Why You Should Never Click Suspicious Links
With the rise of cyber threats and online scams, it’s more important than ever to be cautious when encountering suspicious links. Clicking on such links can lead to various detrimental consequences, including malware infections, phishing attacks, identity theft, and financial loss. Therefore, it is crucial to understand the potential risks and adopt a proactive approach to protect yourself online.
Suspicious links can come from a variety of sources, such as unknown emails, social media messages, or unfamiliar websites. These links often masquerade as legitimate sources, enticing users with offers, discounts, or irresistible content. However, they are designed to deceive and exploit unsuspecting victims.
By clicking on a suspicious link, you may inadvertently download malicious software onto your device. Malware can not only compromise your personal information but also compromise the security of your entire system. It can steal sensitive data, log keystrokes, hijack your browser, or even gain remote control of your device.
Phishing attacks are also commonly carried out through suspicious links. Fraudsters often create fake websites that closely resemble legitimate ones to trick users into entering their personal information, such as login credentials or credit card details. This stolen information can then be used for fraudulent activities, leaving you vulnerable to financial fraud.
Additionally, suspicious links can lead to identity theft. By clicking on these links, you may unknowingly provide hackers with access to your personal information, such as your social security number, address, or date of birth. This stolen data can be used to impersonate you, causing long-term damage to your reputation and financial well-being.
Furthermore, clicking on suspicious links can expose you to scams and online fraud. These links may redirect you to fake websites or prompt you to make fraudulent purchases. Once you provide your payment information, the scammers can empty your bank account or make unauthorized transactions using your credit card.
Step 1: Copy the Link
When you come across a suspicious link, the first step is to avoid clicking on it directly. Instead, right-click on the link and select “Copy link address” or “Copy link location” (depending on your browser). Alternatively, you can highlight the link and press Ctrl+C (Windows) or Command+C (Mac) to copy it.
Copying the link allows you to investigate and analyze it without exposing yourself to potential risks. By doing this, you can take a closer look at the link’s URL, anchor text, and other suspicious elements.
It’s important to note that you should only copy the link from a trusted source. If the link is embedded within an email or a message from an unknown sender, exercise caution. Double-check the sender’s credibility and ensure that the source is legitimate before proceeding with the next steps.
By copying the link, you create a barrier between yourself and the potentially harmful content associated with it. This step is essential in minimizing the risks associated with clicking on suspicious links, protecting your devices, sensitive information, and personal security from potential threats.
To maintain cybersecurity best practices, it’s always advisable to assume that links from unknown sources are potentially dangerous. Copying the link is a proactive measure that empowers you to take control over your online safety and make informed decisions about whether or not to proceed further.
In the following steps, we will guide you through the process of analyzing the link and determining whether it is safe to click or share with others. Remember, being cautious and vigilant in the digital landscape can help safeguard your online presence and protect you from falling victim to cybercriminals.
Step 2: Analyze the Link URL
After copying the suspicious link, the next step is to analyze its URL. The URL, or Uniform Resource Locator, is the web address that provides information about the link’s destination. By examining the URL, you can gain valuable insights into the legitimacy of the website or page you may be directed to.
Start by carefully examining the domain name in the URL. Legitimate websites often have recognizable domain names that match the company or organization’s name. For example, if you receive a link claiming to be from a well-known retailer, but the domain name is misspelled or contains random characters, it’s a major red flag.
Another aspect to consider is the HTTP or HTTPS protocol. Secure websites use HTTPS, which encrypts the data exchanged between the user and the site, ensuring a higher level of security. If the URL starts with “http://” instead of “https://,” exercise caution as the website might not have proper security measures in place.
Long, convoluted URLs with many subdirectories or random characters are often indicators of suspicious or phishing links. Legitimate websites typically have concise and straightforward URLs indicative of the content they host. If the URL appears excessively complex or seems unrelated to the information being presented, it is likely best to avoid clicking on the link.
URL shortening services, such as bit.ly or goo.gl, are commonly used to condense lengthy links. While not inherently malicious, these shortened URLs can hide the true destination of the link. To analyze a shortened URL, you can use an online URL expander tool that will reveal the full URL and allow you to assess its legitimacy.
Additionally, look for unusual characters or misspellings in the URL. Cybercriminals often create fake websites with URLs that closely resemble legitimate ones. For example, they may replace letters with similar-looking characters or include additional words or numbers. Taking a closer look and comparing the URL to the official website can help you determine if there are any discrepancies.
By analyzing the link URL, you can gain valuable insights to determine if it is safe to proceed further. Remember, if something feels off or suspicious, it’s always best to err on the side of caution and avoid clicking on the link. Trusting your instincts and practicing safe browsing habits are essential in protecting yourself from potential online threats.
Step 3: Use an Online Link Scanner
As part of your effort to determine the safety of a suspicious link, utilizing an online link scanner can provide an added layer of protection. Link scanners are tools designed to analyze and evaluate the security of URLs, helping you identify potential threats or malicious content.
Start by searching for reputable online link scanner services. There are several well-known options available, such as VirusTotal, URLVoid, or Google Safe Browsing. These services employ advanced algorithms and databases to check the link against known lists of malicious URLs and websites.
Once you have selected an online link scanner, access their website and locate the provided scanning feature or input field. Simply paste the suspicious link into the scanning tool and initiate the scan. The tool will then analyze the link and provide a report on its findings.
The link scanner will typically evaluate various aspects of the link, including the reputation of the domain, any associated malware or phishing attempts, and the presence of any suspicious or harmful content. The scanner will compare the link against its database and inform you of any potential risks.
Keep in mind that while online link scanners are useful tools, they are not foolproof. It’s still important to exercise caution and use other methods of analysis in conjunction with the link scanner. Some threats may be relatively new or not yet detected by the scanner’s database.
Additionally, note that link scanners may differ in terms of the databases they use and the extent of their scanning capabilities. Therefore, it can be beneficial to utilize multiple scanners to cross-reference the results and obtain a more comprehensive assessment.
Using an online link scanner can provide you with valuable information regarding the safety of a suspicious link. It helps you make an informed decision about whether to proceed or take necessary precautions. However, always remember that your own judgment and critical thinking are essential. If the scanner flags the link as risky, it’s best to avoid interacting with it altogether.
By incorporating online link scanners in your link analysis process, you take an active step towards safeguarding your online security and protecting yourself from potential threats.
Step 4: Search for the Domain
As part of your investigation into a suspicious link, conducting a domain search can provide valuable information about the website or organization associated with the link. Searching for the domain name can help you assess its credibility, reputation, and the likelihood of it being legitimate.
To search for the domain, start by opening a search engine of your choice, such as Google, Bing, or DuckDuckGo. Enter the domain name found in the suspicious link into the search bar and initiate the search. The search engine will then display the search results related to that domain.
Pay attention to the search results and review the information provided. Look for any indications of the domain being associated with fraudulent activities, scams, or malware. Negative reviews or reports from other users can be a strong warning sign.
Furthermore, explore the official website of the organization or business if it is available. Navigate through its pages to gather more information about its services, contact details, and credibility. Legitimate websites often provide clear and comprehensive information about their purpose and activities.
Additionally, research the reputation and online presence of the company or organization connected to the domain. Check for customer reviews, ratings, and feedback on trusted platforms or forums. If there is limited information available or a lack of positive reviews, it could be an indication of a potentially suspicious or unreliable domain.
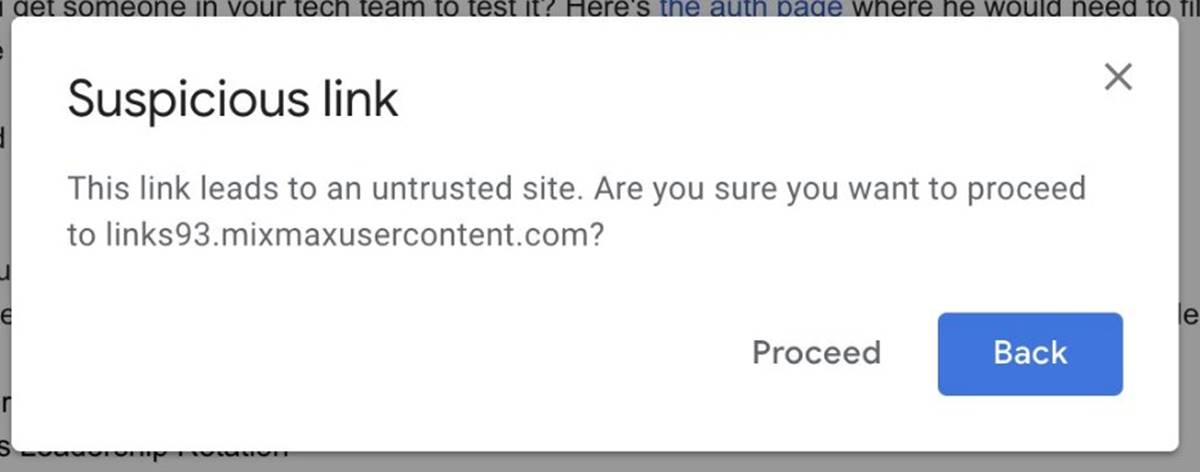
Furthermore, make sure to pay attention to any warnings or alerts from search engines or cybersecurity companies about the domain. Browser warnings or security software notifications may indicate that the website associated with the link has been flagged as untrustworthy or potentially harmful.
By searching for the domain, you can gather valuable insights and make an informed decision about the trustworthiness of the website. If the search results reveal negative information or if the domain appears to be associated with suspicious activities, it is best to avoid clicking on the link to protect yourself from potential risks.
Remember, taking the time to investigate the domain is an essential step in identifying and avoiding potentially harmful links. It allows you to make informed decisions about the safety of the website and protects you from falling victim to scams, malware infections, or other online threats.
Step 5: Analyze the Link Anchor Text
When evaluating a suspicious link, it’s essential to analyze the link’s anchor text. Anchor text refers to the clickable text that appears as a link, usually highlighted in blue and underlined. This text provides important clues about the destination of the link and can help you determine its legitimacy.
Start by examining the anchor text itself. Legitimate links typically have descriptive anchor text that accurately reflects the content of the destination page. For example, a trustworthy link to an article about SEO writing would likely have anchor text like “SEO writing best practices” or “ultimate guide to SEO writing.”
If the anchor text seems vague, generic, or irrelevant to the content of the link, it could be a warning sign. Suspicious links often use generic anchor text like “click here” or “check this out,” as they are designed to grab attention without providing any real information about the link’s destination.
Be cautious of anchor text that uses overly sensational language or makes unrealistic promises. Phrases like “amazing deal,” “exclusive offer,” or “guaranteed results” should raise your skepticism. Legitimate links tend to be more informative and straightforward in their language.
Additionally, look out for anchor text that appears to be deliberately misleading or deceptive. Malicious actors may use anchor text that disguises the true destination of the link. For example, a link that claims to lead to a reputable news article but actually directs you to a phishing website.
It’s important to note that even if the anchor text appears reliable, it’s still crucial to follow the other steps outlined in this guide to thoroughly evaluate the link’s safety. Attackers can craft anchor text that seems genuine while directing users to malicious websites or dangerous content.
By analyzing the link’s anchor text, you can gain insights into the link’s legitimacy and make an informed decision about whether or not to click on it. If the anchor text raises any suspicion or seems misleading, it’s best to exercise caution and avoid interacting with the link. Trustworthy links should have clear and relevant anchor text that aligns with the content they lead to.
Always remember that your own judgment and critical thinking are crucial when assessing the safety of suspicious links. Rely on multiple factors, including the link’s URL, context, and other analysis techniques, to ensure you’re making an informed decision that protects your online security.
Step 6: Look for Red Flags in the Link Description
When evaluating a suspicious link, it’s important to carefully examine the accompanying link description or text that provides additional information about the link’s destination. This description can give you important clues about the legitimacy and credibility of the link.
Start by reading the link description thoroughly. Legitimate links often have clear and concise descriptions that accurately describe the content of the linked page. For example, a trustworthy link to a blog post about healthy recipes may have a description like “Discover delicious and nutritious recipes for a healthy lifestyle.”
Be wary of link descriptions that are overly enticing or use exaggerated claims. Suspicious links often employ clickbait tactics to lure users into clicking on them. Phrases like “amazing secret revealed” or “unbelievable results guaranteed” should raise your suspicion.
Watch out for links that claim to offer exclusive or insider information. Cybercriminals often use deceptive techniques to trick users into clicking on links by promising access to confidential information or leaked content. Be skeptical of such claims and consider the sources of the links carefully.
Additionally, be cautious if the link description contains grammatical errors, misspellings, or awkward sentence structures. Legitimate links are typically professionally written and reviewed for accuracy. Poorly-written descriptions could be a sign of a potentially suspicious or untrustworthy link.
Furthermore, look out for links that include irrelevant or unrelated information. If the description does not provide any valuable context or seems disconnected from the content you were expecting, it could be an indicator of a potentially harmful link.
It’s important to remember that the link description should align with the purpose and content of the link. When in doubt, consider utilizing other analysis techniques in conjunction with examining the link description.
By scrutinizing the link description, you can gather valuable insights and make an informed decision about the safety of clicking on the link. If the description raises any suspicions or seems misleading, it’s best to exercise caution and avoid interacting with the link. Trustworthy links should have clear and relevant descriptions that accurately reflect the content they lead to.
Always rely on your own judgment and critical thinking when evaluating suspicious links. Consider the link’s accompanying information, URL, context, and other analysis techniques to ensure that you’re making a well-informed decision and protecting yourself from potential online threats.
Step 7: Hover Over the Link
In your evaluation of a suspicious link, an essential step is to hover over it to reveal the link’s actual destination. This simple action can provide valuable information about where the link will take you and help you assess its safety.
To hover over a link, position your mouse cursor over the link without clicking. As you do this, pay attention to the bottom-left corner of your browser window or the status bar (depending on your browser). It will typically display the URL associated with the link.
The revealed URL should match or closely resemble the text or content of the link. Legitimate links will generally show a URL that corresponds to the domain or website associated with the link. For example, if the link text says “example.com” but the displayed URL shows a different website entirely, it could indicate a potentially malicious link.
Hovering over the link can also help you identify longer or truncated URLs. Cybercriminals often use techniques such as URL shorteners or redirect links to hide the actual destination of the link. If the displayed URL appears excessively long, contains random characters, or seems unrelated to the content, exercise caution.
Furthermore, examining the URL that appears when hovering over the link allows you to spot any misspellings or minor variations in the domain name. Phishing links often utilize similar-looking or visually deceptive URLs to trick users. By closely inspecting the actual URL, you can detect such attempts to mislead or deceive.
It’s important to note that while hovering over the link can provide significant insights, it is not foolproof. Sophisticated attackers may employ advanced techniques to manipulate the displayed URL or hide malicious intentions. Therefore, it is recommended to combine this step with other analysis techniques outlined in this guide.
By hovering over the link, you gain valuable information about the link’s actual destination and can make an informed decision about its safety. If the displayed URL raises any suspicions, differs greatly from the link text, or seems unrelated to the content, it is best to exercise caution and avoid interacting with the link.
Always rely on your own judgment and critical thinking to assess links. Use the information gathered from hovering along with other analysis techniques to ensure you’re making a well-informed decision and protecting yourself from potential online threats.
Step 8: Check for Misspellings or Random Characters in the Link
When evaluating a suspicious link, it’s crucial to check for any misspellings or random characters that may be present in the link. Cybercriminals often use these techniques to create deceptive links that appear similar to legitimate ones, aiming to trick unsuspecting users into clicking on them.
Start by carefully examining the link for any misspelled words or variations in the domain name. Attackers may intentionally substitute a letter with a similar-looking character or use slight misspellings to create URLs that resemble well-known websites. For example, an attacker might use “gogle.com” instead of “google.com” in an attempt to deceive users.
Be particularly vigilant when evaluating links that contain randomly generated characters or long strings of numbers. Such links are often used by cybercriminals to obfuscate the actual destination of the link. Legitimate links typically have concise and meaningful URLs that reflect the content of the linked page.
If the link contains additional words or phrases that are unexpected or seem unrelated to the content, exercise caution. Cybercriminals may insert catchy phrases or attention-grabbing words to increase the likelihood of users clicking on the link. Analyze the link to ensure that it aligns with your expectations and intentions.
It’s important to note that even links from seemingly legitimate sources can contain misspellings or random characters. Therefore, carefully evaluate the overall context and other factors in conjunction with this step to form a comprehensive assessment.
By checking for misspellings or random characters in the link, you can identify potential attempts at deception or fraudulent activity. If you notice any irregularities, it is best to exercise caution and avoid interacting with the link. Trustworthy links should have clear, properly spelled URLs that reflect the legitimacy of the website or page.
Remember to always trust your judgment and utilize multiple analysis techniques to evaluate the safety of suspicious links. By doing so, you can protect yourself from falling victim to scams, phishing attempts, or other online threats.
Step 9: Inspect the Link’s Source Code
Inspecting the source code of a suspicious link can provide you with valuable insights into its structure, functionality, and potential hidden elements. While this step requires some technical knowledge, it can be helpful in identifying any malicious or suspicious components that may not be apparent at first glance.
To inspect the source code, right-click on the link and select “Inspect” or “Inspect Element” (depending on your browser). This will open the browser’s developer tools, with the link’s HTML code displayed.
Start by looking for any embedded scripts or JavaScript code associated with the link. Malicious actors often use scripts to execute harmful actions, such as redirecting to a phishing site or downloading malware. If you notice any unfamiliar or suspicious scripts, it is best to proceed with caution.
Inspect the hyperlink tags (“) surrounding the link. Check if there are any additional attributes or properties that could indicate suspicious behavior. Be wary of attributes such as `onclick` or `onmouseover`, as they could trigger unwanted actions when you interact with the link.
Look for any hidden elements or additional URLs within the source code. Cybercriminals may conceal links or malware downloads within the HTML code. Pay attention to any elements that are set to `display: none;` or have positioning that makes them invisible to users.
Additionally, analyze the link’s parameters or query strings. These are usually appended to the end of the URL and may contain data used by the website. Be cautious if the parameters seem unusual or contain random characters. Attackers may use them to transmit sensitive information or execute malicious actions.
It’s important to note that inspecting the source code requires some technical knowledge and understanding of HTML. If you’re unfamiliar with reading or interpreting source code, it may be best to seek assistance from a technical expert or avoid interacting with links that require this level of analysis.
By inspecting the link’s source code, you can gain valuable insights into its structure and functionality. While this step may not be necessary for every suspicious link, it can provide additional evidence in confirming its safety or identifying potential risks.
Remember, inspecting the source code is just one of several steps in evaluating a suspicious link. Combine it with other analysis techniques and trust your judgment to make an informed decision about whether to proceed or exercise caution when encountering suspicious links.
Step 10: Consult Antivirus Software
When dealing with suspicious links, it is crucial to leverage the power of antivirus software to detect and protect against potential threats. Antivirus software is specially designed to identify and block malicious files, websites, and links that may pose a risk to your computer and online security.
Ensure that you have reliable and up-to-date antivirus software installed on your device. This software continuously scans your system for malware and offers real-time protection against various types of threats, including those that may be hidden within suspicious links.
If you encounter a suspicious link, consult your antivirus software for further analysis. Start by copying the link and pasting it into the antivirus software’s scanning or analysis feature. The software will scan the link and provide you with information about its potential risks.
Antivirus software usually uses a combination of signature-based detection and behavior-based analysis to identify malicious links. It compares the link against a vast database of known threats and analyzes its behavior to detect any suspicious activity or patterns.
Pay attention to the results provided by the antivirus software. It may categorize the link as safe, potentially unsafe, or outright malicious. The software may provide additional details about the nature of the threat or recommend actions to take, such as blocking or removing the link.
While antivirus software is an effective tool in combating cybersecurity threats, it is important to note that it may not catch all types of malicious links. Cybercriminals are continually devising new methods to evade detection. Therefore, combining antivirus software with other analysis techniques outlined in this guide is essential to ensure comprehensive protection.
Regularly update your antivirus software to ensure it has the latest virus definitions and security patches. New threats emerge regularly, and software updates help to mitigate these risks effectively.
Remember, antivirus software should be considered a vital part of your overall cybersecurity strategy. By leveraging its capabilities to scan and analyze suspicious links, you can significantly reduce the risks associated with clicking on potentially harmful links and ensure the continued security of your device and personal information.