Importance of Downloading Software Safely
Downloading software is a common practice for most computer users. Whether it’s an essential productivity tool, a fun gaming application, or a utility program, we rely on software to enhance our digital experience. However, it’s crucial to prioritize the safety of our devices and personal data when downloading software from the internet. Here’s why downloading software safely should be a top priority:
The internet is teeming with countless websites offering free software downloads. Unfortunately, not all of these sources are trustworthy. Malicious actors often disguise harmful programs as legitimate software, aiming to infiltrate users’ systems and compromise their security. By downloading software from untrusted sources, you expose yourself to the risk of malware, viruses, and other cyber threats.
Safe software downloading starts with thorough research. Before downloading any software, it is essential to investigate the program and verify its authenticity. Look for trusted sources, such as reputable software developers or well-established download platforms. Reading user reviews and checking online forums can provide insights into the software’s reliability and potential security concerns.
The official website of the software developer is typically the safest source for downloading software. Companies often have robust security protocols in place to ensure that their software is free from malware and other harmful elements. Visiting the official website not only guarantees the authenticity of the software but also helps you avoid counterfeit versions that may contain malicious code.
Verifying the authenticity of the software is crucial to ensure that you are downloading the legitimate version. Some unscrupulous websites offer modified versions of popular software that may contain hidden malware. Always double-check the digital signature or the MD5/SHA checksum provided by the software developer. These verification steps can help safeguard your system from downloading fake or tampered software.
Checking the file integrity is another essential aspect of safe software downloading. Before running the installation, perform a quick antivirus scan on the downloaded file. This helps detect any potential malware or viruses that might have slipped through other security measures. Additionally, using a trusted file integrity checker can confirm that the file has not been altered or tampered with during the download process.
When installing software, it’s crucial to understand the installation process and the options available. Some software may request permission to access certain sensitive areas of your computer or require additional software components to function correctly. Make sure to carefully read and understand the installation prompts and only allow necessary permissions to avoid any potential security risks.
One common source of potentially unwanted programs (PUPs) is bundled software. Additional software might be included with the main program you are downloading, often in the form of toolbars, browser extensions, or other applications. Pay close attention to the installation process and deselect any bundled programs that you do not need or trust.
Maintaining a clean and secure digital environment is an ongoing process. By regularly updating your software to the latest version, you ensure that you have the most up-to-date security patches and bug fixes. Developers often release updates to address vulnerabilities that cybercriminals could exploit. Keeping your software updated is a vital part of maintaining a secure system.
Lastly, if you encounter any suspicious or potentially malicious software during the download or installation process, it’s crucial to report it. Notify the software developer or the appropriate authorities so they can take the necessary actions to prevent others from falling victim to such threats.
Researching the Software
Before downloading any software, it is essential to conduct thorough research to ensure its reliability and safety. Taking the time to investigate the software will help you make an informed decision and avoid potential security risks. Here are some key steps to follow when researching software:
1. Read Reviews and Recommendations: Start by reading user reviews and recommendations from trusted sources. These reviews can provide valuable insights into the software’s performance, user-friendliness, and overall reputation. Look for reviews from reputable technology websites, online forums, and social media platforms.
2. Check the Developer’s Credentials: Research the software developer or company behind the software. Look for information about their reputation, track record, and any past security incidents. Reputable developers are more likely to prioritize user security and regularly update their software to address vulnerabilities.
3. Assess User Ratings and Popularity: Consider the overall user rating and popularity of the software. High ratings and widespread usage indicate that the software is trusted and reliable. However, be cautious of artificially inflated ratings or popularity, as these can be manipulated by unethical practices.
4. Look for Online Communities and Forums: Engage with online communities and forums dedicated to the software you’re interested in. These platforms can provide valuable insights, tips, and troubleshooting assistance. Active and engaged communities indicate a strong user base that can offer trustworthy information.
5. Consider the Software’s Age and Update Frequency: Take into account the software’s age and how frequently it receives updates. Newer software may have less testing and review feedback compared to more established programs. However, regular updates show the developer’s commitment to fixing bugs, addressing security vulnerabilities, and improving overall performance.
6. Look for Official Documentation and User Guides: Check if the software has official documentation, user guides, or tutorials. Comprehensive documentation indicates that the developer values transparency and wants to provide users with the necessary resources to use the software effectively and securely.
7. Evaluate Security Features: Assess the software’s security features. Look for features like data encryption, secure connections (HTTPS), password protection, and two-factor authentication. Software that prioritizes security is more likely to protect your sensitive information and provide a safer user experience.
8. Consider Compatibility and System Requirements: Ensure that the software is compatible with your operating system and meets the required system specifications. Incompatible software may not function properly or lead to system instability, potentially exposing you to security risks.
9. Consult with IT Professionals: If you’re unsure about the software’s safety or need expert advice, consult with IT professionals or cybersecurity experts. They can offer valuable insights, perform security assessments, and recommend safe alternatives if necessary.
Remember, the research stage is crucial in determining the reliability and safety of the software you plan to download. By following these research steps, you can make an informed decision and minimize the risks associated with downloading and installing software from the internet.
Choosing a Trusted Source
When it comes to downloading software, selecting a trusted source is of utmost importance. The source from which you obtain software can greatly impact its safety and reliability. Here are key factors to consider when choosing a trusted source for software downloads:
1. Official Developer’s Website: The official website of the software developer is often the most reliable and secure source for downloading software. Developers typically have stringent security measures in place to ensure the integrity of their software. Visiting the official website reduces the risk of downloading counterfeit or tampered versions of the software.
2. Reputable Download Platforms: Look for reputable download platforms that have a solid track record of providing secure software downloads. Examples include well-known platforms like Microsoft Store, Apple App Store, Google Play Store, and reputable open-source repositories like GitHub. These platforms often have strict standards for software quality and security.
3. Trusted Technology Websites: Technology websites and online publications that focus on software reviews and recommendations can provide trustworthy sources for downloading software. Look for websites with a good reputation, a history of unbiased reviews, and a knowledgeable team of experts who thoroughly test and evaluate software before recommending it to users.
4. Developer’s Partner Networks: Some software developers partner with other reputable companies or organizations to distribute their software. These partnerships can provide an additional layer of trust and ensure that the software is sourced from a reliable and verified distributor.
5. Open Source Communities: Open-source software communities can be a great source for downloading software. These communities often have dedicated websites or platforms where developers share their creations. However, it is still crucial to assess the reputation and credibility of the particular community and the software being offered.
6. Avoid Peer-to-Peer (P2P) Networks: Peer-to-peer networks, where users share files directly with each other, can be risky when it comes to software downloads. These networks lack centralized control, making it easier for malicious actors to distribute compromised or counterfeit software. It is best to avoid downloading software from P2P networks to minimize the risk of malware or other security vulnerabilities.
7. Check for Digital Signatures: Digital signatures provide an additional layer of authenticity and security. When downloading software, verify if the developer has digitally signed the software. Digital signatures can help ensure that the software has not been tampered with or modified by unauthorized sources.
8. Trustworthy Recommendations: Seek recommendations from trusted sources such as friends, colleagues, or industry experts who have experience in using the software you are interested in. Their firsthand experiences can provide valuable insights and help you choose a trusted source for downloading the software.
Remember, choosing a trusted source for software downloads is essential for ensuring the safety and security of your computer and personal data. By using reputable sources, you can minimize the risk of downloading malware, counterfeit software, or other security threats.
Downloading from the Official Website
When it comes to downloading software, one of the safest and most reliable sources is the official website of the software developer. Downloading from the official website offers several advantages, including enhanced security and the assurance of obtaining the authentic version of the software. Here are key reasons why you should consider downloading software from the official website:
1. Authenticity Guarantee: The official website of the software developer provides a guarantee of authenticity. Software downloaded from unofficial or third-party websites may be modified, tampered with, or include additional malicious components. By downloading from the official website, you can rest assured that you are obtaining the genuine, unaltered version of the software.
2. Enhanced Security Measures: Developers prioritize the security of their software and are more likely to implement robust security measures on their official websites. This includes regular scanning for malware, secure download protocols (such as HTTPS), and protected servers for hosting the software files. Downloading from the official website reduces the risk of downloading software infected with malware or viruses.
3. Access to the Latest Version: The official website ensures that you have access to the most recent version of the software. Developers regularly release updates that address security vulnerabilities, fix bugs, and introduce new features. By downloading from the official website, you can enjoy the latest enhancements and benefit from improved security measures.
4. Reliable Support and Documentation: Official websites typically provide reliable support channels, including FAQs, user guides, and documentation. If you encounter any issues or have questions about the software, you can turn to these resources for assistance. Official support channels ensure reliable information and can help you troubleshoot problems or learn how to use the software effectively.
5. Unmodified Software Installation Files: Downloading software from the official website helps ensure that you receive unmodified installation files. When downloading from third-party websites or platforms, there is a higher risk of the software being bundled with additional programs, adware, or potentially unwanted software (PUP). These bundled programs can compromise system performance and security. By downloading directly from the official website, you avoid such unwanted extras.
6. Reliability and Stability: Official websites are generally more reliable and stable compared to other sources. They have dedicated servers and infrastructure to handle the software distribution process, reducing the likelihood of interrupted or incomplete downloads. Additionally, official websites often offer multiple download mirrors or servers to cater to a broader audience, ensuring faster and more reliable downloads.
7. Verification of Legal Licenses: Official websites provide legitimate software along with the necessary licensing information. This ensures that you are downloading and using the software legally, avoiding any copyright or licensing infringements. Unauthorized downloads from third-party sources may result in legal consequences and lack the necessary license agreements.
8. Direct Communication with the Developer: Downloading from the official website establishes a direct line of communication with the software developer. This can be beneficial when reporting bugs, requesting features, or seeking additional information. By supporting the developer through the official website, you contribute to the software’s development and further improvements.
When it comes to downloading software, prioritizing the official website of the software developer is a smart choice. By doing so, you can ensure the authenticity, security, and reliability of the software, maximizing your digital experience while minimizing potential risks.
Verifying the Authenticity of the Software
Verifying the authenticity of the software is a crucial step in ensuring that you are downloading legitimate and trustworthy software. With the rise of counterfeit and tampered software versions, it is essential to take measures to confirm the authenticity of the software before downloading or installing it. Here are some effective methods to verify the authenticity of the software:
1. Digital Signatures: Check if the software has a digital signature. A digital signature is a cryptographic security feature that confirms the software’s integrity and authenticity. It serves as a unique identifier and verifies that the software has not been modified or tampered with since it was signed by the developer.
2. MD5/SHA Checksum: Utilize the MD5 or SHA checksum provided by the software developer. The checksum is a string of numbers and letters generated using an algorithm that verifies the integrity of a file. By comparing the checksum of the downloaded file with the one provided by the developer, you can ensure that the file has not been altered during the download process.
3. Software Developer’s Website: Visit the official website of the software developer and confirm that the software is listed there. The official website is often the most trustworthy source for obtaining legitimate software. Developers typically provide a download page or section where users can access verified and authentic versions of their software.
4. Compare File Sizes: Compare the file size of the software you intend to download with the file size mentioned on the official website. If the file size differs significantly, it may indicate that the file has been modified or tampered with. In such cases, it is advisable to avoid downloading the software and instead report the issue to the developer.
5. Verify Developer’s Identity: Ensure that the software developer’s details match what is provided on their official website. Verify their company name, contact information, and any other relevant details. Additionally, check if the developer has a history of providing reliable and legitimate software by researching customer reviews and testimonials.
6. Research Third-Party Validation: Look for third-party validation or certifications that indicate the software’s authenticity and security. Some trusted organizations specialize in evaluating software for authenticity, security, and compliance. Look for certifications or endorsements from these organizations, as they add an extra layer of assurance.
7. User Reviews and Ratings: Read user reviews and ratings from reputable sources to gauge the authenticity and quality of the software. Consider reviews from trusted technology websites, online forums, and social media platforms. User feedback can provide insights into the software’s reliability and help confirm its authenticity.
8. Scan for Malware: Before proceeding with the installation, scan the downloaded software file with reputable antivirus or malware scanning tools. This helps identify any potential threats or malicious code embedded within the file. If the scan detects malware or suspicious behavior, it is best to abort the installation and report the issue to the software developer.
Verifying the authenticity of the software is crucial to ensure that you are downloading legitimate, secure, and reliable software. By following these verification methods, you can minimize the risk of downloading counterfeit or tampered software, protecting your device and personal information from potential harm.
Checking the File Integrity
Checking the integrity of the downloaded software file is an important step in ensuring that the file has not been damaged or tampered with during the download process. Verifying the file integrity helps guarantee that you are working with an unaltered and reliable software file. Here are some techniques to check the file integrity:
1. Antivirus Scan: Before opening or running the downloaded software file, scan it using a reputable antivirus program or malware scanner. Antivirus software can detect and identify any potential malware or viruses that might have been embedded in the file. Running a thorough scan provides an initial layer of security and helps identify any malicious elements.
2. Checksum Verification: Many software developers provide checksum values that you can compare against the downloaded file. Checksums are unique generated strings of numbers and letters based on a specific algorithm. By comparing the checksum provided by the developer with the calculated checksum of the downloaded file using a checksum calculator or verifier, you can ensure that the file has not been modified or corrupted.
3. Hash Verification: Another way to check file integrity is through hash verification. Hash algorithms, such as MD5 or SHA-256, generate a unique hash value for each file. Compare the hash value of the downloaded file with the hash value provided by the developer. If the hash values match, it confirms that the file has remained unaltered during the download process.
4. File Size Comparison: Compare the file size of the downloaded software with the file size mentioned on the official website or by the software developer. If the file sizes differ significantly, it could indicate that the file has been modified or corrupted. In such cases, it is advisable to avoid running or installing the software and instead report the issue to the developer.
5. Digital Signatures: Check if the downloaded software file has a digital signature from the software developer. Digital signatures provide an added layer of security and authenticity. If the file is digitally signed, verify the signature against the developer’s public key or the certificate used to sign the file. This ensures that the file is from the trusted developer and has not been tampered with.
6. Use File Integrity Checkers: File integrity checkers or verification tools can analyze the downloaded file and report any inconsistencies or corruption. These tools calculate hashes or checksums and compare them with the expected values. File integrity checkers can also highlight any changes or modifications made to the file, helping you determine if the file is trustworthy and intact.
7. Re-download the File: If you suspect that the downloaded file may be corrupted or tampered with, consider re-downloading it from the official source. Network issues or incomplete downloads can sometimes result in corrupted files. Downloading the file again ensures that you have a fresh copy and increases the chances of obtaining an unaltered file.
Checking the file integrity of the downloaded software is a crucial step in ensuring that you are working with a reliable and unmodified file. Taking these measures reduces the risk of running or installing compromised software, providing you with greater confidence in the integrity and security of the downloaded file.
Scanning for Malware
Before running or installing downloaded software, it is crucial to scan the file for malware. Malware is a significant threat that can infect your computer, compromise your privacy, and damage your system. By scanning for malware, you can mitigate the risk of downloading and installing malicious software. Here are some important considerations for scanning files for malware:
1. Use a Reputable Antivirus Solution: Install and update a reputable antivirus software solution on your computer. Antivirus programs are designed to detect, quarantine, and remove known malware threats. Ensure that your antivirus software is up to date with the latest virus definitions to provide better protection against emerging threats.
2. Schedule Automatic Scans: Configure your antivirus software to perform regular automatic scans of your computer. Automatic scans ensure that your system is regularly checked for malware, reducing the risk of undetected threats. Schedule scans during periods when your computer is idle to minimize performance impact.
3. On-Demand File Scans: Perform on-demand file scans specifically for the downloaded software file. Most antivirus software allows you to right-click on a file and select the option to scan it. This enables you to scan the specific file you are about to run or install, enhancing your security before interacting with the software.
4. Full System Scan: Conduct regular full system scans as part of your overall cybersecurity routine. Full system scans thoroughly examine all files and directories on your computer, including downloaded software, to identify and remove any malware. Full scans provide a comprehensive check for hidden malware that may have escaped previous scans.
5. Cloud-Based Scanning: Consider using cloud-based malware scanning services. These services leverage a vast database of known malware signatures and behavioral analysis to detect and block malicious files. Cloud-based scanning can provide an additional layer of protection by cross-referencing files with a constantly updated malware database.
6. Enable Real-Time Protection: Activate the real-time protection feature in your antivirus software. Real-time protection continuously monitors your system and scans files as they are accessed, downloaded, or executed. By enabling real-time protection, you can proactively identify and block potentially harmful software before it can cause any damage.
7. Verify Scan Results: Pay attention to the scan results provided by your antivirus software. If any malware is detected, take immediate action to remove or quarantine the infected file. Be cautious of false positives, which occur when legitimate files are mistakenly flagged as malware. In such cases, consult with your antivirus software provider or seek additional opinions to confirm the legitimacy of the file.
8. Keep Software and Virus Definitions Updated: Ensure that both your antivirus software and the virus definitions are regularly updated. Antivirus software relies on virus definitions to identify and detect malware. Regular updates to your antivirus software and virus definitions help protect against the latest threats and enhance the accuracy of scans.
Scanning files for malware is an essential practice to safeguard your computer and personal data. By following these scanning techniques and employing the right antivirus measures, you can significantly reduce the risk of downloading and installing malicious software, ensuring a safer digital experience.
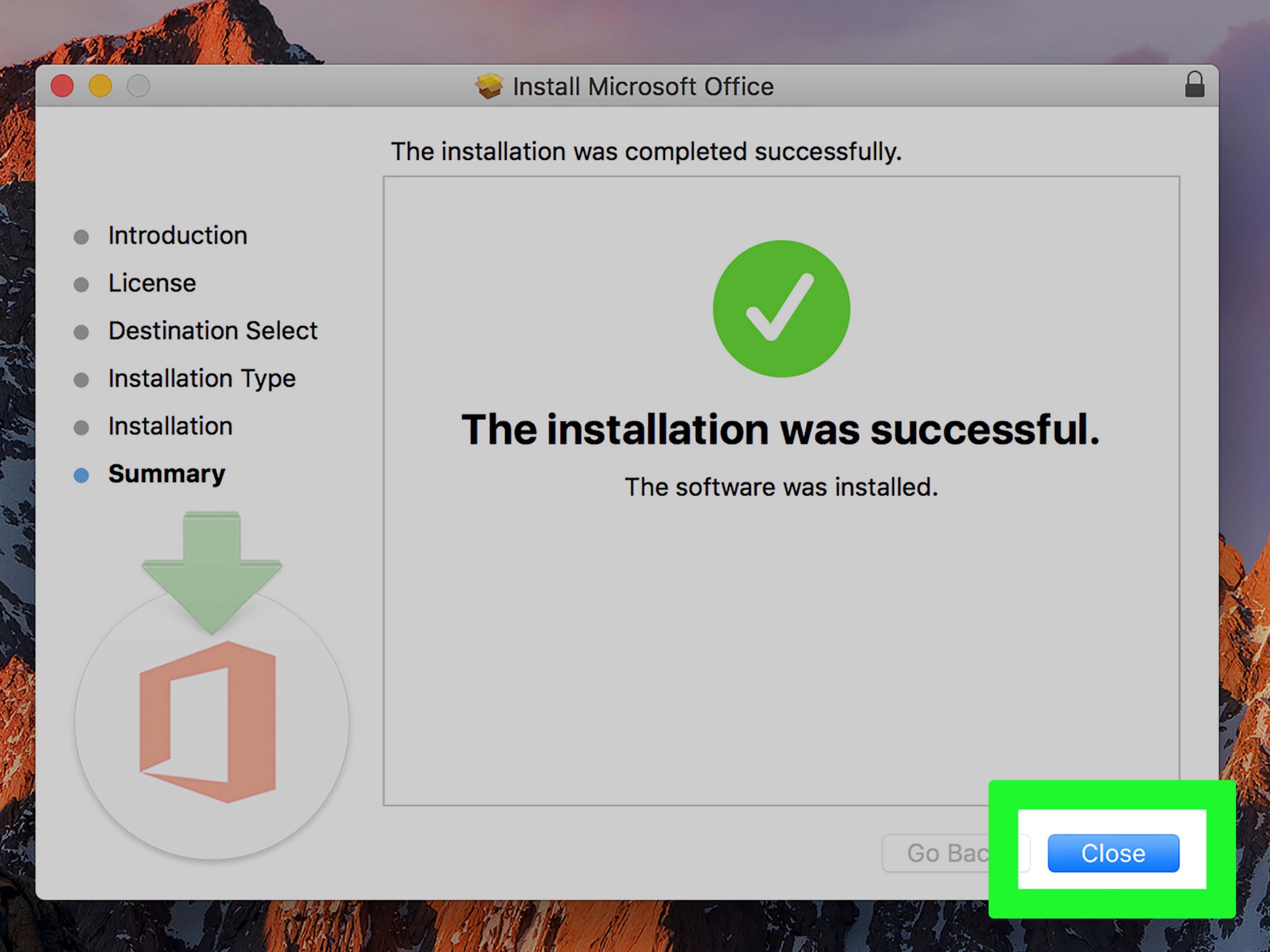
Understanding the Installation Process
Understanding the installation process of software is crucial to ensure a smooth and secure experience. When installing software, it is important to pay attention to the installation steps, confirm the software’s authenticity, and make informed choices regarding additional bundled components. Here are key considerations to understand the installation process:
1. Read Installation Instructions: Carefully read the installation instructions provided by the software developer. The instructions typically outline the necessary steps and precautions to follow during the installation process. By familiarizing yourself with the instructions, you can avoid common installation errors and ensure a successful installation.
2. Verify Software Authenticity: During the installation process, verify that the software being installed is the authentic version obtained from a trusted source. Double-check the software’s digital signature, MD5/SHA checksum, or other verification methods provided by the developer. If any discrepancies or doubts arise, it is recommended to abort the installation and report the issue to the software developer.
3. Choose Custom Installation: Whenever possible, opt for a custom installation rather than a default installation. Custom installations provide more control and allow you to select specific components and options. This eliminates the potential installation of unnecessary or unwanted bundled software that may compromise system performance or security.
4. Review Privacy Settings: Pay attention to the privacy settings and permissions requested during the installation. Some software may ask for unnecessary access to personal data or system resources. Evaluate each permission request and determine if it is necessary for the software to function as intended. If in doubt, limit the permissions or seek additional information from the developer or reputable sources.
5. Decline Additional Offers: Be cautious of additional offers or bundled software that may be presented during the installation process. Often, software developers partner with advertising networks or other companies to include additional programs or toolbars with the main software. Carefully review each offer and deselect any additional components that you do not need or trust.
6. Disable Auto-Updates if Necessary: While it is generally recommended to keep software up to date by accepting automatic updates, there may be situations where disabling auto-updates is preferred. In certain environments, such as mission-critical systems or software with specific compatibility requirements, it may be necessary to carefully manage software updates to avoid any unforeseen issues or disruptions.
7. Review End User License Agreement (EULA): Before proceeding with the installation, read and review the End User License Agreement (EULA). The EULA outlines the terms and conditions under which you are allowed to use the software. Pay attention to any clauses regarding data collection, privacy, and intellectual property rights. If you disagree with the terms outlined in the EULA, it is best to refrain from installing the software.
8. Maintain Backups: Before initiating any software installation, ensure you have a backup of important files and data. This precautionary measure protects against potential issues that may arise during the installation process, such as system crashes or unforeseen data loss. Regularly backing up your data is a best practice that ensures you can recover important information if any problems occur.
Understanding the installation process of software is vital for a secure and hassle-free experience. By following these considerations, you can make informed decisions during the installation process, avoid unnecessary bundled components, and ensure that the software is installed correctly and securely on your system.
Reading the End User License Agreement (EULA)
Reading the End User License Agreement (EULA) is an important step in the software installation process. The EULA outlines the terms and conditions under which you are permitted to use the software. Although it may be tempting to quickly skim through the agreement, taking the time to read and understand the EULA is essential. Here’s why reading the EULA is important:
1. Understanding Usage Rights: The EULA defines your rights and responsibilities as a user of the software. By reading the EULA, you gain a clear understanding of how you can use the software and any restrictions that may apply. This includes details about personal or commercial use, installation limitations, and licensing requirements.
2. Identifying Data Collection Practices: The EULA often outlines the software developer’s data collection and usage practices. Reading the agreement helps you understand what types of data may be collected and how it will be processed. This can include personally identifiable information, usage statistics, or system information. Being aware of these practices allows you to make informed decisions regarding your privacy.
3. Discovering Limitations and Restrictions: The EULA may contain limitations and restrictions on the use of the software. This can include prohibiting reverse engineering, modifying the software’s code, or transferring the license to another user. By reading the EULA, you can ensure that you comply with these limitations, avoiding any potential legal issues.
4. Identifying Termination Clauses: The EULA outlines the conditions under which the software license can be terminated. This can include violations of the agreement, non-payment of licensing fees, or other specified circumstances. Reading the EULA helps you understand the rights of the software developer in terminating the license and any potential consequences for non-compliance.
5. Evaluating Warranty and Liability Terms: The EULA often specifies the software developer’s warranty terms and limitations of liability. By reading this section, you can ascertain what level of support the developer provides, any disclaimers of warranties, and the extent of their responsibility for potential damages. Understanding these terms helps manage your expectations and potential recourse in case of software issues.
6. Assessing Software Updates and Upgrades: The EULA can provide information on the developer’s policy regarding software updates and upgrades. It may outline how updates will be provided, any associated costs, and the developer’s commitment to delivering patches or bug fixes. Understanding the upgrade policy ensures you are aware of any additional expenses and the availability of future software improvements.
7. Potential Legal Consequences: By agreeing to the EULA terms, you enter into a legal contract with the software developer. Failure to comply with the terms of the EULA can have legal consequences. Reading and understanding the EULA allows you to decide whether you are comfortable with the obligations outlined and can help you avoid unintended breaches of the agreement.
8. Making Informed Choices: Ultimately, reading the EULA enables you to make informed choices about whether to proceed with the installation of the software. If you disagree with the terms or are uncomfortable with certain conditions, you have the opportunity to reconsider and potentially explore alternative software options that align more closely with your preferences and requirements.
Reading the End User License Agreement (EULA) is an essential step in the software installation process. By reading and understanding the EULA, you can make informed decisions, protect your rights, and ensure that you comply with the software developer’s terms and conditions.
Customizing the Installation Options
Customizing the installation options during the software installation process allows you to tailor the installation to your specific needs and preferences. By understanding and utilizing the available customization options, you can optimize the software’s functionality, enhance system performance, and avoid installing unnecessary components. Here are key considerations for customizing the installation options:
1. Selecting Installation Location: Many software installation processes give you the option to choose the installation location on your computer. Consider selecting a location that aligns with your preferred directory structure or storage capacity. Choosing a specific location can also help streamline backup and restore processes in the future.
2. Choosing Components: During the installation, you may be presented with options to choose specific components or features to install. Evaluate each component’s usefulness and its impact on system resources. Select only the components that you require to avoid unnecessary clutter and minimize the software’s footprint on your system.
3. Language Selection: If the software offers support for multiple languages, you may have the option to choose the language during the installation process. Select the language that you are most comfortable with or the one that aligns with your primary usage requirements. Choosing the right language ensures a better user experience and ease of use.
4. Startup Preferences: Consider the startup preferences offered during the installation process. Some software may have options to launch the program automatically when you start your computer. Evaluate whether you want the software to start with your system or prefer to launch it manually when needed. Adjusting the startup preferences helps optimize system resources and reduces unnecessary startup delays.
5. Additional Software Offers: Be cautious of additional software offers or bundled components that may be presented during the installation process. Carefully review each offer and consider whether the bundled software or components are necessary and trustworthy. If you do not need or trust the additional offers, opt-out of installing them to ensure a clean and focused software installation.
6. Shortcut Placement: You may have the option to choose where shortcuts and icons will be placed during the installation process. Decide whether you want shortcuts on the desktop, taskbar, or start menu. Customizing the placement of shortcuts allows you to organize your software and access it easily, according to your preferred workflow.
7. Integration with Web Browsers: Certain software installations may offer integration options with web browsers for enhanced functionality. Evaluate whether you require the software to integrate with your web browser or if you prefer to control the integration manually. Sometimes, excessive browser integration can slow down browsing or introduce additional security vulnerabilities.
8. Update and Privacy Settings: During the customization process, review the update and privacy settings offered by the software. Consider enabling automatic updates to ensure you have the latest features, bug fixes, and security patches. Evaluate the privacy settings and adjust them to your preferences, balancing personalization and data collection concerns.
By customizing the installation options, you can optimize your software installation, reduce resource consumption, and tailor the software to your specific needs. Take the time to review and adjust the available options to ensure a streamlined, efficient, and personalized software experience.
Avoiding Potentially Unwanted Programs (PUPs)
When downloading and installing software, it is important to be cautious of Potentially Unwanted Programs (PUPs). PUPs are additional programs or software components that may be bundled with the main software you are downloading. While not necessarily malicious, PUPs can negatively impact system performance, invade privacy, and compromise security. Here are some strategies for avoiding PUPs:
1. Research the Software: Conduct thorough research on the software you intend to download. Read user reviews, visit official forums, and consult technology websites known for unbiased recommendations. Pay attention to any mentions of bundled software or potential PUPs associated with the software. This research helps you make an informed decision and avoid downloading software that may come with unwanted components.
2. Choose Trusted Sources: Download software from trusted and reputable sources. Official software websites, well-known download platforms, and recognized software developers are generally safer options. These sources prioritize user security and tend to minimize the inclusion of PUPs in their software packages. Avoid downloading software from unfamiliar or untrusted sources, as they may be more likely to include unwanted programs.
3. Opt for Custom Installation: During the installation process, choose custom installation instead of the default or express installation. Custom installation options allow you to review and control what components are being installed. It gives you the opportunity to deselect any bundled software or third-party offers that you do not want or trust. Taking the time to review and customize the installation helps you avoid installing PUPs that may be bundled with the software.
4. Read EULA and Privacy Policy: Carefully read the End User License Agreement (EULA) and the privacy policy associated with the software. Pay attention to any clauses that mention bundled software, data collection, or third-party partnerships. These documents can provide insights into the inclusion of PUPs and the developer’s approach to user privacy. If the EULA or privacy policy raises concerns, reconsider installing the software to avoid potential PUPs.
5. Decline Additional Offers: During the installation process, you may encounter additional offers or promotions for unrelated software or services. Be cautious and decline these offers if they are not necessary or from reputable providers. Sometimes, these additional offers can lead to unintentional installation of PUPs. Safeguard your system by being selective and opting out of these offers.
6. Use Ad-Blockers and Anti-Malware Tools: Install ad-blockers and reputable anti-malware tools on your system. Ad-blockers can help prevent potentially misleading or deceptive advertisements that may lead to the download of PUPs. Anti-malware tools can provide real-time protection and actively scan for and remove PUPs that may already be present on your system.
7. Regularly Update Software: Keep your software and security tools up to date. Developers often release updates that address security vulnerabilities and improve overall software performance. Regularly updating your software reduces the risk of PUPs exploiting known vulnerabilities. Additionally, make sure to update your operating system and web browsers to benefit from the latest security patches and features.
8. Stay Vigilant: Exercise caution throughout the software installation process. Pay close attention to the installation steps, read all dialog boxes carefully, and review any pre-selected options. Be wary of websites and installers that use deceptive tactics or aggressive marketing techniques. By staying vigilant, you can avoid PUPs and maintain a secure software environment.
By following these strategies, you can minimize the risk of downloading and installing Potentially Unwanted Programs (PUPs). Being proactive and cautious during the software installation process helps protect your system, privacy, and overall digital experience.
Keeping the Installation Files
Keeping the installation files of the software you download is a recommended practice that offers several benefits. While it may be tempting to delete the installation files after successful installation, retaining them can be advantageous in various situations. Here are key reasons to consider keeping the installation files:
1. Reinstallation and Repair: Having the installation files allows you to reinstall or repair the software if needed. In case of system crashes, software compatibility issues, or corrupted installations, having the original installation files readily available simplifies the process of reinstalling or repairing the software. This saves time and effort, especially when re-downloading large software packages or when an internet connection is unavailable or slow.
2. Customization and Configuration: Retaining the installation files enables you to customize and configure the software further. Some software allows you to modify settings, add plugins or extensions, or customize the user interface. By keeping the installation files, you can easily access and make changes to the software as desired, without having to search for specific versions or editions online.
3. Downgrading or Switching Versions: In certain cases, you may need to downgrade or switch to a previous version of the software. This can be due to compatibility issues with other programs, preference for a previous user interface, or a specific requirement. With the installation files on hand, you can uninstall the current version and install the desired older version without the hassle of searching or relying on potentially less reputable sources.
4. Moving to a Different System: If you acquire a new computer or need to install the software on a different device, having the installation files readily available simplifies the process. Instead of searching for the software online and potentially encountering different versions or sources, you can copy the installation files directly from your storage device and easily install the software on the new system.
5. Temporary Installation: In some scenarios, you may only need to temporarily install the software. This could be for testing purposes, one-time usage, or in a virtual environment. By keeping the installation files, you can simply run the installer whenever needed and uninstall the software when no longer required, without the need to download it again.
6. Offline Installation: In situations where internet access is limited or unavailable, having the installation files is invaluable. You may need to install the software on multiple devices or in remote locations where reliable internet connectivity is not accessible. By keeping the installation files stored locally or on a portable storage device, you can perform installations offline without dependency on an internet connection.
7. Archiving and Documentation Purposes: Keeping the installation files can serve as part of your software and system documentation. By organizing and archiving the installation files, you create a reference for the specific versions of the software you have installed. This documentation can be useful for future reference, audits, or troubleshooting purposes.
8. Security Considerations: In some cases, software developers may remove or modify versions of their software over time. By keeping the installation files, you have a preserved copy of the software and can ensure you are using the exact version that you downloaded initially. This helps maintain software integrity and avoid unwittingly using compromised or altered versions from less reputable sources.
By preserving the installation files of the software you download, you can easily perform reinstalls, repairs, customizations, and version switches as needed. Retaining these files offers convenience, flexibility, and peace of mind by ensuring you have reliable access to the software you have downloaded in its original form.
Using a Virtual Machine
Using a virtual machine (VM) is a helpful strategy for running software in a secure and isolated environment. A virtual machine emulates a complete computer system within your physical computer, allowing you to run different operating systems and applications without affecting your main system. Here are the benefits of using a virtual machine:
1. Enhanced Security: Running software in a virtual machine provides an added layer of security. Since the virtual machine is isolated from the host operating system, any malware or security vulnerabilities within the software are contained within the virtual machine and do not affect the main operating system. This minimizes the risk of infecting your primary system with malware or compromising its security.
2. Sandboxing Environment: A virtual machine serves as a sandboxing environment, isolating the software from your main system. This isolation prevents the software from accessing and modifying critical system files, personal data, or other applications running on your computer. If the software behaves maliciously or causes system instability, it will impact only the virtual machine and not your main operating system.
3. Compatibility Testing: Virtual machines are particularly useful for compatibility testing. You can run the software on different virtual machines with different operating systems and configurations to ensure it functions correctly across various environments. This helps identify any compatibility issues early on and avoid potential problems when deploying the software on different systems.
4. Easy Setup and Configuration: Setting up a virtual machine is relatively straightforward and does not require physical hardware or separate partitions. Virtualization software, such as VirtualBox or VMware, provides user-friendly interfaces for creating and managing virtual machines. Additionally, you can create snapshots or clones of virtual machines, allowing you to quickly revert to a previous state or clone a preconfigured environment for other purposes.
5. Isolation of Development Environments: Running software in a virtual machine makes it easier to set up and manage isolated development environments. You can create a dedicated virtual machine with all the necessary software tools, libraries, and configurations specific to your development needs. This isolation ensures that your development environment remains separate from your main system configuration, reducing conflicts and potential disruptions.
6. Simplified Software Testing: Virtual machines enable efficient software testing. You can create multiple virtual machines with different operating systems and software versions to test the software’s compatibility and performance across various configurations. Testing in virtual machines provides a controlled environment where you can easily replicate different testing scenarios without impacting your main system.
7. Resource Management: Virtual machines offer flexibility in managing system resources. You can allocate specific amounts of CPU, memory, and disk space to each virtual machine, ensuring that the software receives the necessary resources for optimal performance. This resource allocation allows you to run multiple virtual machines simultaneously for different software or testing purposes without straining your main system’s resources.
8. Cost-Effective Solution: Using a virtual machine eliminates the need for additional physical hardware. Instead of setting up separate physical computers or dedicating separate hardware partitions, virtual machines utilize the resources of your existing computer. This cost-effective approach allows you to run software in isolated environments without the expense of acquiring and maintaining separate hardware devices.
By leveraging virtual machines, you can enhance security, create isolated environments, simplify software testing, and efficiently manage system resources. Employing virtual machines offers flexibility, convenience, and peace of mind when running software in a controlled and secure environment.
Regularly Updating Software
Regularly updating software is a crucial practice that helps ensure the security, stability, and functionality of the programs installed on your computer. Software updates often include bug fixes, performance improvements, and most importantly, security patches that address vulnerabilities. Here are the benefits and importance of regularly updating software:
1. Patching Security Vulnerabilities: Software updates frequently include fixes for security vulnerabilities that have been identified since the software’s release. Cybercriminals actively search for and exploit these vulnerabilities to gain unauthorized access to systems, steal data, or propagate malware. Regular software updates patch these vulnerabilities and keep your system protected from potential attacks.
2. Enhanced Stability and Reliability: Updates often include bug fixes and performance optimizations that improve the stability and reliability of the software. Bug fixes address issues that can cause crashes, freezes, or unexpected behavior, leading to a more pleasant and efficient user experience. Regular updates ensure that you are running the latest stable version of the software, reducing the likelihood of encountering software-related problems.
3. Compatibility with New Technologies: Technology evolves rapidly, and software updates are designed to keep up with the latest developments. Regularly updating software ensures compatibility with new operating systems, hardware, and technologies. This compatibility ensures that your software continues to function properly and maximizes its potential in the ever-changing technological landscape.
4. Access to New Features and Improvements: Software updates often introduce new features, enhancements, and improvements that can enhance your user experience and productivity. Developers continuously work on refining and expanding the software’s capabilities based on user feedback and industry trends. Regular updates ensure that you have access to the latest features and improvements, allowing you to take advantage of the software’s full potential.
5. Protection from Emerging Threats: Cyber threats are constantly evolving, and new forms of malware and other digital risks emerge regularly. Software updates help protect against these emerging threats by incorporating advanced security measures and responding to the latest attack techniques. Regularly updating software ensures that you have the best line of defense against the latest cyber threats.
6. Compliance with Licensing and Regulatory Requirements: Some software updates may include compliance-related changes to meet industry standards, legal requirements, or licensing agreements. Staying up-to-date with software updates ensures that you are compliant with these requirements, avoiding legal complications and compatibility issues.
7. Improved Software Performance: Software updates often include performance optimizations that enhance the software’s speed, efficiency, and resource usage. Updates can address memory leaks, streamline code execution, or optimize resource allocation, resulting in faster and smoother software performance. Regular updates ensure that you are benefiting from these performance enhancements and enjoying an optimal user experience.
8. Simplified Support and Troubleshooting: Running the latest version of software simplifies support and troubleshooting processes. If you encounter any issues or seek assistance, support teams are more likely to provide assistance for the latest software versions. Outdated software may receive limited support, and your issues may have already been addressed in later updates. Regularly updating your software makes it easier to receive timely and effective support when needed.
Regularly updating software is crucial for maintaining the security, stability, and performance of your computer systems. By staying up-to-date with software updates, you ensure that you benefit from the latest features, bug fixes, and security enhancements, ultimately improving your overall computing experience.
Reporting Suspicious or Malicious Software
Reporting suspicious or malicious software is an important step to help protect yourself and others from potential cyber threats. By reporting any suspicious or malicious software, you contribute to the collective effort of cybersecurity professionals, software developers, and law enforcement agencies in combating digital risks. Here’s why reporting such software is important:
1. Prevention of Further Harm: Reporting suspicious or malicious software prevents further harm to other users. By alerting relevant authorities and software developers, you enable them to take immediate action, such as investigating the source of the software, analyzing its behavior, identifying associated threats, and developing mitigations or solutions. This can ultimately prevent others from falling victim to the same threats.
2. Timely Response and Investigation: Reporting suspicious or malicious software ensures that cybersecurity professionals and software developers are aware of the issue and can prioritize its investigation. Prompt action leads to faster identification and analysis of emerging threats, allowing for the development of effective countermeasures and security patches. Early reporting ensures timely response, minimizing the impact of the software on users.
3. Identification of New Threats and Attack Techniques: Reporting suspicious or malicious software helps identify new and evolving threats and attack techniques. Cybercriminals are continually adapting their tactics to evade detection and compromise systems. By reporting unusual or suspicious software behavior, you contribute to the identification of new attack vectors and patterns, leading to the development of better defenses and more robust security measures.
4. Collaboration Among Security Professionals: Reporting suspicious or malicious software fosters collaboration among security professionals, software developers, and law enforcement agencies. Sharing information and knowledge about emerging threats improves the collective ability to detect, investigate, and combat cybercrime. Collaboration enables the aggregation of insights and expertise to tackle complex cybersecurity challenges more effectively.
5. Protecting Personal and Sensitive Information: Reporting suspicious or malicious software helps protect personal and sensitive information from unauthorized access or misuse. Cybercriminals often use malware, ransomware, or other malicious software to compromise systems and steal valuable data. Reporting such software ensures that necessary measures are taken to secure systems, mitigate the impact, and protect the confidentiality, integrity, and availability of sensitive information.
6. Legal and Regulatory Compliance: Reporting suspicious or malicious software can help fulfill legal and regulatory obligations. Many jurisdictions require reporting of cybersecurity incidents, particularly those involving personal data breaches or financial fraud. By reporting suspicious or malicious software, you contribute to compliance with relevant laws and regulations, which can help prevent legal consequences for individuals and organizations.
7. Assistance in Catching Cybercriminals: Reporting suspicious or malicious software can aid in catching cybercriminals. Information provided through the reporting process, such as the software’s source, associated email addresses, or IP addresses, can help law enforcement agencies investigate and track down those responsible. This increases the chances of identifying and bringing cybercriminals to justice.
8. Building Safer Digital Environments: Reporting suspicious or malicious software contributes to the overall safety and security of digital environments. It promotes awareness and a collaborative effort to protect individuals, organizations, and critical infrastructure from cyber threats. By reporting and addressing suspicious or malicious software promptly, we work towards creating safer digital ecosystems for everyone.
Reporting suspicious or malicious software plays a pivotal role in combating cyber threats and protecting users. By promptly reporting such software, you aid in the prevention, investigation, and mitigation of cyber risks, ultimately contributing to a safer and more secure digital world.