. After all, protecting yourself from cyberattacks is crucial when you want to keep any sensitive and private information safe.
What Is Cybersecurity?


Cybersecurity refers to the protection of Internet-connected systems from cyber threats. It is used to protect data centers and other computerized systems against unauthorized access. Also known as computer security or information technology security, cybersecurity is important in ensuring sensitive data — whether it belongs to one individual or an entire organization — is properly protected from cyber attacks. Many attackers often aim to hack into your PCs, networks, servers, or mobile devices in order to access, delete, or extort sensitive data stored on such gadgets. As such, it’s vital to always keep your connections secure. This is especially when private data is involved.
As technologies evolve, so do the complexities of cybersecurity mature. However, in contrast, the evolution of technology also provides new methods and approaches to cyber attacks. It’s also worth noting that anyone can be a target of cyber attacks. Whether you are a large corporation or a small organization, you can fall victim to even the most common of cyber attacks. Thus, it’s important to keep your cybersecurity systems up to date to ensure the safety of your data or that of the people around you.
Types of Cyber Attacks


It can be quite a challenge to keep up with new the changes in technology and security. Nevertheless, it’s important to stay updated on the different cyber attacks that can damage you or your business. Educating yourself will help prepare you better for any potential vulnerabilities in your cybersecurity that you may be unaware of. Some of the most common types of cyber attacks include:
Malware
Short for ‘malicious software,’ malware is a software that gives any file or program the ability to harm a computer, server, or computer network. Several types of malware exist and can range from computer viruses to Trojan horses. Spyware and adware are also considered forms of malware. Antivirus softwares and firewalls are some common approaches to protecting and preventing malware from infecting your computer.
Password Attack
Simply put, a password attack involves a third party trying to forcefully gain access to a user’s password. A password attack can be particularly harmful, as it can compromise your online accounts. Not only can this lead to stolen identities, but it can also lead to blackmail and even financial exploitation.
Social Engineering
This type of cyber threat relies on using human interaction to trick users into breaking their company’s security procedures. This, in turn, gives the attacker access to confidential information.
Phishing
Phishing allows attackers to obtain or steal sensitive data by sending fraudulent emails. Often, these fake emails resemble ones that are sent from reputable sources. Thus, the emails can fool users into providing personal data that can be later used to access their accounts. Notably, phishing is similar to social engineering. However, phishing involves more technical trickery — such as fabricated emails — to deceive users.
Types of Cybersecurity


In order to properly protect your network, it’s important to stay up to date on the different types of cybersecurity. This can help you determine which type works best for you or your line of work. The different types of cybersecurity include the following:
Network Security
Network security protects network traffic by controlling connections. This can help prevent threats from intruding or spreading on your internal networks. By protecting the infrastructure and gaining access to it, network security ensures that your internal networks are secure. In order to flag abnormal traffic and be alerted of threats, the security team uses machine learning to manage network security monitoring.
Network administrators implement policies and procedures so that no unauthorized access, modification, and exploitation of networks can occur. Network security implementations are extra logins, new passwords, application security, antivirus programs, firewalls, and so on.
Cloud Security
Cloud security is a security tool that is software-based. It helps in protecting and monitoring data in your cloud-based services and applications. For enterprise users to better secure their data, new security tools are being created and implemented by cloud providers.
Application Security
Application security is a security measure that involves finding and fixing security vulnerabilities in an application. It uses hardware and software methods to help tackle external threats that can arise in an application’s development stage. Developers make use of application security in order to prevent different threats that may attack their application. Some types of application security are firewalls, encryption programs, antivirus programs, and so on.
Critical Infrastructure Security
Critical infrastructure security can be considered a particularly important form of cybersecurity. It involves the protection of systems and networks that are considered vital in the security of a nation, its people, and its economy. Critical infrastructures include electricity grids, water purification, traffic lights, and hospitals. Cyber attacks that target these systems can cause harm and damage to a society. But, it’s worth noting that many of these systems are not only owned by the private sector, but controlled by this sector as well. This can make it much more challenging to adequately control and update the security required for such infrastructures.
Internet of Things (IoT) Security
The Internet of Things pertains to the integration of Internet connectivity to different digital and mechanical devices. Therefore, IoT security deals with the protection of connected networks and devices in the IoT. Appliances, sensors, televisions, WiFi routers, and printers are some examples of such devices.
It’s worth noting that IoT devices do not have the best of security. This is due to device manufacturers neglecting IoT security. There continues to be a lack of prioritizing for IoT security. As such, IoT devices pose security challenges for their users, as the lack of patching often places them in a state of vulnerability.
Elements of Cybersecurity


Information Security
This involves preventing the loss of sensitive information to illegal sources. It refers to the assurance that personal data will not be lost when issues like system malfunctions, theft, or other critically damaging situations arise.
Network Security
Network security refers to thorough security policies and measures to monitor your network and data. It entails checking through users and granting them access to a network’s data to allow the exchange of information. Users are assigned IDs and passwords, or other forms of authentication, to further enhance a network’s security.
Application Security
Application security involves adding security features in an application, particularly during its development. This can help protect applications and websites from cyber attacks and other security vulnerabilities. Moreover, weak application security can become a point of interference for cyber attacks.
End-User Education
This is the weakest link that requires proper training to lessen vulnerabilities to cyber attacks. Regular end-user education is essential to underscore system vulnerabilities to cyber threats and computer security loopholes.
Why Is Cybersecurity Important?
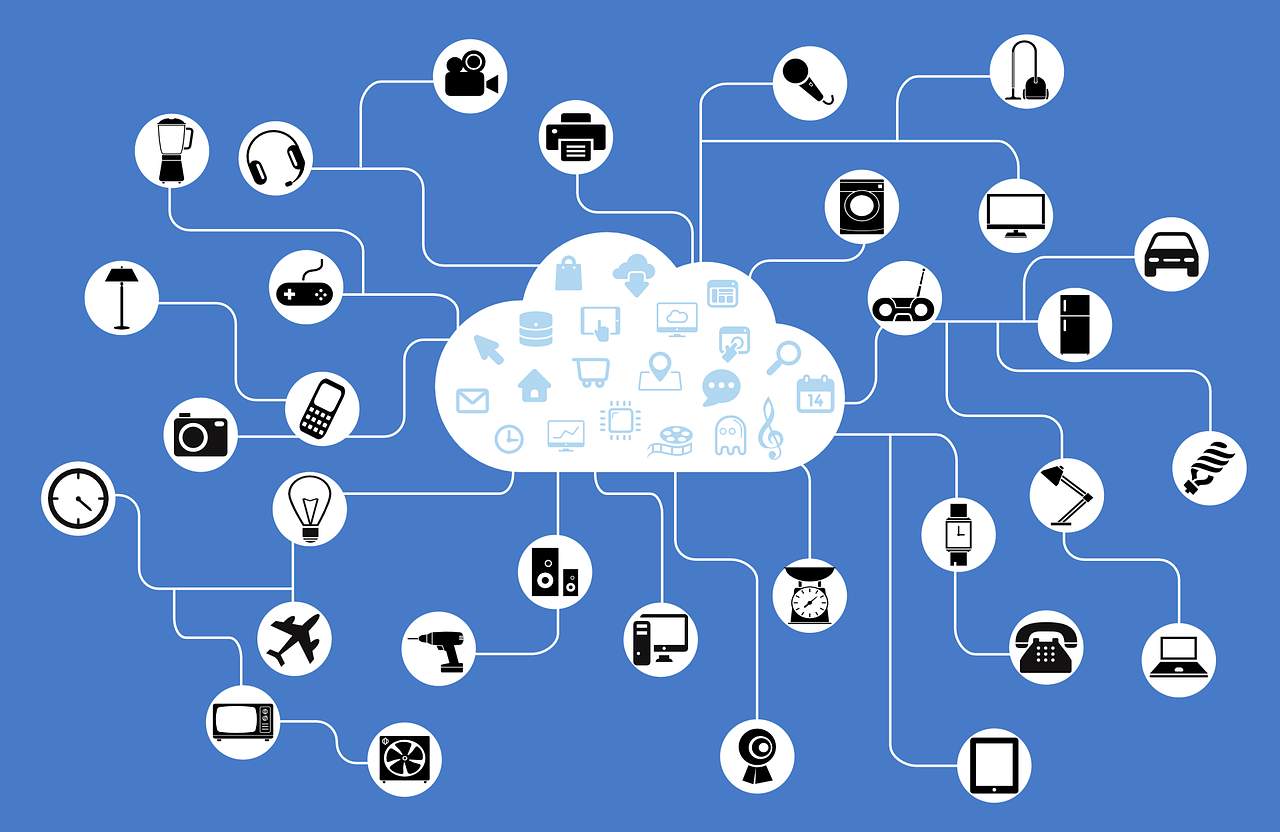
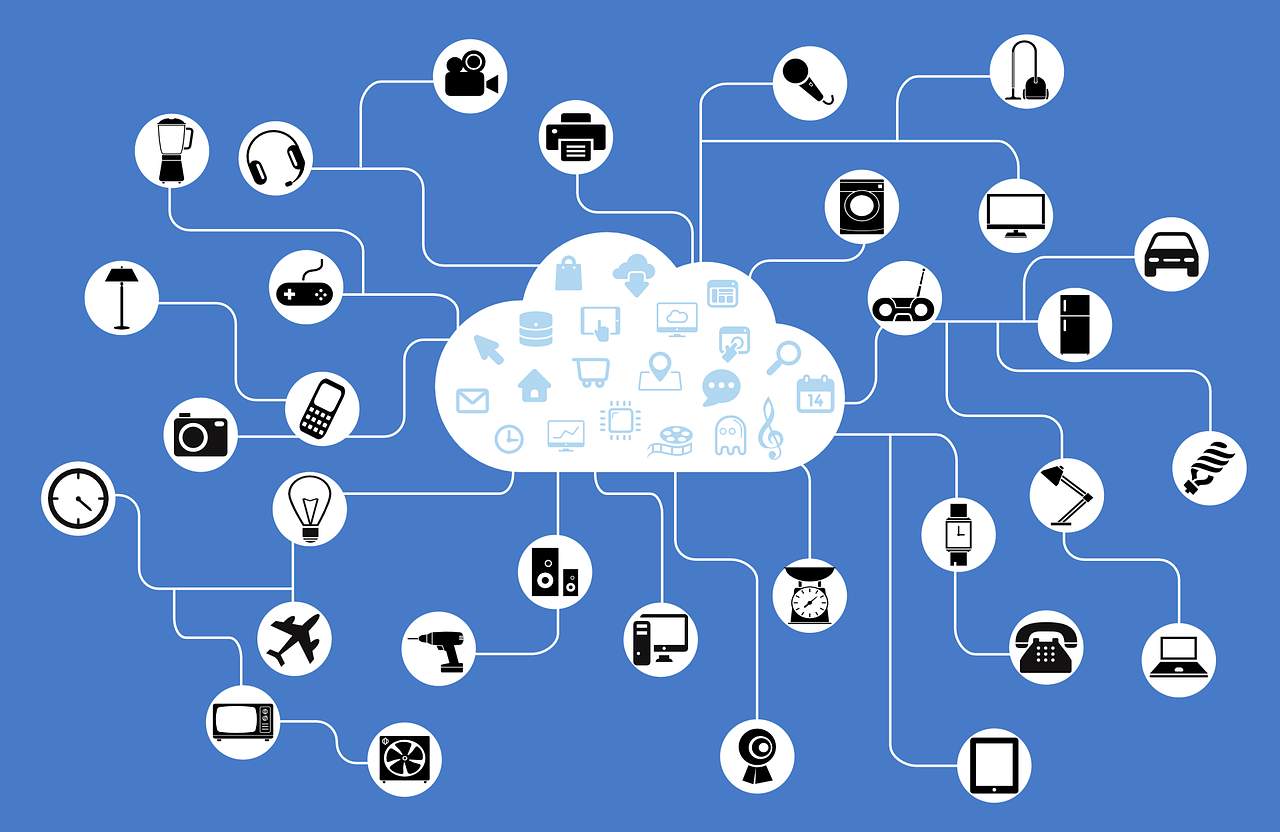
Increase Of IoT
IoT devices are now much more common in homes and offices. Normally, these devices can simplify tasks. Additionally, they can offer the desired level of control in our environment or work spaces. However, it is their proliferation that presents a problem.
If not handled properly, each IoT device connected to your network can open a pathway to cyber threats. These cyber threats can then lead to cyber attacks that can leave your network or business vulnerable. Since IoT devices introduce a wide range of computer security weaknesses, it’s thus wise wise to conduct vulnerability checks to help address risks presented by these devices.
Increase In Available Hacking Tools
The vast availability of hacking tools and programs on the Internet means there is also a growing threat from hackers and cyber attackers. The accessibility of such harmful tools can thus lead to an increase of damaging attacks on cybersecurity.
Rising Cost Of Breaches
Without a doubt, a cybersecurity breach can cause customers to lose trust in a business. A reputation for having poor cybersecurity can also lead to an inability to win or nurture new businesses.
Advantages of Cybersecurity
With many risks come many advantages to cybersecurity as well. Just like the term says, cybersecurity offers security to a system or network. But, there are more advantages besides the basic security of a network. Some cybersecurity benefits include:
Improves Information Security
With proper information security through good cybersecurity, a business has a better chance at establishing stakeholder confidence. Moreover, cybersecurity helps with business continuity management thanks to the protection of a business’ data and information.
Safeguards Sensitive Information
Cybersecurity helps keep personal data safe. The unauthorized access of such data — like patient data and sales data, for example — can lead to misuse and harm.
Creates A Safe Working Environment
Without proper cybersecurity, employees become vulnerable at the hands of cyberattacks. By integrating proper cybersecurity solutions, you can ensure your business — and your people — remain safe from potential cyber attacks. Additionally, this can lead to improved productivity among employees.
Establishes Customer Trust
What is a business without its customers? And what are customers without their trust? Proper cybersecurity systems can help establish a sense of ease in customers. This is because they know their personal information will remain private. Failure to protect such data means a failure to protect your customers.
Cybersecurity Challenges


Cybersecurity sees regular challenges in the form of cyber attackers, loss of data, privacy breaches, and continuous changes in the tech sector. Cyber attacks have yet to show signs of slowing down. Thus, it’s important to know what you may face when it comes to protecting your networks and devices. Some cybersecurity challenges are:
The Evolving Nature of Security Risks
The emergence of new technologies means new approaches for cyber attacks as well. Therefore, cybersecurity elements require regular updates and assessments to detect potential vulnerabilities.
Artificial Intelligence
Artificial intelligence (AI for short) can be both an asset and a hindrance to cybersecurity. Automation can no doubt help improve cybersecurity. However, the current limitations of AI can also put a halt to cybersecurity evolution. At this point, it is simply a matter of time before AI matures into an innovation that elevates cybersecurity to the next level. On the other hand, though, AI and automation could also lead to more mature cyber attacks as well.
End-User Education
Another challenge is end-user education. If employees are not properly educated on cybersecurity, they may accidentally bring viruses into their work computer, laptop, or smartphone. A lack of awareness may lead to a complete disregard of cybersecurity’s importance and impact on a person’s day-to-day life.
Job Shortages
As development in data from organizations turns out to be progressively significant, the requirement for more cybersecurity personnel increases. It is estimated that there are 2,000,000 vacant cybersecurity jobs around the world. Without cybersecurity officers to help oversee and analyze cybersecurity, an organization may be left vulnerable to potential cyber threats.
Cybersecurity Vendors
Cybersecurity vendors use the endpoint, network, and developed security measures for protection against threats and prevention of loss of data. Cisco, McAfee, and Trend Micro are the top three notable cybersecurity vendors.
Cisco’s main focus is on the network. It permits its clients to use firewalls, VPNs, and advanced malware protection, alongside supporting email and endpoint security. Additionally, real-time malware blocking is supported by Cisco.
Meanwhile, McAfee produces cybersecurity products for consumers and enterprise users. They offer services like data protection and encryption.
Lastly, Trend Micro deals with anti-malware services. Their products provide cyber threat protection for systems like hybrid clouds, SaaS, and the IoT. Trend Micro offers endpoint, email, and web security to its users.
Careers In Cybersecurity


As the landscape of cyber threats and cyber attacks grow, people are thus required to equip themselves with the necessary skills and awareness regarding cybersecurity. Though there are several jobs that seek individuals who are knowledgeable about cybersecurity, certain job opportunities stand out in particular. Some of these include:
Chief Information Security Officer (CISO)
The CISO acts on a company or organization’s security program. Moreover, they oversee the operations of the IT security department. They ensure a company’s information assets remain protected.
Security Engineer
The main objective of a security engineer is to protect the assets of an organization or company from cyber threats. Additionally, they put emphasis on quality control within the infrastructure of the IT department. They test security softwares that used in monitoring networks and security breaches.
Security Architect
The security architect is responsible for the planning, analysis, designing, testing, maintenance, and support of an enterprise’s critical infrastructure. Interestingly, security architects can benefit from adopting the same mentality that hackers have. This is because they must anticipate the moves and motives of cyber attackers. Doing so can help them heighten their network’s security better.
Security Analyst
The duty of a security analyst is to detect any security violations on a computer system or network. They look into security breaches and report on other cyber threats. Security analysts are especially crucial in the development of a company’s security policies and standards.
Conclusion
There’s no denying that cybersecurity is a universal concern that affects different people and organizations. Cybersecurity continues to be a major priority among large corporations and financial institutions alike. Faulty cybersecurity can lead to the downfall of these organizations. Nevertheless, even a regular citizen can prioritize cybersecurity as much as any other important organization. Considering how much people stay online, it’s no wonder why cybersecurity remains to be a hot topic in the tech sector to this day. Whether you are a business owner or just want to protect your data, keeping up to date on cybersecurity can go long way in keeping your information safe.


