Privacy Advocates
Privacy advocates are individuals and organizations that promote and defend the right to privacy in the digital age. They believe that strong encryption is crucial for safeguarding personal information and protecting individuals’ privacy rights. Encryption is a method of encoding data to prevent unauthorized access, ensuring that only the intended recipient can decipher the information.
One of the primary reasons privacy advocates support strong encryption is to protect personal data from hackers and cybercriminals. In today’s interconnected world, where sensitive information is stored and transmitted online, encryption acts as a shield against potential security breaches. It ensures that even if a hacker manages to intercept the data, it remains unintelligible and useless without the proper decryption keys.
Moreover, strong encryption plays a vital role in preventing unauthorized access to individuals’ online communication and digital activities. It ensures that only the intended parties can view and understand the content of private messages, emails, files, and other online interactions. This level of privacy is particularly crucial for activities such as online banking, healthcare transactions, and confidential business communications.
For privacy advocates, encryption is not just about protecting personal information; it is also about maintaining the fundamental right to privacy in the face of increasing government surveillance. With the advancements in technology, governments have gained unprecedented capabilities to monitor and collect citizens’ digital data.
Privacy advocates argue that strong encryption is essential to limit the reach of government surveillance and prevent potential abuses of power. By encrypting their online communications and data, individuals can maintain a level of privacy that is necessary for democratic societies to function effectively.
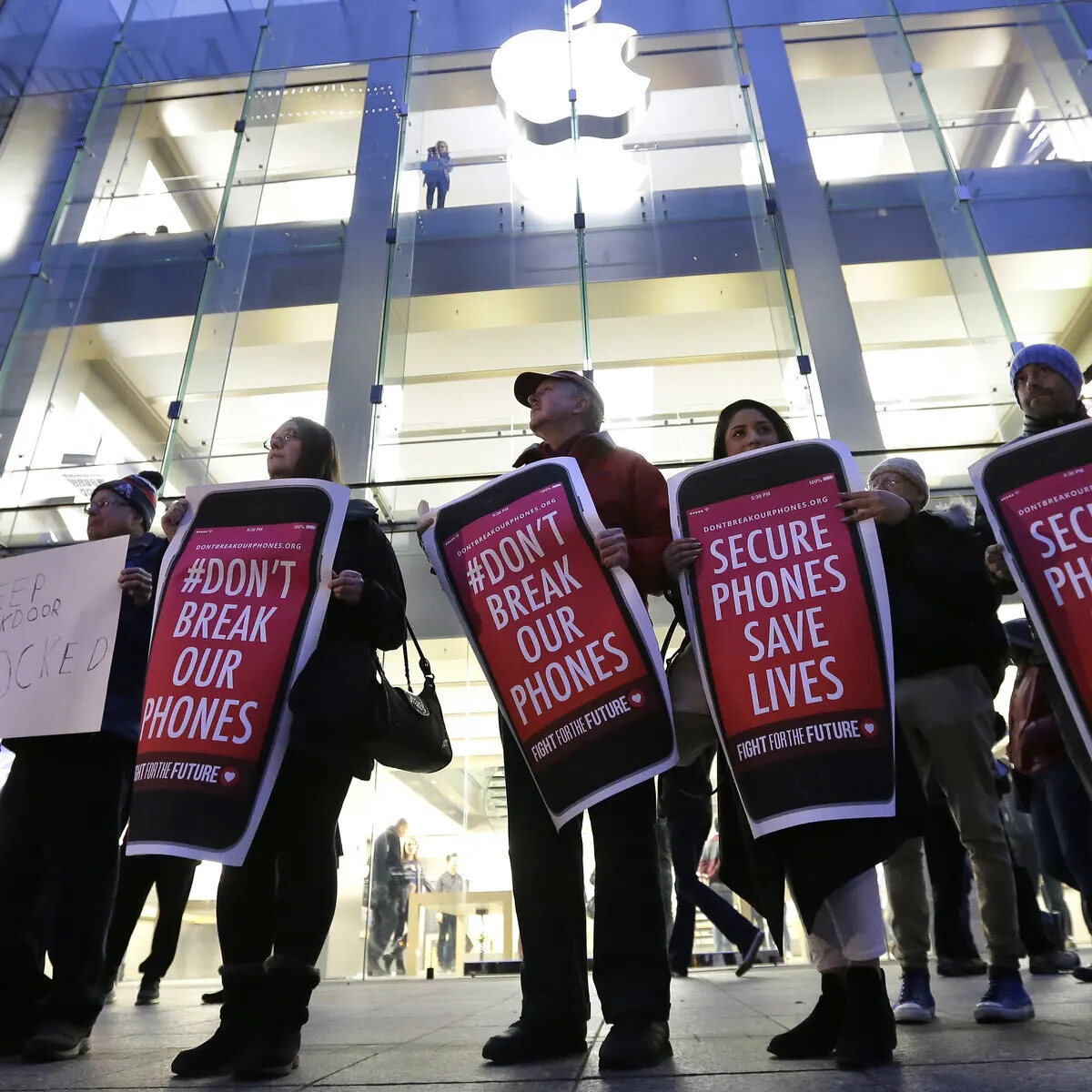
In recent years, the debate between privacy advocates and law enforcement agencies, such as the Federal Bureau of Investigation (FBI), has become more prominent. While privacy advocates argue for robust encryption, the FBI has expressed concerns about the potential barriers it poses to their investigations.
However, it is important to note that privacy advocates’ support for strong encryption does not mean they are opposed to law enforcement. They acknowledge the necessity of effective law enforcement to maintain public safety and combat criminal activities. The key issue lies in finding a balance between preserving individual privacy and providing law enforcement with the tools they need to investigate and prevent crimes.
The debate over encryption and privacy continues to evolve as technology advances and new legal challenges arise. In the next sections, we will explore the importance of strong encryption, the concerns around government surveillance, and the perspectives of both privacy advocates and the FBI.
The Importance of Strong Encryption
Strong encryption is of paramount importance in today’s digital landscape. It plays a crucial role in safeguarding sensitive information, protecting privacy, and ensuring the integrity and security of online communication and transactions.
One of the primary reasons for the importance of strong encryption is its ability to protect personal data from unauthorized access. In an era where cybercrime is on the rise, encryption serves as a vital defense mechanism against hackers and malicious actors. By encrypting data, it becomes virtually impossible for unauthorized individuals to decipher the information without the correct encryption keys. This is particularly crucial for sensitive data such as financial records, healthcare information, and personal communication.
Encryption also enhances the security of online transactions, such as e-commerce and online banking. It ensures that confidential information, such as credit card details and financial transactions, remains secure and protected from interception and fraudulent activities. Strong encryption protocols provide a layer of trust and assurance to both businesses and consumers, fostering a safer online environment.
Moreover, encryption is the backbone of secure communications. Individuals, businesses, and organizations rely on encrypted messaging platforms and email services to ensure the privacy and confidentiality of their conversations. Without strong encryption, sensitive information communicated over digital channels would be vulnerable to eavesdropping and interception by unauthorized parties.
Strong encryption is also vital for protecting national security and critical infrastructure. Governments, military organizations, and intelligence agencies utilize encryption to protect classified information and communications from foreign adversaries and cybercriminals. It ensures that any attempts to infiltrate or gather intelligence on sensitive matters are met with an impenetrable barrier.
Additionally, encryption plays a vital role in maintaining trust and preserving civil liberties in a democratic society. Individuals have the right to privacy and freedom of expression, and strong encryption safeguards these fundamental rights. It prevents unwarranted surveillance and ensures that individuals can communicate and express themselves without the fear of their messages being intercepted or compromised.
As technology continues to advance, so do the threats and challenges faced in the digital realm. Encryption acts as a crucial line of defense against cyber threats, protecting individuals, businesses, and even governments from potential data breaches, identity theft, and other malicious activities.
Protecting Personal Data
In today’s digital age, the importance of protecting personal data cannot be overstated. With the increasing prevalence of online platforms and services, individuals are constantly sharing their personal information, from sensitive financial details to intimate personal messages. Strong encryption plays a vital role in ensuring the security and confidentiality of personal data.
One of the key reasons why strong encryption is crucial for protecting personal data is the ever-present threat of data breaches. Cybercriminals constantly target databases and systems that store large amounts of personal information, such as credit card numbers, social security numbers, and addresses. Encryption ensures that even if a breach occurs, the stolen data remains unreadable and unusable to unauthorized individuals. It acts as a safety net, providing an extra layer of protection against potential privacy violations.
Moreover, encryption is essential for maintaining the privacy of personal communications and messages. In an era where individuals rely heavily on digital platforms for communication, ensuring that messages remain confidential and secure is of utmost importance. For example, end-to-end encryption in messaging apps ensures that only the intended recipients can access and understand the content of the messages. This protects individuals from unauthorized surveillance and ensures the privacy of their conversations.
Encryption also plays a vital role in securing data transmitted over public networks. Public Wi-Fi networks, for instance, are vulnerable to interception and eavesdropping by cybercriminals. By employing encryption protocols, individuals can protect their data from being intercepted and accessed by unauthorized individuals while connected to these networks. This is particularly important when transmitting sensitive information, such as passwords or financial details, over public networks.
Additionally, strong encryption safeguards personal data stored on devices, such as smartphones, laptops, and tablets. These devices contain a plethora of personal information, including contacts, photos, emails, and documents. Encryption ensures that if the device is lost, stolen, or accessed without authorization, the data remains encrypted and inaccessible to the thief or anyone who does not possess the encryption keys.
Furthermore, encryption is crucial for compliance with data protection laws. Many jurisdictions have implemented regulations requiring organizations to protect personal data and maintain the privacy of their customers. Encryption provides organizations with a means to comply with these laws by securing the data they collect and process. Implementing encryption measures not only protects individuals’ data but also helps organizations avoid legal repercussions and reputational damage.
Overall, protecting personal data is essential in today’s digital landscape. Strong encryption acts as a crucial tool for safeguarding personal information, maintaining privacy, and mitigating the risks associated with data breaches and unauthorized access. It provides individuals with the confidence that their data remains confidential and secure, ensuring peace of mind in an increasingly interconnected world.
Preventing Unauthorized Access
In an era where digital information is more valuable than ever, preventing unauthorized access to sensitive data has become a top priority. Strong encryption is a powerful tool in the fight against unauthorized access, providing individuals and organizations with a robust defense mechanism to protect their valuable information.
One of the primary ways encryption prevents unauthorized access is through the use of encryption keys. Encryption involves converting plaintext data into ciphertext using mathematical algorithms. To decrypt the ciphertext and access the original data, a specific encryption key is required. Without the correct key, the encrypted data remains indecipherable, rendering it useless to anyone who gains unauthorized access. This ensures that even if unauthorized individuals obtain the encrypted data, they cannot read or misuse it.
Encryption also acts as a barrier against unauthorized access by adding an additional layer of security to digital communication networks. For example, virtual private networks (VPNs) utilize encryption to create secure connections between users and the internet. This ensures that any information transmitted between the user and the VPN server remains encrypted and protected from potential eavesdroppers or attackers on the network. By preventing unauthorized access to sensitive data in transit, encryption ensures the integrity and confidentiality of the communication.
Moreover, encryption plays a vital role in safeguarding data stored on devices such as smartphones, laptops, and servers. By encrypting the data stored on these devices, unauthorized individuals cannot access the information even if they gain physical access to the device. In the event of theft or loss, encryption ensures that personal and confidential data remains secure and protected from unauthorized exploitation.
Encryption is also crucial in securing data backups and cloud storage. By encrypting backups and data stored in the cloud, organizations can prevent unauthorized access to sensitive information in case of a security breach or unauthorized attempts to access the backup or cloud storage provider’s systems. This adds an extra layer of protection to ensure the confidentiality and integrity of the data, even if it is stored in remote locations.
Additionally, encryption is crucial in preventing unauthorized access to sensitive information in sectors such as healthcare and finance, where privacy and security are of utmost importance. Healthcare institutions encrypt patient medical records to protect personal health information from unauthorized access. Financial institutions leverage encryption to secure sensitive data, including account details and financial transactions, preventing unauthorized access and fraudulent activities.
Overall, preventing unauthorized access to sensitive data is vital in maintaining privacy, protecting against cyber threats, and preserving the integrity of digital systems. Encryption serves as a powerful mechanism to ensure that only authorized individuals can access and understand the data, adding robust security measures to safeguard confidentiality and prevent unauthorized exploitation of valuable information.
Encryption and Cybersecurity
Encryption plays a critical role in the realm of cybersecurity, providing a powerful defense against cyber threats and ensuring the integrity and confidentiality of digital information. It is an essential tool that strengthens the overall security posture of individuals, businesses, and organizations in the face of ever-evolving cyber threats.
One of the primary ways encryption enhances cybersecurity is by protecting data in transit. When data is transmitted over the internet or other networks, it is vulnerable to interception and eavesdropping by malicious actors. Encryption ensures that the data remains encrypted during transmission, making it unreadable to unauthorized individuals. This prevents cybercriminals from accessing sensitive information and minimizes the risk of data breaches and interception attacks.
Moreover, encryption strengthens the security of data at rest. Data stored on devices, servers, or cloud platforms are potential targets for cyber attacks. By encrypting the data, unauthorized individuals who gain access to these systems will find the encrypted data unreadable and useless. Encryption adds an essential layer of protection by ensuring that even if the systems are compromised, the data remains secure and inaccessible to the attackers.
Effective encryption is also crucial in protecting passwords and user credentials. Passwords are often the primary line of defense for online accounts and systems. However, weak or easily guessable passwords can compromise security. Encryption methods such as hashing and salting help protect passwords by encrypting them and making them more resistant to brute force attacks and password cracking techniques.
Encryption is also integral to securing sensitive information stored within databases. Encrypting specific fields, such as credit card numbers or social security numbers, ensures that even if unauthorized access to the database occurs, the sensitive information remains protected. This protects individuals from identity theft and minimizes the impact of data breaches.
Additionally, encryption serves as a deterrent to unauthorized modification of data. By using encryption and digital signatures, individuals and organizations can verify the integrity of data and detect any unauthorized changes. This is particularly important for critical systems that require assurance of data integrity, such as financial transactions or government records.
Furthermore, encryption plays a role in protecting intellectual property and trade secrets. By encrypting sensitive documents, source code, or proprietary information, companies can safeguard their valuable assets from unauthorized access or theft. Encryption helps maintain the confidentiality and competitive advantage of businesses, particularly in industries where intellectual property is significant.
Overall, encryption is a fundamental component of cybersecurity. It provides an invaluable layer of protection against cyber threats, ensuring the confidentiality, integrity, and availability of sensitive data. By encrypting data in transit, at rest, and protecting passwords and user credentials, encryption strengthens the overall security posture and helps mitigate the risks associated with cyber attacks.
Government Surveillance Concerns
The rise of digital communication and advanced technologies has sparked concerns about the extent of government surveillance and its implications for personal privacy and civil liberties. As governments employ various measures to monitor and collect citizens’ digital data, individuals and privacy advocates have raised significant concerns regarding the potential encroachment on privacy rights and the potential abuse of power.
One of the primary concerns surrounding government surveillance is the invasion of personal privacy. With the ability to intercept and monitor digital communications, governments have unprecedented access to individuals’ private conversations, emails, browsing history, and social media activities. This level of surveillance raises questions about the balance between national security and individual privacy, as well as the potential chilling effects it may have on freedom of expression and dissent.
Furthermore, the mass collection and storage of personal data by governments raise concerns about data security and the potential for unauthorized access or misuse. The more extensive the surveillance apparatus, the larger the repositories of personal information become. The risk of data breaches or leaks, as well as the potential for abuse by government officials or third parties with access to this data, raises serious concerns about the security and confidentiality of individuals’ personal information.
Government surveillance also raises questions about the transparency and accountability of surveillance practices. Transparency is crucial to maintaining the trust of citizens and ensuring that surveillance measures are used appropriately and within the bounds of the law. Without sufficient transparency and oversight, there is an increased risk of power abuse, targeting of specific individuals or groups, and the violation of privacy rights.
Another concern is the potential chilling effect on free speech and the exercise of democratic freedoms. The knowledge that one’s online activities and communications are being monitored can have a detrimental impact on individuals’ willingness to express their opinions freely or engage in dissenting discourse. This surveillance dynamic can dampen political engagement and hinder the free exchange of ideas, which are essential components of democratic societies.
Moreover, the global nature of digital communications and government surveillance has raised questions about jurisdictional boundaries and international cooperation. With different legal frameworks and surveillance capabilities across countries, concerns arise regarding the potential for governments to bypass privacy protections by accessing data stored in other jurisdictions. This undermines the notion of privacy as a universal human right and presents challenges in reconciling different approaches to surveillance and information sharing.
Overall, government surveillance concerns are centered around the potential intrusion on personal privacy, data security, transparency, accountability, and the impact on democratic freedoms. Striking a balance between necessary security measures and upholding civil liberties remains a complex challenge that requires ongoing public debate, legal safeguards, and robust oversight mechanisms.
The FBI’s Perspective
The Federal Bureau of Investigation (FBI) plays a vital role in investigating and preventing criminal activities, including terrorism, cybercrimes, and organized crime. From the FBI’s perspective, strong encryption presents challenges and concerns that impact their ability to effectively carry out their missions.
One of the key concerns the FBI raises regarding strong encryption is its potential to impede their investigations. Encryption technology can make it extremely difficult, if not impossible, for law enforcement agencies to access encrypted data, even with proper legal authorization. This can hinder investigations into serious crimes, such as terrorism or child exploitation, where timely access to encrypted information may be crucial in preventing harm or saving lives.
The FBI also highlights the increasing use of encryption by criminals, particularly in relation to communication platforms and devices that provide end-to-end encryption. These encryption methods can serve as a safe haven for criminals, shielding their communication and evading law enforcement surveillance. As criminal activities become increasingly sophisticated and reliant on encryption, the FBI argues that they need the necessary tools and capabilities to access encrypted data in order to protect public safety.
Furthermore, the FBI raises concerns about the use of encryption by organized crime groups and criminal networks. Strong encryption can make it challenging for law enforcement agencies to gather intelligence, monitor activities, and disrupt these criminal operations effectively. From their perspective, the inability to access encrypted communications and information can hinder the investigation and prosecution of criminal enterprises that pose significant threats to national security and public safety.
Additionally, the FBI emphasizes the importance of finding solutions that balance privacy rights with public safety. While acknowledging the significance of privacy protections, the FBI argues that strong encryption should not be absolute and impenetrable. They suggest that lawful access to encrypted data, under appropriate legal authorization and oversight, is essential for effective crime prevention and investigation. They advocate for addressing the issue of “going dark,” where encryption hinder the ability of law enforcement to access critical information needed for investigations.
From the FBI’s perspective, collaboration and cooperation between technology companies, policymakers, and law enforcement agencies are essential to find solutions that maintain the benefits of strong encryption while enabling lawful access for legitimate investigative purposes. They propose the exploration of alternative approaches such as developing lawful access capabilities or implementing mechanisms that allow for the retrieval of encrypted data with proper authorization.
It is important to recognize that the FBI’s perspective on encryption is driven by their mandate to protect national security, combat crime, and ensure public safety. Their concerns about the challenges encryption presents should be considered in the broader conversation surrounding privacy, civil liberties, and the potential trade-offs involved in finding a balance between security and individual rights.
Balancing Privacy and National Security
The balance between privacy and national security is a complex and delicate challenge faced by governments and societies worldwide. Privacy is a fundamental human right that safeguards individuals’ personal information and ensures freedom from unwarranted intrusion, while national security encompasses activities aimed at protecting the safety and well-being of a nation and its citizens. Striking the right balance between these two objectives is essential to maintain a democratic society while addressing security concerns.
From a privacy standpoint, individuals have the right to control their personal information and maintain privacy in their digital interactions. Privacy advocates argue that strong encryption is necessary to safeguard personal data and protect against unauthorized surveillance and data breaches. They emphasize the importance of upholding privacy rights as an essential component of individual freedom and autonomy.
On the other hand, national security considerations require governments to implement measures to prevent and investigate threats to public safety and protect vital interests. Law enforcement agencies, including intelligence and security services, argue that certain circumstances call for lawful access to encrypted data. They contend that access to encrypted communications and information is necessary to protect against criminal activities, terrorism, and other security threats.
Striking the balance between privacy and national security involves finding solutions that do not unduly compromise one at the expense of the other. It requires open dialogue and collaboration between technology companies, policymakers, and law enforcement agencies to address the challenges posed by encryption effectively while respecting individual privacy rights.
Transparency and oversight are crucial mechanisms for ensuring that privacy and security measures are implemented responsibly. Clear legal frameworks and judicial oversight mechanisms can help to prevent abuses of power and ensure that any access to encrypted data is subject to proper authorization and judicial review. This helps maintain trust in government actions and ensures accountability in balancing privacy and national security interests.
The debate surrounding encryption often centers around the concept of “backdoors” or deliberately weakened encryption methods that allow law enforcement access to encrypted data. Privacy advocates argue that introducing backdoors compromises the security and integrity of encryption, leaving individuals vulnerable to hacking and unauthorized access. They contend that weakened encryption measures erode trust and set dangerous precedents that can be exploited by malicious actors.
Both privacy advocates and law enforcement agencies recognize the need for solutions that strike a balance between respecting privacy and enabling legitimate investigative access when necessary. Instead of backdoors, alternative approaches such as exploring lawful access solutions or facilitating secure methods for providing limited access to encrypted data may offer potential paths forward.
The delicate task of balancing privacy and national security requires ongoing dialogue and collaboration. It is essential to consider the broad societal implications, seek input from experts in various fields, and engage in public discourse to ensure that decisions are well-informed and take into account the viewpoints of all stakeholders involved.
The Debate over Backdoors
The debate over backdoors in encryption has been a contentious issue in the ongoing discussion on privacy, security, and the role of law enforcement. A backdoor refers to a deliberate vulnerability or weakened encryption method inserted into a system, allowing authorized parties, typically law enforcement, to access encrypted data. The concept of backdoors has sparked significant debate among experts, policymakers, and privacy advocates, with varying perspectives on their efficacy, security implications, and potential impact on individual privacy rights.
Proponents of backdoors argue that they are necessary for law enforcement to gain access to encrypted information in investigations relating to serious crimes, terrorism, and national security threats. They contend that backdoors can help prevent criminal activities and ensure the safety and security of the public. They argue that lawful access mechanisms are essential to protect society and enable effective law enforcement in the digital age.
However, privacy advocates and cybersecurity experts have raised significant concerns regarding the implementation of backdoors. They argue that introducing intentional vulnerabilities into encryption undermines the overall security and integrity of the technology. Any vulnerability, intentional or not, can be exploited by malicious actors, from hackers to state-sponsored adversaries, weakening the security for all users. Additionally, weakened encryption methods can potentially expose personal and sensitive data to unauthorized access, leading to identity theft, fraud, and other detrimental consequences.
Privacy advocates also argue that backdoors fundamentally disrupt the notion of privacy as a fundamental human right. They contend that individuals should have the right to protect their personal information from unwarranted surveillance, even when it comes to legitimate law enforcement investigations. They warn against the potential for abuse or misuse of backdoors, with concerns about government overreach, mass surveillance, and the erosion of trust between individuals and technology companies.
Another aspect of the debate revolves around the global nature of encryption. Encryption is a technology that transcends borders, and different countries have varying perspectives on backdoors. Implementing backdoors in one jurisdiction could have implications for users and companies globally, potentially harming the security and privacy of innocent individuals. The implementation of backdoors also raises concerns about the potential abuse of such vulnerabilities by authoritarian regimes, further compromising the safety and rights of individuals in repressive societies.
Moreover, critics argue that the focus on backdoors detracts from developing alternative solutions that prioritize both privacy and security. Encouraging the use of strong encryption, supporting law enforcement in developing alternative investigative techniques, and investing in advanced tools and techniques may offer viable pathways to balancing privacy and security without compromising encryption integrity.
The debate over backdoors is unlikely to reach a consensus any time soon. It requires ongoing discussions involving experts, policymakers, technology companies, and civil society to find the right balance between privacy, security, and law enforcement. Striving for solutions that preserve the benefits of encryption while enabling necessary investigative access remains a significant challenge for all stakeholders involved.
Legal Challenges and Court Orders
The debate surrounding encryption and privacy is not limited to the realm of policy and technology. Legal challenges and court orders play a crucial role in shaping the landscape of encryption and determining the extent of government access to encrypted data. The complexity of balancing privacy rights and law enforcement needs is often addressed through legal frameworks and court decisions.
One of the key legal challenges in the context of encryption is the question of whether individuals have a right to encrypt their data and communications without interference from the government. Many countries recognize privacy as a fundamental right, and this includes the right to use encryption to protect personal information. Legal frameworks are continually evolving to ensure that individuals can have a reasonable expectation of privacy, even in the face of emerging technologies and complex encryption methods.
However, legal challenges also arise when law enforcement agencies seek access to encrypted data for criminal investigations. In such cases, court orders can be issued, compelling technology companies or individuals to provide access to encrypted information. The judiciary plays a crucial role in determining the legality and scope of such orders, preserving individual privacy rights while considering the legitimate needs of law enforcement.
Legal challenges related to encryption often revolve around the concept of “going dark,” where encryption inhibits law enforcement’s ability to access crucial evidence. This issue has been widely debated in various jurisdictions, leading to court battles and legal precedents that shape the parameters of encryption and government access. Courts must carefully balance the importance of privacy rights and the need for effective law enforcement, weighing the potential impact on individual privacy against broader public safety interests.
Moreover, the international dimension of encryption presents additional legal challenges. Different countries have varying approaches to encryption and government access, leading to complex legal scenarios when data flows across borders. Companies may face conflicting legal requirements from different jurisdictions, creating a tension and potential conflicts of law. Ensuring consistency and harmonization in legal frameworks remains a challenge in the globalized digital era.
Legal challenges related to encryption have led to important court decisions that have set precedents and refined the legal interpretation of privacy and security. These court decisions significantly influence the extent of government access to encrypted data and the responsibilities of technology companies and individuals in providing such access.
It is noteworthy that striking the right balance through legal means is an ongoing process, constantly reassessed as technology evolves and societal perspectives shift. Courts must adapt to changing circumstances, carefully examining the nuances and complexities brought forth by encryption technology and its impact on privacy and law enforcement needs.
Legal challenges and court orders represent essential avenues for addressing the complexities and inherent tensions surrounding encryption and privacy. They provide opportunities for deliberation and the development of legal frameworks that balance privacy rights, law enforcement needs, and ensure that the rule of law is upheld in the digital age.
International Perspectives on Encryption
The debate surrounding encryption and the balance between privacy and security extends beyond national borders. Different countries and regions hold varying perspectives on encryption, reflecting diverse cultural, legal, and policy considerations. The international landscape regarding encryption provides valuable insights into the global approach to privacy, security, and law enforcement.
Some countries embrace strong encryption as a fundamental tool for protecting individual privacy and upholding civil liberties. In these jurisdictions, encryption is seen as a necessary component of ensuring the security of personal information and fostering trust in digital technologies. Privacy is often considered a fundamental human right, and governments are cautious about implementing measures that could compromise encryption’s integrity or privacy rights.
On the other hand, certain countries emphasize security concerns and the need for government access to encrypted data for law enforcement and national security purposes. These countries may consider the risks associated with encryption, such as hindering investigations into criminal activities or terrorist threats, as more significant than individual privacy rights. They argue for measures that facilitate lawful access to encrypted data while acknowledging the challenges and vulnerabilities that weakened encryption may introduce.
The divergent perspectives on encryption have led to policy differences and legal frameworks across jurisdictions. Some countries have implemented laws mandating backdoors or weakening of encryption, while others have passed legislation explicitly protecting the right to use strong and uncompromised encryption. These policy contrasts reflect contrasting views on the balance between privacy, security, and law enforcement needs.
International cooperation and collaboration play a crucial role in addressing encryption-related challenges. Countries recognize the necessity of working together to combat transnational criminal activities, terrorism, and cyber threats. However, achieving consensus on encryption-related policies remains complex, highlighting the ongoing struggle to find common ground in balancing privacy and security interests across different legal systems and cultural contexts.
International agreements and initiatives also shape the international perspective on encryption. For example, the Wassenaar Arrangement, an international export control regime, includes provisions related to encryption technologies. The development of global standards and norms regarding encryption, privacy, and security is an active area of discussion among international organizations, industry leaders, and policymakers.
The global perspective on encryption also underlines the challenges of jurisdictional boundaries and data sovereignty. When data traverses multiple jurisdictions, conflicts arise regarding legal requirements and government access obligations. The tension between various legal frameworks poses difficulties for individuals, businesses, and governments operating in the global digital landscape.
An understanding of international perspectives on encryption is crucial for shaping effective policies, promoting global cooperation, and addressing the challenges posed by encryption technology. Recognizing the diversity of views facilitates better dialogue, collaborative solutions, and mutual understanding of the complex issues surrounding privacy, security, and the role of encryption in the digital age. Achieving a harmonized and balanced approach to encryption remains an ongoing challenge as countries continue to grapple with the multifaceted dimensions presented by this critical technology.
Encryption in the Digital Age
Encryption, often regarded as the cornerstone of digital security, plays a critical role in safeguarding personal information, protecting communication, and preserving privacy in the digital age. As the world becomes increasingly interconnected, encryption has gained prominence as an essential tool for individuals, businesses, and governments alike.
In today’s digital landscape, encryption serves multiple purposes. It protects personal data from unauthorized access, securing sensitive information such as financial records, healthcare data, and personal messages. Encryption ensures that even if data is intercepted or accessed without authorization, it remains unintelligible and useless, effectively mitigating the risks of data breaches and privacy violations.
Moreover, encryption guarantees the integrity and confidentiality of online communication. It enables individuals to exchange information securely, whether it’s through messaging platforms, email services, or financial transactions. Encryption ensures that only the intended recipients can access and understand the content, preventing eavesdropping and unauthorized surveillance.
Encryption also acts as a deterrent against cyber attacks. In a world where cybercriminals continually evolve their tactics, encryption provides a robust defense against unauthorized access, identity theft, and financial fraud. It serves as a barrier that cybercriminals must overcome, making their efforts significantly more challenging and time-consuming.
In addition to protecting personal data, encryption underpins trust in digital technologies and services. It offers individuals confidence that their information is secure, encouraging the adoption and utilization of online platforms for everything from e-commerce and banking to social networking and cloud storage. Strong encryption builds a foundation of trust necessary for the digital economy to thrive.
Encryption also plays a vital role in upholding human rights and democracy in the digital age. Privacy is an essential aspect of personal autonomy and freedom of expression. Strong encryption empowers individuals to exercise their rights without fear of unwarranted surveillance, enabling the free exchange of ideas, ensuring diversity of thought, and fostering democratic discourse.
However, encryption is not without challenges. The rapid advancement of technology brings about complex issues related to balancing privacy and security, addressing lawful access, and combating emerging threats. The ongoing debate surrounding encryption reflects the need to find the right equilibrium, taking into account the legitimate needs of law enforcement while preserving individual privacy rights.