Wireshark Overview
Wireshark is a powerful and widely-used open-source network protocol analyzer. It allows you to capture and analyze network traffic in real-time, providing valuable insights into the communication between devices on a network. Wireshark supports a wide range of network protocols, making it an essential tool for network administrators, developers, and security professionals.
By capturing packets sent and received over a network, Wireshark enables you to examine the details of each packet, including source and destination addresses, protocol information, and even the contents of the packets themselves. This level of visibility into network traffic can help identify and troubleshoot various network issues, security vulnerabilities, and performance bottlenecks.
Installing Wireshark is a straightforward process, as it is available for various platforms, including Windows, macOS, and Linux. Once installed, Wireshark provides a user-friendly interface that allows you to start capturing network traffic with just a few clicks.
When capturing network traffic, you can choose to capture packets from specific network interfaces or apply filters to capture only the packets relevant to your analysis. Wireshark also allows you to save captured packets for offline analysis or share them with colleagues for collaborative troubleshooting.
After capturing the network traffic, Wireshark provides powerful analysis features to help make sense of the captured data. The built-in packet analyzer allows you to navigate through captured packets, inspect packet details, and even reconstruct fragmented packets.
Wireshark supports advanced features like filtering and sorting packets based on various criteria, such as source or destination IP address, protocol, port number, or even specific packet contents. This allows you to focus on the specific packets that are relevant to your analysis, saving time and making your analysis more efficient.
Understanding protocols and packets is crucial when analyzing network traffic, and Wireshark provides comprehensive protocol support for a wide range of network protocols, including ICMP, TCP, UDP, DNS, HTTP, SSL/TLS, and many more. It allows you to dissect and decode packets, revealing the underlying protocol details and allowing for in-depth analysis.
Wireshark can be used to analyze various types of network traffic, including HTTP, DNS, TCP, UDP, SSL/TLS, and even VoIP traffic. By examining the different protocols and their associated packets, you can gain insights into network performance, security vulnerabilities, and potential issues affecting the network infrastructure.
Overall, Wireshark is an indispensable tool for anyone involved in network analysis, troubleshooting, or security. Its intuitive interface, powerful analysis features, and extensive protocol support make it a valuable asset for network professionals. Whether you are diagnosing network issues, analyzing network performance, or investigating security incidents, Wireshark provides the necessary capabilities to dive deep into network traffic and discover valuable insights.
Installing Wireshark
Installing Wireshark is a straightforward process and can be done on various operating systems, including Windows, macOS, and Linux.
For Windows users, you can download the Wireshark installer from the official website. Once downloaded, run the installer and follow the on-screen instructions. The installer will guide you through the installation process, allowing you to choose additional components and configuration options if desired. After the installation is complete, you will find the Wireshark application ready to use in your start menu or desktop.
Mac users can install Wireshark by downloading the .dmg package from the official website. Once downloaded, open the package and drag the Wireshark application to the Applications folder. After the installation is finished, you can launch Wireshark from the Launchpad or the Applications folder.
If you are using a Linux distribution, you can install Wireshark using the package manager specific to your distribution. For example, on Debian or Ubuntu-based distributions, you can run the following command in the terminal:
sudo apt-get install wiresharkFor Fedora or CentOS-based distributions, you can use the following command:
sudo dnf install wiresharkAfter the installation is complete, you may need to add your user to the “wireshark” group to allow capturing packets without root privileges. You can do this by running the following command:
sudo usermod -aG wireshark your_usernameOnce installed, Wireshark provides a user-friendly interface that allows you to start capturing network traffic. The main window consists of various panels, including the packet list, packet details, packet tree, and protocol tree. You can customize the layout of the panels to suit your needs.
It’s important to note that capturing network traffic usually requires administrative or root privileges, as it involves accessing the network interface directly. Therefore, when launching Wireshark, you may need to provide the necessary permissions or run it with elevated privileges.
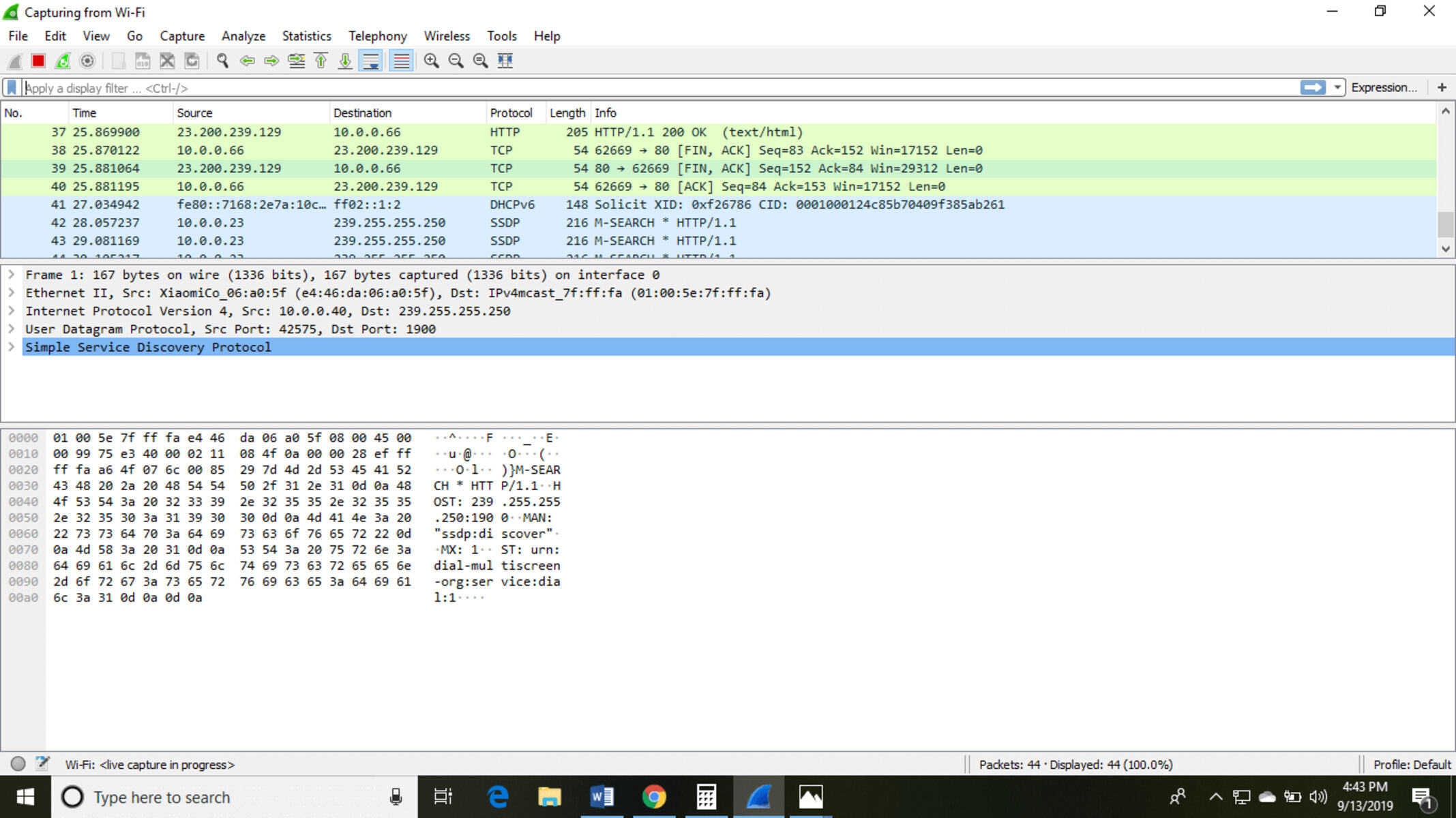
Capturing Network Traffic
One of the core functionalities of Wireshark is capturing network traffic in real-time, allowing you to analyze the communication between devices on a network. Capturing network traffic can help you troubleshoot network issues, monitor network performance, or investigate security incidents.
To start capturing network traffic, open Wireshark and select the network interface you want to capture packets from. This can be your Ethernet adapter, Wi-Fi adapter, or any other network interface available on your system. Wireshark will start listening to packets on the selected interface, capturing all the traffic that passes through it.
By default, Wireshark captures all packets on the selected interface. However, you can apply filters to capture only the packets that are relevant to your analysis. Wireshark supports a wide range of filter options based on IP addresses, protocols, port numbers, and specific packet contents. Filters help narrow down the captured packets, allowing you to focus on specific communication or specific network issues.
Once the capture is running, you will see a live packet list in the main Wireshark window, displaying the captured packets in real-time. Each packet is listed with details such as the source and destination IP addresses, protocol information, and packet length.
Wireshark allows you to view detailed information about each captured packet by selecting it from the packet list. The packet details panel provides in-depth information about the selected packet, including protocol-specific details, packet header values, and even the raw packet data.
In addition to live capturing, Wireshark also provides the option to capture packets to a file for offline analysis. This is especially useful when you want to capture traffic over an extended period or share captured packets with others. Simply select the “File” menu and choose “Save” or use the Ctrl+S shortcut to save the captured packets to a file. You can then load the saved capture file into Wireshark for analysis at a later time.
Wireshark also offers advanced features for capturing specific types of network traffic. For example, if you want to capture only HTTP traffic, you can use the built-in “Follow TCP Stream” feature. This allows you to capture and display the complete HTTP conversations between the client and server, making it easier to analyze the HTTP traffic and identify any issues.
It’s important to note that capturing network traffic can be resource-intensive, especially when capturing a large amount of traffic or using complex filtering rules. Therefore, it’s recommended to have sufficient system resources, including CPU, memory, and storage, to accommodate the capture requirements.
Overall, Wireshark provides powerful capabilities for capturing and analyzing network traffic. By capturing packets from specific interfaces, applying filters, and utilizing advanced features, you can gain valuable insights into network communication, troubleshoot issues more effectively, and make informed decisions to optimize network performance.
Analyzing Network Traffic
Once you have captured network traffic using Wireshark, the next step is to analyze the captured packets to gain insights into the communication between devices on the network. Wireshark provides a wide range of analysis features to help you interpret and understand the network traffic.
The packet list in Wireshark displays the captured packets, allowing you to navigate through them. Each packet is listed with details such as the source and destination IP addresses, protocol information, and packet length. By examining the packet list, you can quickly identify patterns or anomalies in the network traffic.
By selecting a packet from the list, you can view detailed information about that packet in the packet details panel. Wireshark decodes the packet based on its protocol and provides protocol-specific information such as header values and payload contents. This information can help you understand the purpose and content of each packet.
Wireshark also offers the ability to filter and sort packets based on various criteria. This allows you to focus on specific packets or specific aspects of the network traffic. For example, you can filter packets based on source or destination IP addresses, specific protocols, port numbers, or even specific packet contents. Filtering and sorting make it easier to analyze specific communication or track down specific network issues.
In addition to individual packet analysis, Wireshark provides advanced analysis features for interpreting and understanding network traffic at a higher level. For example, Wireshark can reconstruct fragmented packets, allowing you to view the complete content of packets that were split across multiple packets during transmission.
Wireshark also provides statistics and graphs to visualize the network traffic. These statistics include packet count, packet rate, protocol distribution, and network conversations. The graphs provide a visual representation of the traffic patterns, making it easier to identify abnormal behavior or performance bottlenecks.
Wireshark supports a wide range of network protocols, and it can dissect and decode packets for each supported protocol. This allows you to analyze the specific protocol headers and contents, gaining insights into the behavior and performance of the protocols used in the network communication.
Furthermore, Wireshark provides expert analysis information. It detects and highlights potential issues or anomalies in the network traffic based on predefined rules and heuristics. These expert analysis details can be helpful in identifying security vulnerabilities, misconfigurations, or abnormal network behavior.
It’s important to note that analyzing network traffic requires a good understanding of network protocols and their behavior. Wireshark provides protocol-specific information and decodes packets accordingly, but interpreting the data requires knowledge of the protocols involved.
By utilizing the analysis features offered by Wireshark, you can gain valuable insights into network communication, troubleshoot network issues more effectively, and identify potential security vulnerabilities or performance bottlenecks. Understanding the network traffic allows you to make informed decisions to optimize network performance, ensure proper network security, and improve overall network reliability.
Filtering and Sorting Packets
Wireshark provides powerful filtering and sorting capabilities that allow you to focus on specific packets or specific aspects of the captured network traffic. Filtering and sorting packets can help you streamline your analysis, locate specific packets of interest, and identify patterns or anomalies in the network communication.
When analyzing network traffic, you can apply filters to display only the packets that meet specific criteria. Wireshark supports a wide range of filters based on source or destination IP addresses, protocols, port numbers, and even specific packet contents. By applying filters, you can narrow down the packet list to show only the packets that are relevant to your analysis.
To apply a filter, you can use the filter toolbar located at the top of the Wireshark window. Simply enter the desired filter expression and press Enter or click the Apply button. The packet list will update to display only the packets that match the specified filter criteria.
For example, you can apply a filter to display only HTTP traffic by entering “http” in the filter expression. This will show you all the packets that are related to HTTP communication, making it easier to analyze the HTTP traffic and identify any issues. Similarly, you can apply filters for specific IP addresses, protocols, or even specific text patterns in packet contents.
Wireshark also supports advanced filtering options, such as logical operators (AND, OR, NOT) and compound expressions. This allows you to combine multiple filter conditions to create more complex filtering rules. You can use parentheses to group filter expressions and specify the order of evaluation for complex filters.
In addition to filtering, Wireshark allows you to sort the packets based on various criteria. This can be helpful when you want to analyze packets in a specific order, such as sorting by the time of capture or sorting by packet length. Sorting packets allows you to focus on specific aspects of the network traffic or track down specific packet patterns.
To sort packets, you can click on the column headers in the packet list. Clicking once will sort the packets in ascending order based on that column, and clicking again will sort them in descending order. By sorting packets, you can easily identify patterns or anomalies in the network traffic, such as packets with unusually high or low response times.
Combining filtering and sorting allows for a more refined analysis of the network traffic. For example, you can filter packets based on a specific protocol, such as HTTP, and then sort them by packet size to identify unusually large or small HTTP packets.
It’s important to experiment with different filters and sorting options to tailor your analysis to the specific needs of your investigation. By leveraging these powerful capabilities of Wireshark, you can quickly locate and analyze the relevant packets, saving time and making your analysis more efficient.
Overall, filtering and sorting packets in Wireshark help you focus on specific aspects of the network traffic, track down specific packet patterns, and identify anomalies or issues in the communication between devices. By utilizing these features effectively, you can streamline your analysis and gain deeper insights into the network traffic.
Understanding Protocols and Packets
Wireshark provides comprehensive protocol support, allowing you to analyze and understand the behavior of various network protocols used in the captured network traffic. By dissecting and decoding packets, Wireshark enables you to gain insights into the structure, content, and interactions of different protocols.
Each packet in a network contains a combination of headers and data specific to a particular protocol. Wireshark takes advantage of its expansive protocol knowledge to dissect packets and present their contents in a human-readable format. This allows you to inspect the different layers and fields of each packet, providing valuable information about the protocols involved in the communication.
When analyzing network traffic in Wireshark, the protocol hierarchy, or packet tree, is displayed alongside the packet list. The packet tree provides a detailed breakdown of the different layers and protocol headers present in each packet. This visual representation helps you understand the encapsulation of protocols within one another and navigate through the packet structure.
Wireshark can dissect and decode a wide range of network protocols, including common protocols like TCP, UDP, ICMP, DNS, HTTP, SSL/TLS, and many more. By expanding the packet tree in Wireshark, you can delve into the details of each protocol layer, inspecting the specific fields, flags, and values associated with that protocol.
Understanding the protocols involved in the network traffic is essential for analyzing and troubleshooting communication issues. Each protocol has its own specific behaviors, requirements, and potential issues that can impact network performance and security.
For example, analyzing TCP traffic in Wireshark provides insights into the establishment, maintenance, and termination of TCP connections. By inspecting TCP flags, sequence numbers, and window sizes, you can identify issues such as packet loss, retransmissions, or TCP flow control problems.
Similarly, analyzing UDP traffic helps you understand datagram-based communication, where reliability is not guaranteed. By inspecting UDP headers and payload, you can identify malformed packets, port scanning attempts, or potential security vulnerabilities associated with specific UDP services.
Wireshark also supports the analysis of application-layer protocols like HTTP and DNS. By examining HTTP packets, you can assess web page loading times, analyze response headers, and troubleshoot issues related to HTTP status codes or content delivery. Analyzing DNS traffic allows you to identify DNS queries and responses, diagnose DNS resolution issues, and detect potential DNS spoofing or cache poisoning attempts.
In addition, Wireshark can dissect encrypted communication protocols like SSL/TLS. Although the payload is encrypted, Wireshark can still provide valuable information about the handshake process, negotiated keys, and cipher suites, allowing you to assess the security configuration and overall strength of the encrypted connection.
By understanding the protocols and their associated packets, Wireshark empowers you to analyze network traffic with deeper insights into the behavior, performance, and security of the communication. This understanding enables you to troubleshoot network issues, optimize network performance, and identify potential security vulnerabilities effectively.
Analyzing HTTP Traffic
HTTP (Hypertext Transfer Protocol) is a fundamental protocol used for communication between web browsers and web servers. Analyzing HTTP traffic with Wireshark provides valuable insights into web application behavior, performance, and potential security issues. Wireshark allows you to dissect and decode HTTP packets, enabling you to examine the HTTP headers, methods, response codes, and even the content of web requests and responses.
When analyzing HTTP traffic in Wireshark, you can filter packets based on the HTTP protocol to focus solely on HTTP communication. By applying a filter like “http” or “tcp.port == 80” (assuming standard HTTP traffic on port 80), you can narrow down the packet list and analyze only the HTTP packets.
Wireshark displays detailed information about each HTTP packet, including the HTTP version, request method (GET, POST, etc.), response codes (such as 200 OK or 404 Not Found), and the URLs involved. By examining the HTTP headers, you can gather important information about caching directives, cookies, content encoding, and other relevant details of the HTTP transactions.
Furthermore, Wireshark allows you to follow the TCP stream for an HTTP connection. This feature reconstructs the entire HTTP conversation between a client and server, presenting it as a cohesive flow. Following the TCP stream provides a comprehensive view of the exchanged HTTP requests and responses, making it easier to analyze the flow of data and identify any abnormalities or errors.
Analyzing HTTP traffic in Wireshark can be particularly useful for troubleshooting web application issues. By examining the HTTP response codes, you can identify any server-side errors (5xx) or client-side errors (4xx), which can give you insights into potential issues with the web server or application code.
Wireshark also allows you to analyze the performance of web pages by measuring the time between various stages of an HTTP transaction. By inspecting timestamps in the HTTP headers, you can assess the time taken for the DNS resolution, establishing the TCP connection, SSL/TLS handshake, and receiving the content. This analysis can help pinpoint performance bottlenecks, such as slow DNS resolution, high latency, or excessive server response times.
In addition to performance analysis, Wireshark provides visibility into the content of HTTP traffic. It allows you to view the actual HTML, CSS, JavaScript, and other resources exchanged between the client and server. This can be valuable for troubleshooting issues related to missing resources, incorrect content, or potential security vulnerabilities in web applications.
Wireshark also supports the analysis of secure HTTP traffic using SSL/TLS. When SSL/TLS is used to encrypt HTTP communication (HTTPS), Wireshark can decrypt and analyze the encrypted traffic if you have the private key available. This allows you to view the exchanged HTTP requests and responses in clear text, aiding in the analysis of HTTPS traffic.
Overall, analyzing HTTP traffic in Wireshark provides a wealth of information about web application behavior, performance, and potential security issues. By dissecting and understanding the HTTP packets, you can troubleshoot application errors, optimize web performance, and ensure the security of your web applications.
Analyzing DNS Traffic
DNS (Domain Name System) is a fundamental protocol used for translating domain names into IP addresses, allowing devices to locate and communicate with servers on the internet. Analyzing DNS traffic with Wireshark provides valuable insights into the DNS resolution process, DNS configuration issues, and potential security concerns. Wireshark allows you to dissect and decode DNS packets, enabling you to examine DNS queries, responses, and other relevant DNS information.
When analyzing DNS traffic in Wireshark, you can filter packets based on the DNS protocol to focus solely on DNS communication. By applying a filter like “dns” or “udp.port == 53” (assuming standard DNS traffic on port 53), you can narrow down the packet list and analyze only the DNS packets.
Wireshark displays detailed information about each DNS packet, including the DNS query type (such as A, AAAA, MX, etc.), query name (domain name being resolved), and the corresponding response. By examining the DNS headers, you can gather important information about DNS servers, response codes, and other relevant details of the DNS transactions.
Furthermore, Wireshark allows you to follow the UDP stream for a DNS connection. This feature reconstructs the entire DNS conversation between a client and server, presenting it as a cohesive flow. Following the UDP stream provides a comprehensive view of the exchanged DNS queries and responses, making it easier to analyze the flow of data and identify any abnormalities or errors.
Analyzing DNS traffic in Wireshark can be particularly useful for troubleshooting DNS-related issues. By examining the DNS response codes, you can diagnose potential issues like DNS server errors (NXDOMAIN), server misconfigurations, or DNS resolution failures.
Wireshark also allows you to analyze the performance of DNS resolution by measuring the time between various stages of the DNS transaction. By inspecting timestamps in the DNS headers, you can assess the time taken for DNS queries, name server lookups, and receiving the DNS responses. This analysis can help identify potential delays in the DNS resolution process that may impact website loading times or other network operations.
In addition to performance analysis, Wireshark provides visibility into the contents of DNS traffic. It allows you to view the actual domain names being queried and the corresponding IP addresses being resolved. This can be valuable for troubleshooting issues related to DNS misconfigurations, wrong DNS responses, or DNS spoofing attacks.
Wireshark also supports the analysis of DNS over TLS (DoT) traffic or DNS over HTTPS (DoH) traffic when DNS queries are encrypted. When DoT or DoH is used, Wireshark can decrypt and analyze the encrypted DNS traffic if you have the necessary keys available. This allows you to view the exchanged DNS queries and responses in clear text, aiding in the analysis of encrypted DNS traffic.
Overall, analyzing DNS traffic in Wireshark provides valuable insights into the DNS resolution process, DNS configuration issues, and potential security concerns. By dissecting and understanding the DNS packets, you can troubleshoot DNS-related problems, ensure proper DNS resolution, and identify and mitigate potential security threats related to DNS.
Analyzing TCP Traffic
TCP (Transmission Control Protocol) is a widely used transport protocol in computer networks. Analyzing TCP traffic with Wireshark provides valuable insights into the behavior, performance, and potential issues related to TCP-based communication. Wireshark allows you to dissect and decode TCP packets, enabling you to examine various aspects of TCP connections, including establishing and terminating connections, flow control, congestion control, and data transmission.
When analyzing TCP traffic in Wireshark, you can filter packets based on the TCP protocol to focus solely on TCP communication. By applying a filter like “tcp” or specifying the specific source or destination port (e.g., “tcp.port eq 80” for HTTP), you can narrow down the packet list and analyze only the TCP packets relevant to your analysis.
Wireshark displays detailed information about each TCP packet, including the source and destination IP addresses, source and destination port numbers, sequence numbers, acknowledgment numbers, TCP flags, and more. By examining these details, you can gather insights into the TCP communication and identify potential issues.
One aspect to analyze in TCP traffic is the establishment and termination of TCP connections. By examining the TCP three-way handshake, you can understand how connections are established between clients and servers. Analyzing the TCP connection termination process can help identify issues such as half-open connections or premature connection closures.
Flow control and congestion control are essential aspects of TCP performance. Wireshark allows you to analyze these aspects by inspecting TCP window sizes, TCP acknowledgments, and TCP congestion control mechanisms like slow start, congestion avoidance, and fast retransmit. Analyzing TCP flow control and congestion control can help identify network bottlenecks, packet loss, or inefficient network communication.
Additionally, Wireshark provides the ability to analyze TCP retransmissions. Retransmissions occur when a packet is lost or not acknowledged within a specified timeout period. By analyzing retransmissions, you can identify potential network issues, such as high latency or packet loss, and take appropriate steps to improve network performance.
Wireshark also supports the analysis of TCP performance metrics. By examining timestamps in TCP packets, you can calculate round-trip times (RTTs), TCP throughput, and TCP retransmission rates. These performance metrics are invaluable when troubleshooting network issues, determining application response times, or identifying potential bottlenecks in the network infrastructure.
Decrypting and analyzing encrypted TCP traffic is also possible with Wireshark if you have the necessary encryption keys. This allows you to inspect the content and behavior of encrypted TCP connections such as HTTPS or SSL/TLS encrypted communications.
Overall, analyzing TCP traffic in Wireshark provides valuable insights into the behavior, performance, and potential issues related to TCP-based communication. By dissecting and understanding TCP packets, you can troubleshoot TCP-specific problems, optimize TCP performance, and ensure the reliability of network communication relying on TCP.
Analyzing UDP Traffic
UDP (User Datagram Protocol) is a connectionless transport protocol commonly used for lightweight and low-latency communication. Analyzing UDP traffic with Wireshark provides valuable insights into the behavior, performance, and potential issues related to UDP-based communication. Wireshark allows you to dissect and decode UDP packets, enabling you to examine various aspects of UDP communication, including the transmission of datagrams, port numbers, and content.
When analyzing UDP traffic in Wireshark, you can filter packets based on the UDP protocol to focus solely on UDP communication. By applying a filter like “udp” or specifying the specific source or destination port (e.g., “udp.port eq 53” for DNS), you can narrow down the packet list and analyze only the UDP packets relevant to your analysis.
Wireshark displays detailed information about each UDP packet, including the source and destination IP addresses, source and destination port numbers, and the length of the UDP datagram. By examining these details, you can gather insights into the UDP communication and identify potential issues.
One aspect to analyze in UDP traffic is the content of the datagrams. Unlike TCP, UDP does not guarantee reliable and ordered delivery of packets. Therefore, analyzing the contents of UDP datagrams becomes crucial. By examining the payload of the UDP packets, you can extract and interpret the data that is being transmitted.
Analyzing UDP traffic also involves examining the port numbers used by the applications or services. By inspecting the source and destination port numbers, you can identify the specific applications or services that are transmitting or receiving UDP packets. This information can be useful for troubleshooting, monitoring network activity, or identifying potential security concerns.
Wireshark allows you to analyze UDP multicast traffic as well. Multicast is a communication method where one sender can transmit data to multiple receivers simultaneously. Analyzing UDP multicast traffic in Wireshark allows you to inspect the multicast group address, source address, destination address, and the contents of the multicast packets.
Another aspect of UDP traffic to analyze is performance. As UDP does not have built-in mechanisms for flow control or reliable delivery, analyzing UDP performance can involve assessing factors like packet loss, latency, and overall network efficiency. By examining timestamps, packet sizes, and network behaviors, you can gain insights into the performance characteristics of UDP communication.
It’s also worth noting that Wireshark enables the analysis of various UDP-based protocols such as DNS, VOIP, SNMP, DHCP, and others. These protocols have specific behaviors, message formats, and potential issues that can be identified and debugged through Wireshark’s packet inspection capabilities.
Overall, analyzing UDP traffic in Wireshark provides valuable insights into the behavior, performance, and potential issues related to UDP-based communication. By dissecting and understanding UDP packets, you can troubleshoot UDP-specific problems, optimize UDP performance, and ensure the reliability of network communication relying on UDP.
Analyzing SSL/TLS Traffic
SSL/TLS (Secure Sockets Layer/Transport Layer Security) is a cryptographic protocol used to secure communication over the internet. Analyzing SSL/TLS traffic with Wireshark provides valuable insights into the establishment, negotiation, and security of encrypted connections. Wireshark allows you to dissect and decode SSL/TLS packets, enabling you to examine various aspects of SSL/TLS communication, including cipher suites, certificate information, and the encrypted content exchanged between client and server.
When analyzing SSL/TLS traffic in Wireshark, you can filter packets based on the TCP ports typically used for SSL/TLS communication, such as 443 for HTTPS. By applying a filter like “tcp.port == 443”, you can narrow down the packet list and focus on SSL/TLS encrypted traffic.
Wireshark displays detailed information about each SSL/TLS packet, including the version of SSL/TLS used, the cipher suite negotiated between the client and server, and relevant handshake information. By examining these details, you can gather insights into the security features and encryption algorithms being used in the SSL/TLS connection.
One of the key aspects to analyze in SSL/TLS traffic is the handshake process. The handshake is performed at the beginning of an SSL/TLS session and involves multiple steps, including establishing a secure connection, authenticating the server, and optionally, the client. By examining the handshake packets, you can identify the supported SSL/TLS versions, cipher suites, and certificate details exchanged during the negotiation process.
Furthermore, Wireshark allows you to analyze the certificate chain in SSL/TLS traffic. By inspecting the certificates exchanged between the client and server, you can validate the server’s identity, verify certificate chains, and identify potential security concerns such as expired or self-signed certificates.
Decryption is another powerful feature of Wireshark when analyzing SSL/TLS traffic. If you have access to the private key used for the SSL/TLS connection, Wireshark can decrypt and analyze the encrypted packets, providing clear text visibility into the exchanged data. This allows you to inspect the content of the encrypted communication and understand the behavior and content transmitted over the SSL/TLS connection.
Wireshark also offers insights into encrypted application-layer protocols utilizing SSL/TLS, such as HTTPS. By analyzing the decrypted SSL/TLS packets, you can extract and examine the content of the HTTP requests and responses, including headers, query parameters, and the actual web page content. This level of visibility helps troubleshoot application-level issues and identify potential security vulnerabilities within encrypted web communication.
Overall, analyzing SSL/TLS traffic in Wireshark allows you to gain valuable insights into the security, negotiation, and content of encrypted connections. By dissecting and understanding SSL/TLS packets, you can troubleshoot SSL/TLS-specific problems, verify the security of encrypted communication, and gain visibility into the encrypted content exchanged between clients and servers.
Analyzing VoIP Traffic
VoIP (Voice over Internet Protocol) refers to the technology that enables voice communication over an IP network. Analyzing VoIP traffic with Wireshark allows you to gain insights into the behavior, quality, and potential issues related to voice communication over IP. Wireshark enables you to dissect and decode VoIP packets, providing visibility into the protocols, signaling, and media streams used in VoIP communication.
When analyzing VoIP traffic in Wireshark, you can filter packets based on the specific protocols used for VoIP communication. Common VoIP protocols include SIP (Session Initiation Protocol) for call signaling and RTP (Real-Time Transport Protocol) for media delivery. By applying filters such as “sip” or “rtp”, you can narrow down the packet list and analyze only the VoIP packets relevant to your analysis.
Wireshark displays detailed information about each VoIP packet, including the source and destination IP addresses, source and destination ports, sequence numbers, timestamps, and payload content. By examining these details, you can gather insights into the VoIP communication and identify potential issues affecting call quality and functionality.
One aspect to analyze in VoIP traffic is the call signaling process, typically implemented using SIP. By examining SIP packets, you can see call setup and teardown messages, caller and callee information, and other signaling parameters. Analyzing SIP packets allows you to troubleshoot issues related to call setup failures, authentication problems, or misconfigured SIP servers.
In addition to signaling, analyzing the media streams in VoIP traffic is crucial for understanding call quality. RTP is the transport protocol used to deliver voice and video streams in VoIP communication. By examining RTP packets, you can assess metrics like packet loss, jitter, and latency. These metrics are important for diagnosing and troubleshooting issues affecting the quality of VoIP calls.
Wireshark provides features like RTP stream analysis that allows you to plot statistics, visualize packet sequence graphs, and analyze voice or video quality metrics. By examining these statistics, you can gauge call quality, detect anomalies, and identify potential network or codec-related issues impacting the audio or video streams.
Furthermore, Wireshark allows you to analyze specific codecs used for voice compression in VoIP communication. Codecs like G.711, G.729, or Opus encode voice data for transmission over the network. By examining the codec information in Wireshark, you can identify the codecs being used, assess their bandwidth requirements, and troubleshoot issues related to codec negotiation, compatibility, or performance.
Wireshark also supports the analysis of encrypted VoIP communication like SRTP (Secure Real-Time Transport Protocol). With the necessary encryption keys, Wireshark can decrypt and analyze the encrypted voice or video streams. This allows you to inspect the content and assess the security of encrypted VoIP communication.
Overall, analyzing VoIP traffic in Wireshark provides valuable insights into the behavior, quality, and potential issues related to voice communication over IP networks. By dissecting and understanding VoIP packets, you can troubleshoot VoIP-specific problems, optimize call quality, and ensure the reliability of voice communication over IP.
Troubleshooting Network Issues
When faced with network issues, Wireshark is an invaluable tool for troubleshooting and diagnosing problems. By capturing and analyzing network traffic, Wireshark provides insights into the behavior of network protocols, identifies anomalies, and helps pinpoint the source of network issues. Here are several ways in which Wireshark can aid in troubleshooting network problems.
One common use case of Wireshark is diagnosing connectivity issues. By capturing packets on the network, you can observe the establishment and termination of connections, allowing you to identify any failed or incomplete connections. Wireshark can reveal issues such as network misconfigurations, firewall rules blocking traffic, or incorrect network routing.
Wireshark also helps in identifying the root causes of slow network performance. By analyzing the timing and sequence of packets, you can detect delays, examine packet retransmissions, and identify potential sources of congestion. This information can lead to optimizations such as adjusting network settings, improving bandwidth allocation, or identifying network bottlenecks.
Additionally, Wireshark assists in troubleshooting application-specific issues. By capturing packets related to a specific application, you can examine the protocol behavior and identify any anomalies or errors. For example, Wireshark can help pinpoint HTTP errors, DNS resolution failures, or misconfigured application-layer protocols.
Wireshark is particularly useful for detecting and analyzing network security issues. By inspecting packets, you can identify suspicious or malicious activity such as unauthorized access attempts, port scanning, or abnormal network traffic patterns. Wireshark also reveals potential vulnerabilities in network communication such as unencrypted credentials, weak encryption, or insecure protocol configurations.
Another troubleshooting use case for Wireshark is diagnosing VoIP quality issues. By capturing and analyzing VoIP traffic, you can examine factors like packet loss, jitter, or latency, which can impact call quality. Wireshark provides insight into network-related problems affecting VoIP, allowing you to identify and address issues that may degrade call quality.
Wireshark captures packets in real-time, but it also allows for the analysis of previously captured packet files. This enables you to troubleshoot network issues that may have occurred in the past or were not observed in real-time. By loading a saved packet file into Wireshark, you can review the captured packets and perform in-depth analysis to uncover the root cause of the problem.
Furthermore, Wireshark provides various expert analysis tools and filters to automatically detect potential network issues. These tools can flag issues like TCP retransmissions, out-of-order packets, or other anomalies that may indicate network performance or configuration problems. By utilizing these expert analysis tools, you can quickly identify problematic areas for further investigation.
Wireshark also offers the ability to generate graphical representations and statistical summaries of network traffic. These visualizations help to identify patterns, analyze trends, and assess network behavior over time. This information is particularly beneficial when troubleshooting intermittent or sporadic network issues.
Wireshark can also be used in collaboration with other network monitoring tools. By leveraging Wireshark’s packet capturing capabilities alongside other tools, you can gain a comprehensive view of network performance and troubleshoot issues more effectively.
Advanced Wireshark Features
Wireshark provides a range of advanced features that enhance its capabilities for in-depth network analysis and troubleshooting. These features enable users to extract valuable insights from captured packets, apply advanced filtering and searching techniques, and perform complex analysis tasks.
One advanced feature of Wireshark is the ability to create and apply custom display filters. Display filters allow users to define specific criteria to selectively display packets based on various properties, such as protocol, source or destination IP addresses, port numbers, or specific packet contents. This enables focused analysis by excluding irrelevant traffic and highlighting relevant packets related to specific network issues or protocols.
Wireshark also supports the use of capture filters. Unlike display filters, capture filters are applied during the packet capture process, allowing users to specify which packets are captured based on specified criteria. This feature helps conserve resources by capturing only the relevant packets, reducing the amount of data that needs to be processed during analysis.
Another powerful feature of Wireshark is the ability to perform protocol-specific analysis using dissectors. Dissectors are responsible for decoding and interpreting the various network protocols present in captured packets. Wireshark provides a wide range of dissectors for common protocols such as TCP, UDP, HTTP, DNS, and more. Additionally, users can create custom dissectors to handle proprietary or lesser-known protocols, allowing for comprehensive analysis of network traffic.
Wireshark also supports the creation of statistics and summary reports. Users can generate graphical plots, tables, and statistical summaries of various network parameters, such as packet sizes, response times, protocol distributions, or conversation analysis. These visualizations aid in identifying patterns, analyzing trends, and providing a comprehensive overview of the captured network traffic.
In addition to analysis capabilities, Wireshark includes the capability to export captured packets or specific packet data in various formats, including CSV, XML, or plain text. This functionality allows for further analysis or integration with other tools and platforms. It can be particularly useful when collaborating with colleagues or when sharing packet captures with external parties for troubleshooting purposes.
Wireshark also supports scripting and automation through the use of scripting languages like Lua or Python. Users can create custom scripts to automate repetitive tasks, extract specific information from packets, or perform complex analysis using the Wireshark Command-Line Interface (CLI) or its Scripting API. Scripting capabilities extend the functionality of Wireshark and enable users to tailor the tool to their specific analysis needs.
Additionally, Wireshark offers the ability to perform expert analysis. Expert analysis identifies potential network issues, errors, or anomalies in the captured packets. Wireshark’s predefined rules and heuristics automatically flag issues such as retransmissions, unnecessary protocol behavior, or suspicious network activity. Expert analysis enhances the efficiency of analysis by providing automatic insights and highlighting areas that require further investigation.
Wireshark’s extensibility through plugins and external tools further enhances its functionality. Users can take advantage of numerous plugins and integration options to extend and customize Wireshark’s capabilities. These plugins provide additional dissectors, analysis tools, visualizations, or integration with external tools for enhanced troubleshooting and analysis workflows.
Tips and Tricks for Using Wireshark
Wireshark is a powerful tool for network analysis and troubleshooting. Here are some tips and tricks to enhance your experience and make the most out of using Wireshark:
- Learn the keyboard shortcuts: Familiarize yourself with Wireshark’s keyboard shortcuts to perform tasks more efficiently. Shortcut keys like Ctrl+F for search, Ctrl+Shift+F for applying a display filter, or Ctrl+E for stopping a packet capture can save you valuable time.
- Customize the interface: Take advantage of Wireshark’s customizable interface to adapt the layout according to your preferences. You can rearrange panels, adjust column widths, or hide unnecessary information to create a personalized workspace that suits your analysis needs.
- Master display filters: Invest time in understanding display filters as they enable you to focus on specific packets and extract relevant information. Experiment with different filter expressions to refine your analysis and quickly spot the packets that matter.
- Use coloring rules: Utilize Wireshark’s coloring rules feature to highlight specific packets based on predefined criteria. Creating coloring rules based on source or destination IP addresses, port numbers, or even display filter match can make it easier to identify important packets at a glance.
- Leverage IO graphs: Take advantage of Wireshark’s IO graph feature to visualize network statistics over time. IO graphs can display metrics like packet rate, byte rate, or even the round-trip time (RTT) for specific protocols. Visualizing these statistics can help identify trends and patterns in network behavior.
- Explore the Wireshark wiki and online resources: Wireshark has extensive documentation and an active community. Make use of the Wireshark wiki, user forums, and online tutorials to learn advanced features, explore troubleshooting techniques, and stay up-to-date with the latest developments in network analysis.
- Consider using capture filters: If you’re capturing packets on a busy network, apply capture filters to capture only the packets of interest. Capture filters can reduce the amount of captured data and optimize the performance of Wireshark by capturing only the relevant packets.
- Keep your Wireshark installation up to date: Regularly update your Wireshark installation to benefit from bug fixes, performance improvements, and new features. Official releases often include important security updates, so staying up to date is crucial for reliable and secure network analysis.
- Use profiles for different analysis scenarios: Wireshark allows you to create profiles to save specific configurations, such as capturing options, display filter preferences, or coloring rules. Use profiles to quickly switch between different analysis scenarios and streamline your workflow.
- Practice analyzing packet captures: To sharpen your Wireshark skills, practice analyzing different packet captures across various network scenarios. Analyzing real-world packet captures can help you gain experience in troubleshooting network issues, understanding protocol behaviors, and identifying potential security vulnerabilities.
By following these tips and tricks, you can enhance your efficiency, improve your analysis capabilities, and become a more proficient user of Wireshark. Remember, exploring and experimenting with Wireshark’s features will enable you to unlock its full potential for network analysis and troubleshooting.