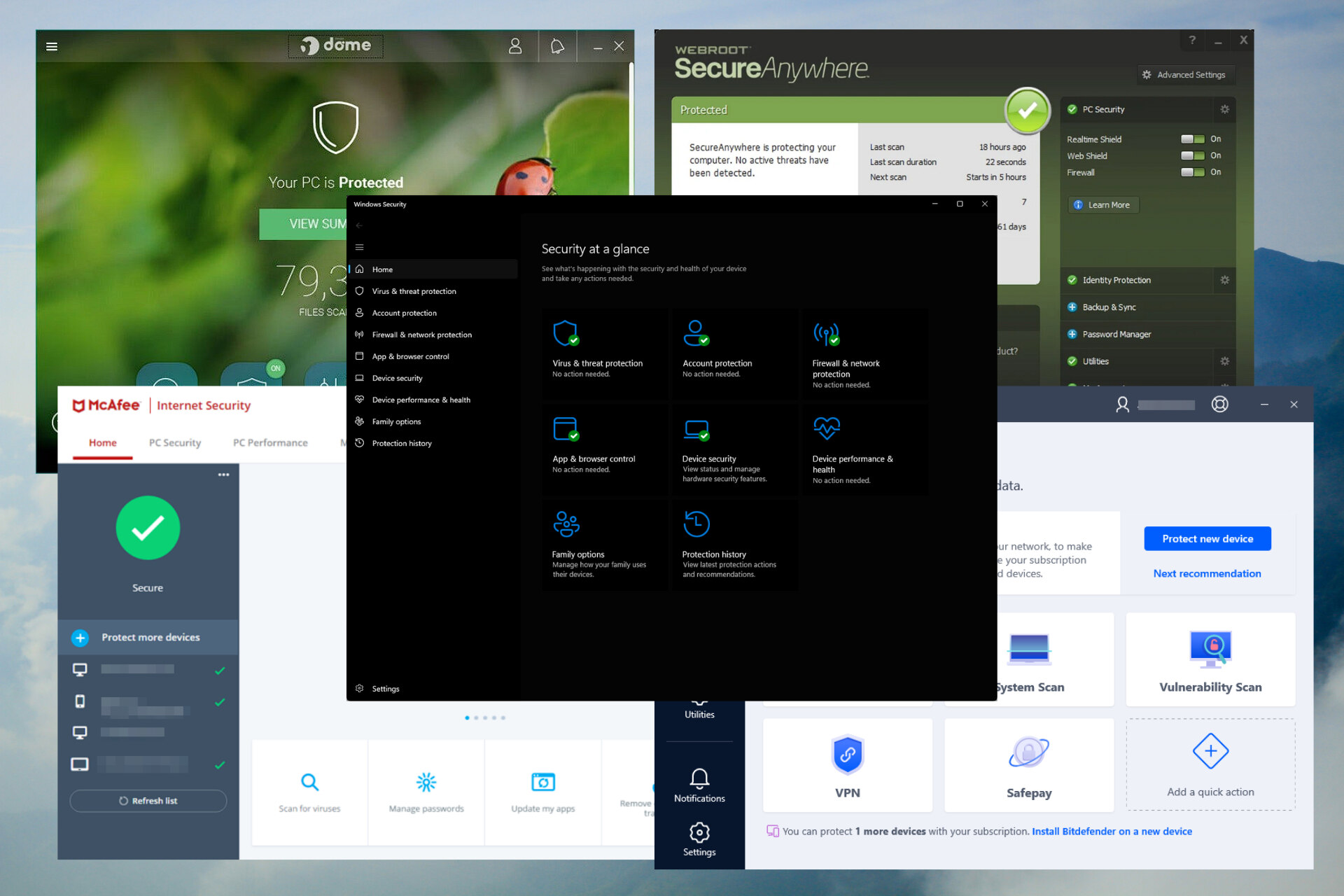
Protect your devices with antivirus software
In today’s digital age, protecting your devices from malware and other online threats is of utmost importance. One of the most effective ways to safeguard your devices is by using antivirus software. Antivirus software not only detects and removes malicious software but also prevents infections from occurring in the first place. Here are some key reasons why you should always have antivirus software installed:
- Real-time threat detection: Antivirus software continuously monitors your device for any suspicious activities or files. It scans incoming and outgoing data to identify and block any potential threats, ensuring that your device remains safe.
- Malware protection: Antivirus software provides protection against various types of malware, such as viruses, worms, Trojans, ransomware, and spyware. It detects and removes these malicious programs from your device, preventing them from causing harm or stealing your sensitive information.
- Web protection: Antivirus software often comes with web protection features that shield you from dangerous websites and malicious links. It can identify phishing websites, fraudulent online platforms, and unsafe downloads, keeping you safe while browsing the internet.
- Automatic updates: Antivirus software regularly updates its virus definitions to stay current with the latest threats. These updates ensure that the software can effectively detect and neutralize new and emerging malware, providing you with optimal protection.
- Performance optimization: Many antivirus programs also include system optimization tools that help improve the performance of your device. These tools clean up unnecessary files, optimize system settings, and remove any performance-draining elements, resulting in a faster and more efficient device.
With the increasing number of complex cyber threats, relying solely on the built-in security features of your operating system might not be enough. Investing in reputable antivirus software is an essential step towards protecting your devices and ensuring your online safety. It is important to choose a reliable and trusted antivirus solution from reputable vendors. Regularly updating the software and running scheduled scans will ensure that your devices are protected from the latest threats.
Utilize strong and unique passwords
In today’s interconnected world, where passwords are the keys to our digital lives, using strong and unique passwords is crucial in protecting your sensitive information from unauthorized access. Here are some important reasons why you should prioritize using strong and unique passwords:
- Protect against password cracking: Weak passwords are easy targets for hackers using techniques like brute force attacks or dictionary attacks. By creating strong and complex passwords, you make it exponentially more difficult for attackers to crack them.
- Safeguard multiple accounts: Many individuals have multiple online accounts, including email, social media, and online banking. By using unique passwords for each account, you minimize the risk of a security breach. If one account is compromised, the others remain secure.
- Prevent credential stuffing: Cybercriminals often obtain lists of compromised usernames and passwords from data breaches and attempt to use them on multiple websites. By using unique passwords, you significantly reduce the chances of falling victim to credential stuffing.
- Combine complexity and memorability: Create passwords that are both complex enough to withstand hacking attempts and memorable enough so you don’t have to write them down. Consider using a combination of uppercase and lowercase letters, numbers, and special characters.
- Consider password managers: If remembering multiple complex passwords is challenging, consider using a password manager. These tools securely store your passwords, generate strong ones for you, and automatically fill them in when you need to log in.
Keep in mind that using strong and unique passwords is just one part of the equation. It is equally important to regularly update passwords, especially after any security breaches. Avoid using easily guessable passwords, such as common phrases, birthdates, or sequential numbers. Instead, opt for a mix of random words, numbers, and symbols that do not contain personally identifiable information.
Remember, the security of your online accounts and the protection of your personal information are in your hands. Take the time to create strong and unique passwords for all your accounts, and consider implementing additional security measures like two-factor authentication for an added layer of protection.
Enable two-factor authentication
In today’s digital landscape, where data breaches and online threats are on the rise, relying solely on passwords for account security is no longer enough. Two-factor authentication (2FA) provides an extra layer of protection by requiring users to provide additional verification alongside their password. Here’s why enabling 2FA is vital:
- Enhanced security: With 2FA, even if your password is compromised, an attacker would still require access to your secondary authentication method, such as a unique code sent to your mobile device, to gain entry to your account. This significantly reduces the likelihood of unauthorized access to your sensitive information.
- Protection against phishing attacks: 2FA adds an additional security step that phishing attacks can’t easily bypass. Even if you accidentally provide your username and password on a fraudulent website, the attacker would still need access to your second-factor authentication code to gain entry.
- Multiple authentication options: 2FA solutions offer various options for the second-factor authentication, including SMS codes, email verification, authenticator apps, and physical security keys. Choose the method that suits your preferences and provides the highest level of convenience and security.
- Applicable across multiple platforms: Many online services now offer 2FA as an option, including social media platforms, email providers, financial institutions, and more. By enabling 2FA across these platforms, you add an extra layer of protection to all your accounts.
- Quick and easy setup: Setting up 2FA is a straightforward process, and most online services provide step-by-step instructions. It usually involves linking your account to a phone number or authenticator app, and from then on, you’ll be prompted to enter the secondary authentication code whenever you log in.
Enabling 2FA is a crucial step in strengthening the security of your online accounts and protecting your personal information. While it may introduce a minor inconvenience during login, the added layer of security is well worth it. Take the time to enable 2FA on all the platforms that offer this feature, and regularly review and update your authentication methods to ensure optimal security.
Be cautious of phishing scams
Phishing scams are a prevalent and dangerous form of cyberattacks that aim to trick individuals into providing their sensitive information, such as usernames, passwords, and financial details. Falling victim to a phishing scam can lead to identity theft, financial loss, and other forms of cybercrime. Here are some essential tips to help you stay cautious and protect yourself from phishing scams:
- Be vigilant of suspicious emails: Phishing emails often appear to be from trustworthy sources like banks, social media platforms, or government agencies. However, they may contain grammatical errors, ask for sensitive information, or use urgent language to create a sense of urgency. Always double-check the sender’s email address and be skeptical of unexpected requests or offers.
- Avoid clicking on suspicious links: Phishing emails often contain links that lead to fake websites designed to steal your information. Hover over the links to see the actual URL and ensure it matches the legitimate site. Instead of clicking on links in emails, manually type in the website address to access your accounts.
- Protect personal information: Legitimate organizations typically don’t ask for personal or financial information via email. Be cautious of emails requesting account numbers, passwords, or social security numbers. If you receive such a request, contact the organization directly through their official website or phone number to verify the authenticity of the request.
- Stay updated with security software: Install reputable security software that includes anti-phishing features. These tools can help detect and block known phishing websites and malicious links, providing an additional layer of protection against phishing attempts.
- Keep your operating system and software up to date: Regularly update your devices, operating systems, and applications to ensure you have the latest security patches in place. Phishing attacks often exploit vulnerabilities in outdated software, so staying up to date reduces the risk of falling victim to phishing scams.
- Educate yourself and others: Stay informed about the latest phishing tactics and scams. Share these insights with friends, family, and colleagues to help them stay cautious and avoid becoming victims. Remember, cybersecurity is a collective effort.
By being cautious, attentive, and informed, you can greatly reduce the risk of falling victim to phishing scams. Always trust your instincts and err on the side of caution when faced with suspicious emails or messages. Remember, legitimate organizations will never ask you to provide sensitive information via email, so stay vigilant and protect your personal and financial well-being.
Keep your software and operating systems up to date
Regularly updating your software and operating systems is a critical aspect of maintaining a secure digital environment. Software updates, often referred to as patches or security updates, provide essential bug fixes, performance enhancements, and most importantly, security patches that protect your devices from known vulnerabilities. Here are some key reasons why you should prioritize keeping your software and operating systems up to date:
- Protection against security vulnerabilities: Hackers are constantly evolving their techniques to exploit weaknesses in software and operating systems. By staying up to date with patches and updates, you ensure that known vulnerabilities are patched, minimizing the risk of potential security breaches.
- Defense against malware and cyber threats: Outdated software is more susceptible to malware attacks, as cybercriminals often target known vulnerabilities. Keeping your software up to date strengthens your device’s defenses against various types of malware, such as viruses, ransomware, and spyware.
- Bug fixes and performance improvements: Software updates not only address security issues but also fix bugs and improve the overall performance of the application or operating system. By installing updates, you can benefit from enhanced features and smoother user experiences.
- Stay compatible with new technologies: New technologies and standards emerge regularly, and software updates ensure that your devices are compatible with these advancements. By staying up to date, you can take advantage of new features, functionalities, and interoperability with other devices and systems.
- Automate updates where possible: Most operating systems and software have options to enable automatic updates. By enabling this feature, you ensure that updates are installed promptly without relying on manual intervention. This helps to keep your devices secure even when you may forget to check for updates.
- Verify software authenticity: Cybercriminals sometimes attempt to distribute malicious software disguised as legitimate updates. Ensure that you only download updates from official sources or through legitimate update channels to avoid falling victim to fake updates.
While it might seem time-consuming to regularly update your software and operating systems, the benefits far outweigh the potential risks. Set aside time for periodic updates and consider enabling automatic updates for convenience and peace of mind. By maintaining up-to-date software, you protect your devices, personal information, and digital ecosystem from evolving cyber threats.
Use a reliable and trustworthy VPN
In an era where online privacy and security are paramount, using a Virtual Private Network (VPN) is a must. A VPN creates a secure connection between your device and the internet by encrypting your internet traffic and routing it through a remote server. Here’s why using a reliable and trustworthy VPN is essential:
- Enhanced online security: A VPN encrypts your internet traffic, making it virtually impossible for anyone, including hackers, ISPs, or government agencies, to intercept and decipher your data. It provides a secure tunnel for your online communications, protecting your sensitive information from prying eyes.
- Anonymous browsing: When you connect to a VPN, your real IP address is masked and replaced with the IP address of the VPN server. This allows you to browse the internet anonymously, preventing websites, advertisers, and other entities from tracking your online activities and collecting your personal data.
- Bypass geographical restrictions: A VPN allows you to bypass geographical restrictions and access content that may be blocked or censored in your region. By connecting to a server located in a different country, you can access region-restricted websites, streaming services, and other online resources.
- Secure Wi-Fi connections: Public Wi-Fi networks, such as those in airports, cafes, and hotels, are notorious for security vulnerabilities. By using a VPN when connected to public Wi-Fi, you create a secure and encrypted connection, protecting your data from potential eavesdropping and Wi-Fi network vulnerabilities.
- Choose a reputable VPN provider: It’s crucial to choose a reliable and trustworthy VPN provider. Research and select a provider that values user privacy, has a strong reputation for security, and offers transparent policies regarding data logging and sharing. Additionally, look for VPNs that offer strong encryption protocols and a wide range of server locations.
- Take advantage of additional features: Some VPN providers offer additional features to enhance security, such as built-in ad-blockers, malware protection, and DNS leak prevention. Consider opting for a VPN that provides these extra layers of security.
While a VPN is an effective tool for enhancing online security and privacy, it’s important to note that it’s not a one-size-fits-all solution. Some websites and services may block access from VPN IP addresses, and using a VPN can impact internet connection speeds. Nevertheless, for most internet users, using a reliable and trustworthy VPN offers significant benefits in terms of privacy, security, and unrestricted access to online content.
Secure your home network
With the increasing number of connected devices in our homes, securing your home network is crucial to protect your personal information and maintain a safe digital environment. Here are some essential steps to secure your home network:
- Change your default router settings: When setting up your home network, change the default username and password for your router’s administrative interface. Default login credentials are widely known and can be exploited by attackers.
- Enable encryption: Ensure that your Wi-Fi network is encrypted with WPA2 or WPA3 encryption. Encryption scrambles the data transmitted between your devices and the router, preventing unauthorized access to your network.
- Use a strong Wi-Fi password: Set a strong and unique password for your Wi-Fi network. Avoid using easily guessable passwords and consider utilizing a passphrase that combines letters, numbers, and symbols.
- Enable network firewalls: Activate the built-in firewall feature on your router and individual devices. Firewalls monitor and control incoming and outgoing network traffic, acting as a barrier against unauthorized access and potential attacks.
- Disable remote management: Unless necessary, disable remote management of your router. This restricts access to the router’s administration interface from outside your home network, minimizing the risk of unauthorized configuration changes.
- Regularly update router firmware: Keep your router’s firmware up to date by checking for updates from the manufacturer. Firmware updates often include security patches that address vulnerabilities in the router’s software.
- Segment your network: Consider segmenting your network by creating separate Wi-Fi networks for devices with different security requirements. For example, you could have a guest network for visitors and a separate network for your smart devices.
- Disable Wi-Fi Protected Setup (WPS): WPS can be vulnerable to brute-force attacks. Disable this feature on your router to prevent potential unauthorized access attempts.
- Secure your IoT devices: Internet of Things (IoT) devices, such as smart cameras or thermostats, can be entry points for attackers. Change the default passwords, update their firmware regularly, and connect them to a separate network segment.
- Regularly review connected devices: Periodically review the devices connected to your network. Disconnect devices you no longer use or recognize to ensure that only authorized devices have access to your home network.
By implementing these network security practices, you can significantly reduce the risk of unauthorized access and protect your digital devices and personal data. Remember, securing your home network is an ongoing process, so make it a habit to regularly review and update your network settings and devices to stay one step ahead of potential threats.
Backup your data regularly
Backing up your data is a fundamental practice that helps safeguard your important files and ensure that you can recover them in the event of data loss, such as hardware failure, accidental deletion, or security breaches. Here’s why regular data backups are essential:
- Data loss prevention: Accidents and unexpected events can occur at any time, leading to the loss of valuable data. Regular backups create a safety net, allowing you to restore your files and recover from data loss without significant disruption to your work or personal life.
- Protection against ransomware: Ransomware attacks, where hackers encrypt your files and demand a ransom for their release, have become increasingly prevalent. With proper backups, you can restore your files from a clean backup source rather than succumbing to the demands of cybercriminals.
- Secure your memories and important files: Irreplaceable memories, such as family photos or important documents, can be lost forever if not backed up regularly. By creating backups, you ensure that these cherished moments and essential files are protected and easily retrievable.
- Reduction of downtime: In the event of a computer or system failure, having recent backups allows you to quickly restore your data and resume normal operations. This minimizes downtime and prevents disruptions to your productivity or personal activities.
- Ease of migration to new devices: When upgrading to a new device or transitioning to a different system, backups make the transition seamless. You can transfer your files and settings from the backup, ensuring a smooth and efficient migration process.
When it comes to data backups, it’s important to follow these best practices:
- Choose the right backup solution: Select a backup solution that suits your needs, whether it’s an external hard drive, cloud storage, or a combination of both. Each option has its advantages and considerations, so evaluate which one provides the ideal balance of convenience, security, and accessibility for your data.
- Automate the backup process: Set up automated backups to ensure that your data is backed up regularly without relying on manual intervention. This reduces the risk of forgetting to back up important files and simplifies the backup process.
- Encrypt your backups: If you store backups in cloud storage or external hard drives, consider encrypting them to add an extra layer of security. Encryption protects your data from unauthorized access, ensuring that only you can restore and access your backed-up files.
- Test your backups: Regularly validate and test your backups to ensure that your data is successfully backed up and can be restored when needed. This verification process gives you confidence in the integrity of your backups.
- Keep backups offsite: Storing backups in a separate location from your primary system protects against physical damage and theft. Consider rotating backups to an offsite location, such as a safe deposit box or a trusted friend’s house, to ensure redundancy and resilience.
Remember, backups are only effective if you maintain them regularly. Set a schedule for backups and make it a habit to perform them consistently. By prioritizing regular data backups, you can ensure the safety, accessibility, and longevity of your important files and memories.
Avoid suspicious websites and downloads
When browsing the internet or downloading files, it’s crucial to exercise caution and be mindful of the websites you visit and the files you download. Taking the following steps can help you avoid potential threats and protect your devices and personal information:
- Stick to trusted websites: Only visit reputable websites that have a proven track record for security. Be cautious when clicking on links from unknown sources, as they may lead to malicious websites or initiate downloads of harmful files.
- Look for HTTPS: Before entering any sensitive information or making online transactions, ensure that the website is secured with HTTPS (Hypertext Transfer Protocol Secure), indicated by a padlock icon in the address bar. This encryption protocol helps protect your data from interception by unauthorized parties.
- Be wary of phishing websites: Phishing websites try to trick users into providing their sensitive information by masquerading as trustworthy sites. Double-check the website’s URL for any misspellings or suspicious variations and avoid entering personal information on unfamiliar or suspicious-looking sites.
- Be cautious of pop-ups and ads: Pop-up windows and intrusive ads can link to malicious websites or initiate malicious downloads. Avoid clicking on these ads, and consider using an ad blocker to reduce the risk of encountering potentially harmful content.
- Download from reputable sources: When downloading files or applications, only do so from trusted sources, such as official websites or trusted app stores. Be cautious of third-party sites or peer-to-peer networks that may distribute compromised or pirated software.
- Verify file authenticity: Before opening or executing downloaded files, scan them with reputable antivirus software to detect any potential malware. Additionally, double-check the file name, size, and extension to ensure they align with your expectations and avoid opening suspicious or unexpected file types.
- Keep your browser and security software up to date: Regularly update your web browser and antivirus software to ensure they have the latest security patches, which protect against newly discovered threats. Set your software to update automatically to stay protected from emerging risks.
- Educate yourself about common online scams: Stay informed about common online scams, such as fake software updates, free offers, or prize promotions. By familiarizing yourself with these scams, you can better recognize and avoid potential traps.
Remember, prevention is key when it comes to avoiding suspicious websites and downloads. Remain cautious, stay informed, and trust your instincts. By adopting these practices, you can minimize the risk of encountering malicious websites or downloading potentially harmful files, keeping your devices and personal information safe and secure.
Educate yourself about internet security threats
In the rapidly evolving world of technology, staying informed about internet security threats is crucial to protect yourself and your digital assets. By being aware of the various threats and understanding how they can impact you, you can take proactive measures to safeguard your online presence. Here are some reasons why educating yourself about internet security threats is essential:
- Recognize and avoid common threats: Understanding common threats like phishing, malware, ransomware, and identity theft allows you to recognize warning signs and take appropriate action. Educate yourself on the techniques used by cybercriminals to exploit vulnerabilities, such as social engineering tactics and deceptive practices, so you can protect yourself from falling victim to these threats.
- Protect your personal information: Knowledge about internet security threats helps you understand the importance of safeguarding your personal information. By learning about privacy settings, secure communication methods, and best practices for sharing information online, you can minimize the risk of your data being compromised or misused.
- Stay updated with emerging threats: New security threats and attack vectors are constantly emerging as technology advances. By staying informed through reliable sources like cybersecurity news websites, blogs, and official security advisories, you can adapt your security practices to counter these evolving threats.
- Keep your devices and software secure: Educating yourself about internet security threats helps you understand the importance of using strong passwords, keeping your software up to date, and employing security measures like antivirus software and firewalls. With this knowledge, you can implement best practices to protect your devices, networks, and sensitive data.
- Teach others and promote a safer digital environment: Sharing your knowledge about internet security threats allows you to educate others and contribute to a safer digital ecosystem. By spreading awareness about online risks among family, friends, and colleagues, you can collectively reduce the impact of cyber threats and create a safer online environment for everyone.
There are several resources available to help you stay informed about internet security threats:
- Cybersecurity websites and blogs: Follow reputable cybersecurity websites and blogs that provide up-to-date information on the latest threats, vulnerabilities, and best practices. These resources often offer practical tips and insights to help you stay ahead of potential risks.
- Official security advisories: Governments and cybersecurity organizations issue security advisories to warn users about emerging threats. Stay informed by regularly checking these sources for any updates or alerts relevant to your digital environment.
- Online security communities: Join online forums and communities dedicated to internet security. Engage in discussions, share experiences, and learn from others who have encountered and managed security threats. Participating in these communities can be an excellent way to broaden your knowledge and gain insights from experts and fellow users.
- Security awareness training: Many organizations offer security awareness training programs designed to educate individuals on internet security threats and best practices. Consider enrolling in a training course or seeking out free resources to enhance your knowledge and skills.
Remember that internet security threats are ever-evolving, and staying educated is an ongoing process. By dedicating time and effort to educate yourself, you empower yourself to navigate the digital landscape safely and protect your online presence.