Symptoms of Yahoo Malware
Malware can cause significant issues for your computer, compromising its security and overall performance. If you suspect that your system has been affected by Yahoo malware, it is crucial to be aware of the telltale signs and symptoms. By recognizing these symptoms, you can take immediate action to remove the malware and restore your computer’s safety.
Here are some common symptoms to look out for:
- Unwanted Browser Redirects: One of the primary signs of Yahoo malware is frequent and unexpected browser redirects. You may find yourself being redirected to unfamiliar websites, particularly those containing suspicious or malicious content. These redirects can severely disrupt your browsing experience and expose your computer to further risks.
- Changes in Search Engine Settings: If you notice sudden changes in your browser’s default search engine, homepage, or new tab settings that you did not make, it could be a sign of Yahoo malware. Malware often manipulates these settings to redirect your search queries to compromised search results or ads.
- Pop-up Advertisements: Malware is notorious for causing an influx of invasive and persistent pop-up ads. These ads may appear even when you are not actively using your browser and can hinder your online activities. If you find yourself constantly bombarded with pop-ups, especially those related to Yahoo, it could indicate the presence of Yahoo malware on your system.
- Slow Performance: Malware can significantly slow down your computer’s performance by consuming system resources. If you notice a sudden decrease in your computer’s speed and responsiveness, it could be a result of Yahoo malware. Pay attention to any unusual delays when launching programs, opening files, or accessing websites.
- Disabled Antivirus and Security Features: Some malware strains, including those related to Yahoo, can disable or manipulate your antivirus and security software. If you find that your antivirus program is unable to run or update, or that your firewall settings have been altered without your consent, it may indicate the presence of Yahoo malware.
It is important to remember that these symptoms can vary depending on the specific malware strain and its capabilities. Therefore, it is advisable to regularly scan your computer for malware and keep your security software up to date to prevent and detect any potential threats.
Steps to Identify Yahoo Malware
Identifying Yahoo malware on your computer can be challenging as it often disguises itself and operates covertly. However, there are several steps you can take to help identify the presence of Yahoo malware and protect your system from further harm. Here’s what you can do:
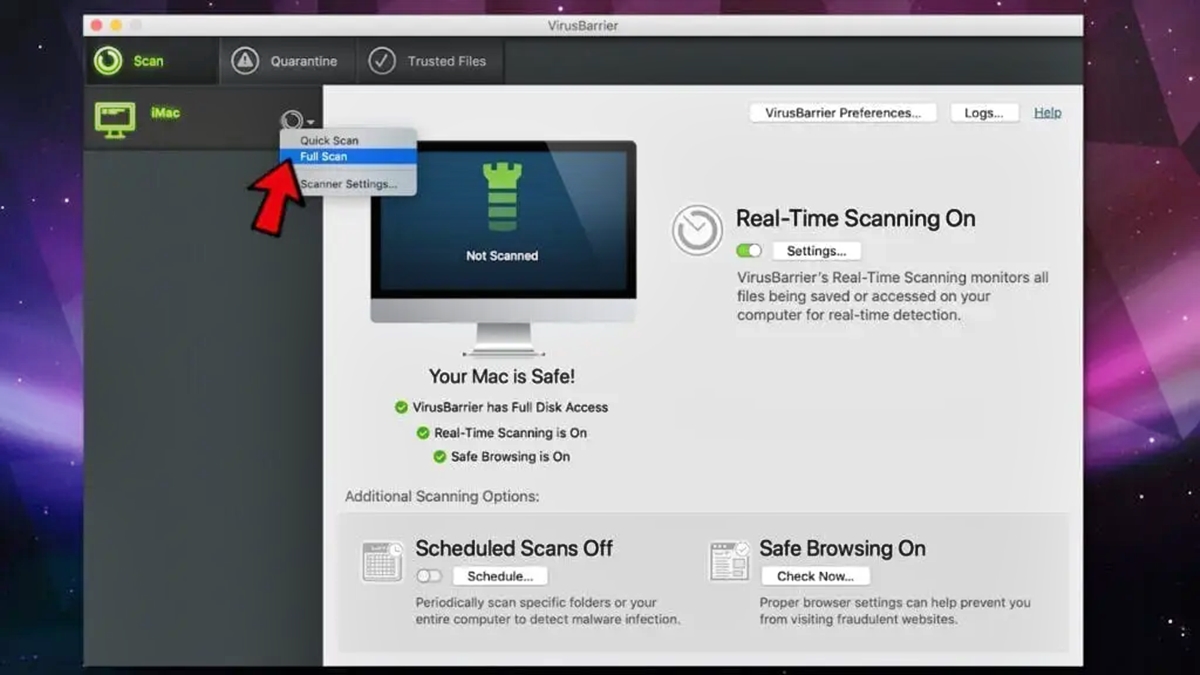
- Perform Full System Scan: Begin by running a full system scan using reputable antivirus software. Make sure to update the virus definitions to ensure your antivirus program can detect the latest threats. If the scan detects any suspicious files or programs related to Yahoo malware, follow the software’s instructions to quarantine or remove them.
- Check Browser Extensions: Yahoo malware often affects web browsers by installing malicious extensions without your knowledge. Open your browser’s extension or add-on manager and review the installed extensions carefully. If you find any unfamiliar or suspicious extensions, remove them immediately to eliminate potential sources of Yahoo malware.
- Monitor Network Traffic: Use a network monitoring tool to track your computer’s incoming and outgoing network traffic. Look for any unusual or suspicious connections, particularly those related to Yahoo. If you notice any unauthorized or suspicious network activity, it may indicate the presence of Yahoo malware.
- Analyze Unusual Behavior: Pay attention to any unusual behavior exhibited by your computer. This includes unexpected system crashes, freezes, excessive bandwidth usage, or programs launching automatically. These irregularities may be indicators of Yahoo malware and require further investigation.
- Review System Performance: Continuously monitor the performance of your computer. Keep an eye out for sudden declines in performance, increased resource usage, or unexplained background processes. Yahoo malware often consumes system resources and can significantly affect your computer’s overall performance.
Remember that identifying Yahoo malware may require a combination of these steps, as well as additional techniques tailored to your specific operating system and software. It is essential to stay vigilant and regularly check for any signs of malware to ensure the security and integrity of your computer system.
Removing Yahoo Malware Manually
Removing Yahoo malware manually can be a complex and time-consuming process. It is important to proceed with caution and follow these steps carefully to ensure the thorough removal of the malware from your system:
- Disable System Restore: Before removing Yahoo malware, disable the System Restore feature on your computer. This is important as malware often hides in system restore points, which can potentially reinfect your system after removal.
- Enter Safe Mode: Restart your computer and enter Safe Mode. This will prevent any malicious processes from running and make it easier to detect and remove Yahoo malware. To enter Safe Mode, press the F8 key repeatedly during the startup process and select the Safe Mode option.
- Uninstall Suspicious Programs: Open the Control Panel and navigate to the “Programs” or “Add/Remove Programs” section. Look for any unfamiliar or suspicious programs, especially those related to Yahoo, and uninstall them. Be thorough in your search and remove any unwanted software or toolbars that may have been installed without your consent.
- Delete Malicious Files and Folders: Use the Windows File Explorer or Finder on Mac to search for and delete any traces of Yahoo malware. Look for suspicious files and folders in your system directories, particularly in the “Program Files” or “Applications” folders.
- Modify Browser Settings: Open your web browser and navigate to the settings menu. Remove any unfamiliar or suspicious search engines, homepages, or extensions. Resetting your browser to its default settings can help eliminate any modifications made by Yahoo malware.
- Clear Browser Data: Remove any cookies, caches, and browsing history associated with Yahoo malware. This helps ensure that no residual data remains that may reinfect your system. Consult your browser’s settings or preferences menu to find the options for clearing this data.
Keep in mind that manual removal methods can be challenging and may not guarantee the complete eradication of Yahoo malware. It is recommended to combine manual removal with reliable and updated antivirus software to maximize the effectiveness of the removal process.
Using Antivirus Software to Remove Yahoo Malware
One of the most effective ways to remove Yahoo malware from your computer is by using reputable antivirus software. Antivirus software is specifically designed to detect, quarantine, and remove various types of malware, including Yahoo malware. Here are the steps to use antivirus software to remove Yahoo malware:
- Choose a Reliable Antivirus Software: Research and select a trusted antivirus software that offers real-time protection, regular updates, and a comprehensive malware removal feature. Popular options include Norton, McAfee, Avast, and AVG.
- Install and Update the Software: Download and install the antivirus software on your computer. After installation, make sure to update the virus definitions to ensure that the software can detect the latest threats, including Yahoo malware.
- Perform a Full System Scan: Launch the antivirus software and initiate a full system scan. This will thoroughly check all files, programs, and processes on your computer for any signs of Yahoo malware. Allow the scan to complete, as it may take some time depending on the size of your hard drive.
- Review the Scan Results: Once the scan is complete, review the scan results provided by the antivirus software. It will indicate whether any Yahoo malware or related threats have been detected. Take note of the identified malware for further action.
- Quarantine or Remove the Malware: Most antivirus software allows you to quarantine or remove the detected malware. Quarantining isolates the malware, preventing it from causing any further harm, while removing completely deletes the malware from your system. Follow the prompts provided by the antivirus software to take the appropriate action.
- Rescan Your System: After quarantining or removing the Yahoo malware, perform another full system scan to ensure that your computer is clean. This additional scan helps to confirm the effectiveness of the removal process and detect any residual traces of malware.
Remember to regularly update your antivirus software and run scheduled scans to proactively detect and remove any future malware threats, including Yahoo malware. It is vital to use a reputable and up-to-date antivirus software to provide ongoing protection to your computer.
Updating Your Browser and Plugins
Keeping your web browser and plugins up to date is an essential step in maintaining a secure and malware-free browsing experience. Outdated browsers and plugins can have vulnerabilities that can be exploited by malware, including Yahoo malware. Follow these steps to update your browser and plugins:
- Check for Browser Updates: Open your web browser and navigate to the settings or preferences menu. Look for the option to check for updates. If an update is available, follow the prompts to download and install the latest version of your browser. Regularly checking for updates ensures that you have the latest security patches and fixes.
- Enable Automatic Updates: To streamline the update process, enable automatic updates for your browser. This ensures that you receive the latest updates without having to manually check for them. Consult your browser’s settings or preferences menu to enable this feature.
- Update Plugins and Extensions: Many browser plugins or extensions, such as Adobe Flash Player, Java, or Silverlight, can also pose security risks if they are outdated. Check for updates for these plugins and install any available updates. If you no longer use a particular plugin, consider removing it to reduce potential vulnerabilities.
- Remove Unnecessary Plugins: Review the list of installed plugins or extensions and remove any that you no longer use or recognize. Unnecessary plugins can increase the risk of malware infections and slow down your browsing experience.
- Consider Plugin Security Settings: Some browsers allow you to adjust the security settings for individual plugins. Review these settings and make sure they are appropriately configured to enhance your browser’s security.
By regularly updating your web browser and plugins, you can take proactive steps to prevent Yahoo malware and other malware infections. Remember to also enable automatic updates and periodically check for updates manually to ensure you have the latest protection and security enhancements.
Resetting Browser Settings
If you suspect that your browser has been affected by Yahoo malware or if you experience persistent issues despite other troubleshooting steps, resetting your browser settings can help eliminate any unwanted changes and restore your browser to its default state. Here’s how to reset your browser settings:
- Backup Important Data: Before resetting your browser, back up any important data, such as bookmarks, saved passwords, or browsing history. This ensures that you don’t lose any valuable information during the reset process.
- Access Browser Settings: Open your browser and navigate to the settings or preferences menu. Look for the option to reset or restore settings. The location and wording may vary depending on the browser you are using.
- Choose Reset Options: Depending on the browser, you may have different options for resetting your browser settings. Consider selecting options that reset your homepage, search engine preferences, disable extensions, and clear browsing data.
- Confirm the Reset: Confirm your selection to reset your browser settings. Keep in mind that this action will remove any customizations you have made to your browser and revert it to its default configuration.
- Restart Your Browser: After resetting your browser settings, close and restart your browser to apply the changes. You may need to reconfigure certain preferences and re-login to websites if necessary.
- Review Browser Extensions: Once your browser has restarted, review the extensions or plugins installed. Remove any suspicious or unwanted extensions that could be causing or contributing to the Yahoo malware issue.
Resetting your browser settings can help eliminate the presence of Yahoo malware and restore your browser’s functionality. However, keep in mind that this process may not completely remove all traces of malware. It is recommended to combine this step with other malware removal methods, such as using antivirus software or performing manual scans, for a more comprehensive approach.
Clearing Browser Cookies and Caches
Clearing your browser’s cookies and caches can help resolve various issues caused by Yahoo malware and improve your browser’s performance. Cookies are small files stored by websites on your computer, while caches store temporary data to speed up page loading. To clear them, follow these steps:
- Access Browser Settings: Open your browser and go to the settings or preferences menu. Look for the option related to privacy or browsing data.
- Select Clear Browsing Data: Depending on your browser, you may encounter different terminology, such as “Clear browsing data,” “Clear browsing history,” or “Manage cookies and site data.” Click on the appropriate option.
- Choose Data to Clear: In the dialog box that appears, select the types of data you want to clear. This typically includes cookies, caches, browsing history, and other temporary internet files. Consider selecting the appropriate time range to clear data from a specific time period.
- Clear the Data: Confirm your selection and initiate the clearing process. Depending on the amount of data to be cleared and your computer’s performance, this process may take a few moments.
- Restart Your Browser: Once the data is cleared, close and reopen your browser to apply the changes. Websites you visit will no longer have access to any stored cookies, and caches will be cleared, ensuring a clean browsing experience.
- Review Privacy Settings: After clearing cookies and caches, take a moment to review your browser’s privacy settings. Consider adjusting settings related to cookie preferences, third-party cookies, or site data storage to enhance your privacy and protect against future Yahoo malware infections.
Regularly clearing your browser’s cookies and caches not only helps to remove any traces of Yahoo malware but also improves your browsing speed and privacy. However, keep in mind that clearing cookies may log you out of websites and remove any stored preferences, so be prepared to re-enter login credentials and customize settings as needed.
Preventing Future Yahoo Malware Infections
Preventing future Yahoo malware infections is essential to maintain the security and integrity of your computer. By following these proactive measures, you can significantly reduce the risk of encountering Yahoo malware or any other type of malware:
- Keep Software Updated: Regularly update your operating system, web browsers, and plugins to ensure they have the latest security patches and bug fixes. Enable automatic updates where possible to streamline the process.
- Use Reliable Antivirus Software: Install reputable antivirus software and keep it updated. Run regular scans to detect and remove any malware threats, including Yahoo malware. Consider using real-time protection features for continuous monitoring.
- Exercise Caution with Email Attachments and Downloads: Be cautious when opening email attachments or downloading files from the internet. Only download files from trusted sources and avoid interacting with suspicious or unsolicited emails, as they can contain malware.
- Be Wary of Phishing Attempts: Stay vigilant against phishing attempts, as they can lead to Yahoo malware infections. Avoid clicking on suspicious links or providing personal information to unknown sources. Verify the authenticity of emails, websites, and requests before taking action.
- Enable Firewall Protection: Activate the built-in firewall on your computer or install a reliable firewall software. Firewalls act as a barrier between your computer and potential intruders, blocking unauthorized access and preventing malware infections.
- Be Mindful of Social Engineering Techniques: Be aware of social engineering techniques used to trick users into downloading or executing malicious programs. Exercise caution when interacting with unexpected pop-ups, advertisements, or requests for personal information.
- Practice Safe Browsing Habits: Avoid visiting suspicious websites, engaging in illegal or unethical activities, or downloading pirated software. Stick to reputable websites and exercise caution when clicking on links or downloading files.
- Regularly Backup Your Data: Back up your important files and data regularly to an external hard drive, cloud storage, or a reliable backup service. In the event of malware or other issues, having a recent backup ensures you can recover your data without paying ransom or experiencing data loss.
- Educate Yourself and Stay Informed: Stay up to date with the latest news on malware threats and security practices. Educate yourself about common malware techniques and how to recognize and avoid them. Regularly visit trusted cybersecurity websites and follow reputable security experts for insights and recommendations.
By adopting these preventive measures and maintaining good cybersecurity habits, you can greatly reduce the risk of encountering Yahoo malware or any other malware. Remember that staying proactive and cautious is key to keeping your computer and personal information safe from cyber threats.