Understanding the Importance of Hiding your Trezor Wallet
When it comes to the security of your cryptocurrency investments, one of the most important steps you can take is to ensure the privacy and protection of your Trezor wallet. While the Trezor hardware wallet already provides a high level of security, it’s crucial to implement additional measures to hide it from prying eyes. By doing so, you reduce the risk of theft and unauthorized access to your funds.
One significant advantage of hiding your Trezor wallet is that it adds an extra layer of security in case someone gains physical access to your computer or device. By concealing your wallet, you minimize the chances of an opportunistic thief getting their hands on your precious funds.
Moreover, hiding your Trezor wallet helps to maintain your privacy and anonymity, which is crucial in the world of cryptocurrency. With the increasing prevalence of cyberattacks and online surveillance, protecting your digital assets has never been more important.
Additionally, by keeping your Trezor wallet hidden, you can avoid potential awkward situations or unwanted attention. Cryptocurrency holdings can be a target for hackers or even criminals who might attempt to extort funds from you. Concealing your wallet can help you fly under the radar and reduce the likelihood of being targeted.
Furthermore, hiding your Trezor wallet is not only about physical security but also about maintaining peace of mind. Knowing that your funds are well protected and out of sight can alleviate any unnecessary stress or worry about the safety of your investments.
Overall, understanding the importance of hiding your Trezor wallet is essential for anyone looking to safeguard their cryptocurrency holdings. By implementing various strategies to keep your wallet concealed, you can enhance the security and privacy of your funds, making it more challenging for potential threats to gain access. Stay tuned as we explore various methods to hide your Trezor wallet in the following sections.
Creating a Hidden Partition on your Computer
One effective method to hide your Trezor wallet is by creating a hidden partition on your computer. This involves dividing your hard drive into two separate sections – one visible and accessible, and the other hidden and concealed.
To begin, you can utilize disk partitioning software, such as Disk Utility on macOS or Disk Management on Windows, to create a hidden partition. This hidden partition will be encrypted and inaccessible to anyone who does not have the necessary permissions or knowledge of its existence.
Once you have successfully created the hidden partition, you can install the Trezor bridge software and other necessary wallet applications exclusively on this partition. By doing so, you effectively isolate your Trezor wallet from the visible portion of your computer’s storage.
To further enhance security, you can set up a separate user account on your computer specifically for accessing the hidden partition. This user account should have a unique password, different from your regular computer login credentials.
When you’re finished using your Trezor wallet, it’s crucial to unmount or hide the hidden partition. This will make it virtually impossible for anyone to stumble upon it while using your computer. Additionally, regularly update your encryption and security measures to stay one step ahead of potential threats.
Creating a hidden partition on your computer is a great way to protect your Trezor wallet from prying eyes. By isolating your wallet in a secure and concealed area of your hard drive, you add an extra layer of security to your cryptocurrency investments.
Encrypting your Trezor Wallet Files
Another crucial step in hiding your Trezor wallet is to encrypt the wallet files themselves. Encryption adds an extra layer of protection by scrambling the data and making it unreadable without the decryption key.
There are several encryption software options available, such as VeraCrypt or BitLocker, that allow you to encrypt specific files or folders on your computer. To begin, locate the wallet files associated with your Trezor wallet and create a backup copy in a secure location.
Next, use the encryption software to encrypt the wallet files. Set a strong and unique password for the encryption, ensuring that it is a combination of letters, numbers, and special characters. Remember to keep this password secure and separate from your Trezor device.
Once the files are encrypted, you can safely store them in a hidden or secure location. This can be on an external storage device, such as a USB drive or an encrypted cloud storage service. Make sure to choose a storage solution that is reliable and offers robust security measures to protect your encrypted wallet files.
When you need to access your Trezor wallet, use the encryption software to decrypt the wallet files. Enter the password you set during the encryption process to gain access to the decrypted wallet files. Once you’re done using your wallet, remember to re-encrypt the files to keep them secure.
Encrypting your Trezor wallet files ensures that even if your computer or storage device is compromised, the encrypted files will remain inaccessible to unauthorized individuals. It adds an extra layer of security to your wallet and protects your cryptocurrency investments.
Using Cryptocurrency Mixing Services
When it comes to maintaining privacy and hiding the traceability of your cryptocurrency transactions, using cryptocurrency mixing services can be an effective strategy. These services, also known as tumblers or mixers, help to obscure the origin and destination of your funds, making it difficult to trace them back to your Trezor wallet.
Cryptocurrency mixing services work by taking your digital assets and mixing them with numerous other transactions, creating a complex network of transactions that make it challenging to track individual funds. This process helps to break the link between your initial wallet address and the final destination address, maintaining your anonymity and privacy.
To use a cryptocurrency mixing service, you’ll need to follow a few simple steps. First, select a reputable and trustworthy mixing service, ensuring that they have a proven track record of protecting their users’ privacy.
Next, you’ll need to provide the mixing service with the funds you want to mix. This involves sending your cryptocurrency from your Trezor wallet to the mixing service’s designated address. Make sure to follow the instructions provided by the mixing service carefully to ensure a successful transaction.
Once your funds are received by the mixing service, they will be mixed with other transactions from various sources. This process can take some time, as the mixer tries to make it difficult to trace the origin and destination of the funds.
After the mixing process is complete, you can withdraw your mixed funds to a new wallet address, which can be generated by your Trezor wallet. This new address adds an additional layer of privacy and makes it even more challenging to trace your funds back to your original wallet.
Using cryptocurrency mixing services can help to enhance the privacy and security of your Trezor wallet. By breaking the transaction trail and mixing your funds with others, you make it challenging for anyone to trace your cryptocurrency activities back to you, adding an extra layer of anonymity and protecting your funds.
Employing a Hardware Wallet Hideaway
One effective method to hide your Trezor wallet is to employ a hardware wallet hideaway. This involves finding a secure and inconspicuous location to store your Trezor hardware wallet, making it less likely to be discovered by unauthorized individuals.
The key to a successful hardware wallet hideaway is to choose a location that is both secure and easily accessible for you. Consider using a safe or a lockbox that provides physical protection for your Trezor device.
You can also opt for more creative hiding spots within your home, such as hollowed-out books, hidden compartments in furniture, or even specially designed camouflage cases. The goal is to find a place that blends seamlessly with your surroundings and avoids drawing attention.
Additionally, you may want to consider using a decoy wallet. This involves placing a dummy wallet in a visible and easily accessible location, while keeping your actual Trezor wallet hidden elsewhere. This can serve as a distraction and mislead any potential intruders.
Remember to choose a hiding spot that is unlikely to be accidentally discovered or compromised. Avoid common hiding spots that criminals may check first, such as under the mattress, in the sock drawer, or in obvious locations like a desk drawer.
When hiding your Trezor wallet, ensure that it is protected from environmental factors that can potentially damage or compromise its functionality. Consider factors such as temperature, humidity, and exposure to magnetic fields.
Employing a hardware wallet hideaway adds an extra layer of physical security to your Trezor wallet. By keeping it out of sight and safely concealed, you reduce the risk of theft or unauthorized access to your cryptocurrency funds.
Utilizing a Virtual Machine for Added Security
When it comes to hiding and securing your Trezor wallet, utilizing a virtual machine (VM) can provide an additional layer of security. A VM is a software emulation of a computer system that allows you to run applications and programs in an isolated environment.
By using a virtual machine, you can create a separate and isolated operating system solely dedicated to managing your Trezor wallet. This helps to minimize the risk of malware or keyloggers that may exist on your primary operating system compromising the security of your wallet.
Setting up a virtual machine for your Trezor wallet involves a few simple steps. First, choose a reliable virtualization software such as VirtualBox or VMware, and install it on your computer.
Next, create a new virtual machine and install an operating system that is compatible with the Trezor wallet software. You can choose a lightweight, security-focused operating system like Tails or Ubuntu for added security.
Once your virtual machine is set up, install the necessary Trezor wallet software and connect your Trezor hardware wallet to the virtual machine. This allows you to perform all wallet-related tasks within the isolated environment, keeping your funds secure from potential threats on your primary operating system.
Utilizing a virtual machine for your Trezor wallet provides several advantages. It helps to separate your wallet activities from other potentially compromised applications or processes running on your computer. It also provides an extra layer of isolation and protection for your private keys and transactions.
However, it’s important to note that virtual machines are not foolproof, and you should still adopt other security measures to protect your wallet. Regularly update your virtual machine software, use strong passwords, and employ encryption for added protection.
Overall, utilizing a virtual machine for your Trezor wallet adds an additional level of security by isolating your wallet activities from potentially compromised environments. It provides peace of mind and reduces the risk of unauthorized access to your cryptocurrency funds.
Keeping your Recovery Seed Phrase Securely Hidden
One of the most critical aspects of securing your Trezor wallet is safeguarding the recovery seed phrase. The recovery seed phrase is a sequence of words that serves as a backup for your wallet, allowing you to recover your funds in case your Trezor device is lost, stolen, or damaged.
To hide your recovery seed phrase, it’s important to consider both physical and digital security measures:
Physical Security:
- Write down your recovery seed phrase on a piece of paper or use a metal recovery seed phrase storage device specifically designed for this purpose.
- Keep the recovery seed phrase in a secure and hidden location, such as a safe, a lockbox, or a hidden compartment.
- Avoid storing the recovery seed phrase in easily accessible places, such as in a regular wallet, on a computer or mobile device, or in a cloud storage service.
- Consider using a decoy or diversion method to mislead potential intruders, such as writing a fake recovery seed phrase or mixing the real one with irrelevant words.
Digital Security:
- Avoid storing your recovery seed phrase on any digital devices, including computers, smartphones, or cloud storage platforms.
- Never share your recovery seed phrase with anyone, including online services, support staff, or strangers.
- Be cautious of phishing attempts or fake recovery seed phrase generators. Only trust reputable sources and official Trezor channels.
- Consider encrypting your recovery seed phrase using encryption software or a password manager for added protection.
Remember, losing your recovery seed phrase or having it fall into the wrong hands can result in a complete loss of access to your funds. Therefore, it is critical to keep it securely hidden and away from prying eyes.
It’s also important to regularly check and verify the safety of your recovery seed phrase storage. Routinely inspect the condition of the paper or metal storage device and ensure it remains in a secure location.
By taking the necessary precautions to hide and protect your recovery seed phrase, you ensure that even if your Trezor device is compromised or lost, you will have a secure backup to recover your funds and maintain control over your cryptocurrency investments.
Taking Precautions when using Online Platforms
When it comes to hiding your Trezor wallet, it’s important to take precautions when using online platforms. While online platforms can provide convenience and accessibility, they also pose potential risks to the security and privacy of your cryptocurrency funds.
Here are some essential precautions to consider:
- Choose reputable platforms: When using online platforms, such as cryptocurrency exchanges or wallet providers, choose those with a strong reputation and a proven track record of security. Research reviews and user experiences to ensure that the platform takes the necessary precautions to protect its users’ funds.
- Enable two-factor authentication (2FA): Two-factor authentication adds an extra layer of security by requiring an additional verification step, such as a code sent to your mobile device, when logging in or making transactions. Activate 2FA on all platforms that offer this feature to mitigate the risk of unauthorized access.
- Use separate email and strong passwords: Create a unique email address and a strong, complex password specifically for your cryptocurrency-related activities. Avoid reusing passwords and use a password manager to securely store and manage your login credentials.
- Be mindful of phishing attempts: Be cautious of phishing attempts where attackers may impersonate legitimate platforms to trick you into revealing your credentials. Always double-check the website URL, use bookmarks or manually type the URL, and never click on suspicious links or download unknown attachments.
- Regularly update your software and firmware: Keep your computer’s operating system, antivirus software, and firmware of your Trezor wallet up to date. Updates often contain important security patches that address vulnerabilities and ensure the latest security measures are in place.
- Monitor your accounts: Regularly review your account activity and transaction history on online platforms. Set up alerts to notify you of any suspicious or unauthorized activity. Report any irregularities immediately to the platform’s support team.
- Consider using a VPN: When accessing online platforms, especially when using public Wi-Fi networks, consider using a virtual private network (VPN) to encrypt your internet connection and protect your data from potential eavesdroppers.
By taking precautions when using online platforms, you can enhance the security and privacy of your Trezor wallet. It’s important to stay vigilant and stay informed about potential threats and new security measures to adapt and protect your cryptocurrency investments effectively.
Safeguarding your Trezor Wallet during Travel
Traveling with your Trezor wallet requires extra precautions to ensure the security of your cryptocurrency funds. Whether you’re going on a short trip or an extended journey, here are some essential tips to safeguard your Trezor wallet during travel:
- Keep your Trezor wallet with you: Avoid placing your Trezor wallet in checked baggage or leaving it unattended in hotel rooms or other public places. Keep it with you at all times to minimize the risk of loss or theft.
- Secure your Trezor with a strong password: Ensure that your Trezor wallet is protected with a strong and unique PIN code. Use a combination of numbers, letters, and symbols to create a robust password that is not easily guessable.
- Back up your wallet seed phrase: Before traveling, ensure that you have securely backed up your wallet’s recovery seed phrase and stored it in a separate location. This will allow you to recover your funds in case your Trezor wallet gets lost or stolen.
- Use a security cable or lock: Consider using a security cable or lock to physically secure your Trezor wallet when it’s not in use. This can provide an extra layer of protection against theft or unauthorized access.
- Avoid public Wi-Fi networks: Public Wi-Fi networks are often unsecured and can pose a security risk. Avoid accessing your Trezor wallet or making transactions when connected to public Wi-Fi. Instead, use a personal Wi-Fi hotspot or a trusted cellular network connection.
- Use a VPN: If you need to access your Trezor wallet online while traveling, consider using a virtual private network (VPN) to encrypt your internet connection and protect your data from potential hackers or eavesdroppers.
- Be cautious of physical surveillance: Be mindful of your surroundings and be cautious of individuals who may be watching or attempting to gain unauthorized access to your Trezor wallet. Use privacy screens or shields to prevent prying eyes from seeing your transactions or PIN entry.
- Inform trusted contacts: If you’re traveling with a Trezor wallet and something unexpected happens, it’s important to inform trusted contacts who can assist you with recovery or securing your funds. This can include family members, friends, or representatives from your cryptocurrency exchange or wallet provider.
By following these precautions, you can ensure the safety and security of your Trezor wallet while traveling. Remember, it’s crucial to remain vigilant and prioritize the protection of your cryptocurrency funds, especially in unfamiliar or potentially high-risk environments.
Implementing Smart Hidden Storage Solutions
Implementing smart hidden storage solutions is an effective way to hide and protect your Trezor wallet from prying eyes. By creatively concealing your wallet, you can add an extra layer of security to your cryptocurrency funds. Here are some smart hidden storage ideas to consider:
- Secret compartments: Utilize hidden compartments in common household objects, such as books, picture frames, or furniture. These compartments can be specially designed or DIY projects that discreetly conceal your Trezor wallet.
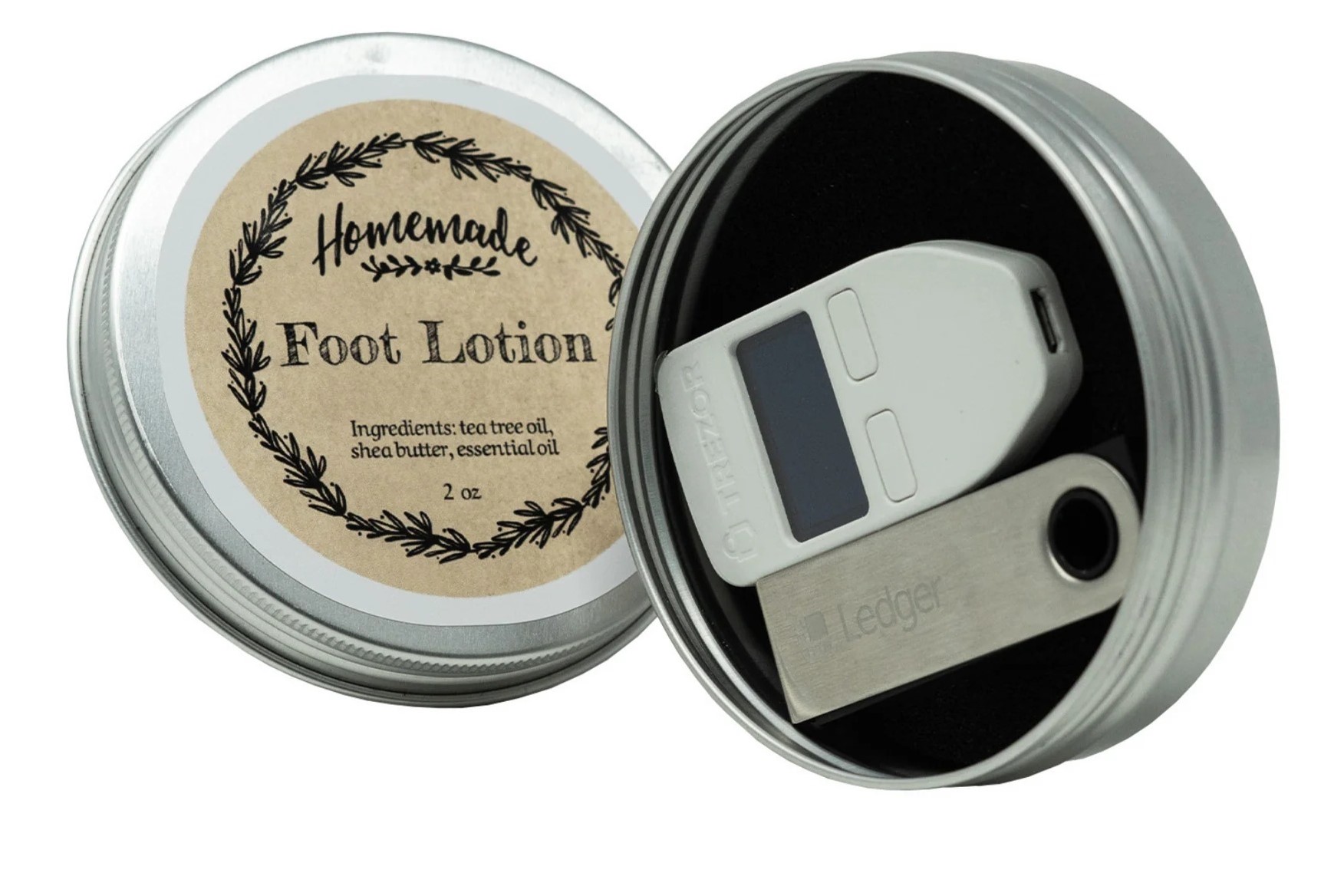
- Camouflage cases: Use specially designed cases that mimic everyday objects, such as a phone case, a wallet, or a portable power bank. These cases can discreetly hold your Trezor wallet while blending in seamlessly with your other belongings.
- Multipurpose containers: Utilize multipurpose containers, such as small lockboxes or portable safes, that have built-in compartments for hiding your Trezor wallet. These containers can provide both secure storage and camouflage.
- Creative hiding spots: Get creative by finding unconventional hiding spots in your home or office. For example, hollowed-out potted plants, false panels behind wall art, or hidden holes in the ceiling can be clever places to discreetly store your Trezor wallet.
- Decoy diversions: Consider using decoy objects to divert attention from your Trezor wallet. For instance, place a dummy wallet or a small amount of cash in an easily accessible location while keeping your real Trezor wallet hidden elsewhere.
- Secure storage devices: Invest in secure storage devices that are specifically designed to protect your Trezor wallet from physical damage or theft. These devices may include metal wallets, tamper-proof bags, or encrypted storage solutions.
When implementing smart hidden storage solutions, it’s important to ensure that your Trezor wallet is still easily accessible to you. Strike a balance between security and convenience, making sure that you can retrieve your wallet efficiently when needed.
Remember to keep a record or map of your hidden storage locations to avoid forgetting where you’ve hidden your Trezor wallet. Additionally, periodically review and update your storage solutions to adapt to any changes in your living or working environment.
By implementing smart hidden storage solutions, you can effectively conceal and protect your Trezor wallet, adding an extra layer of security to your cryptocurrency investments.
Regularly Updating your Security Measures
Regularly updating your security measures is essential to keep your Trezor wallet and cryptocurrency funds secure. The threat landscape is constantly evolving, and staying proactive with your security practices is key to mitigating risks. Here are some important aspects to consider when updating your security measures:
- Software Updates: Regularly update the firmware and software of your Trezor wallet. Firmware updates often include bug fixes, performance improvements, and security patches that address vulnerabilities and strengthen the overall security of your device.
- Passwords and PINs: Update your passwords and PINs regularly, creating strong and unique combinations that are not easily guessable. Avoid using the same passwords for multiple accounts and consider using a password manager to help generate and securely store your credentials.
- Two-Factor Authentication (2FA): Enable 2FA on all platforms and services that support it. Regularly review and update your 2FA settings, such as changing the codes or using alternative 2FA methods for added security.
- Email Security: Be cautious of phishing attempts via email. Regularly review and update your email security settings, such as enabling spam filters and adjusting security levels. Be vigilant in identifying suspicious emails and avoid clicking on unknown links or downloading attachments.
- Backup and Recovery: Regularly review and update your backup and recovery procedures. Ensure that your wallet’s recovery seed phrase is securely stored and regularly verify its accuracy. Consider creating multiple backups in different secure locations for added redundancy.
- Privacy Settings: Regularly review and update the privacy settings on your devices, applications, and online platforms. Limit the amount of personal information shared and minimize data collection when possible. Be aware of privacy risks associated with third-party applications and services.
- Periodic Security Audits: Conduct regular security audits of your devices, networks, and online platforms. This includes performing vulnerability scans, checking for unauthorized access, and reviewing system logs. Address any identified vulnerabilities promptly.
- Stay Informed: Stay updated on the latest security trends, vulnerabilities, and best practices in the cryptocurrency space. Follow reputable sources, security blogs, and news outlets to remain informed about potential threats and security advancements.
Remember that security is an ongoing process, and updating your security measures should be a regular practice. Set reminders or schedule regular security checkups to ensure that you stay on top of any necessary updates or changes.
By regularly updating your security measures, you can stay one step ahead of potential threats and ensure the continued safety of your Trezor wallet and cryptocurrency investments.
Storing your Trezor Wallet in a Safe Place
Storing your Trezor wallet in a safe place is crucial to protect your cryptocurrency funds from theft, loss, or damage. Here are some important considerations when it comes to storing your Trezor wallet:
- Choose a secure location: Select a secure and discreet location to store your Trezor wallet. This could be a locked drawer, a home safe, a safety deposit box, or any other place that offers protection from potential physical threats.
- Consider a backup location: It’s a good practice to have a backup storage location for your Trezor wallet. This provides additional protection in case your primary storage location becomes compromised or inaccessible.
- Avoid obvious hiding spots: Avoid storing your Trezor wallet in obvious hiding spots that could be easily discovered, such as under the mattress, inside a desk drawer, or in a commonly used safe box. Choose a location that is less predictable and less likely to be targeted by thieves.
- Use natural camouflage: Utilize natural camouflage by integrating your Trezor wallet into everyday objects or locations. For example, you can conceal it within a household item that blends in with its surroundings or keep it within a stack of books on a bookshelf.
- Physical protection: Consider using a protective case or sleeve for your Trezor wallet to safeguard it from scratches, impact, and environmental factors. This adds an extra layer of protection and helps maintain the longevity of the device.
- Secure digital backups: Create secure digital backups of your Trezor wallet data, including your recovery seed phrase, and store them in encrypted storage solutions or password-protected devices. Be sure to keep these backups separate from your physical Trezor wallet storage.
- Share information selectively: Be cautious about sharing information regarding the location or existence of your Trezor wallet. Limit access to this knowledge to trusted individuals whom you can rely on for support or recovery purposes.
- Regularly review and update: Periodically review and update your storage strategy for your Trezor wallet. As circumstances change, you may need to make adjustments to ensure the continued security and accessibility of your funds.
Remember to strike a balance between convenience and security when choosing a storage location. It should be easily accessible to you, but challenging or inconspicuous for potential intruders to discover.
By storing your Trezor wallet in a safe place, you can protect your cryptocurrency funds from physical threats and have peace of mind knowing that your assets are securely stored.
Taking Advantage of Additional Security Features
When it comes to protecting your Trezor wallet and securing your cryptocurrency funds, it’s important to take advantage of the additional security features offered by the device. These features are designed to enhance the overall security of your wallet and provide you with peace of mind. Here are some key security features to consider:
- Passphrase Encryption: Trezor wallets offer the option to set up a passphrase in addition to your PIN code. This passphrase acts as an extra layer of security, providing an additional barrier for unauthorized access to your wallet. It’s essential to choose a strong, unique, and memorable passphrase and ensure that it is securely stored.
- Multi-signature Transactions: Utilize the multi-signature functionality offered by Trezor wallets for added security. This feature requires multiple signatures to authorize transactions, reducing the risk of a single point of failure and protecting your funds from unauthorized transactions.
- Hidden Wallets: Take advantage of the hidden wallets feature provided by Trezor. This allows you to create multiple wallets within your device, each with its own unique passphrase. By using hidden wallets, you can compartmentalize your funds and add an extra layer of security and privacy.
- Secure Recovery Process: Follow the recommended recovery process for your Trezor wallet to ensure the safe retrieval of your funds. This involves securely storing your recovery seed phrase and verifying its accuracy during the setup process. Be cautious of potential phishing attempts or fake recovery processes and only use official Trezor channels.
- USB Communication Verification: Before entering your PIN code or authorizing transactions on your Trezor device, always verify that you’re communicating with genuine Trezor software. Check the security indicators on the device’s screen, such as the Trezor logo or the confirmation message. This step helps prevent falling victim to phishing attacks or rogue software.
- Brute-Force Attack Mitigation: Take advantage of the built-in protections against brute-force attacks provided by Trezor devices. The device enforces a delay between each incorrect PIN attempt, making it significantly more challenging for malicious actors to guess or crack your PIN code.
- Regular Firmware Updates: Keep your Trezor firmware up to date by regularly installing the latest updates provided by the manufacturer. Firmware updates often include security patches, bug fixes, and improvements to ensure the highest level of protection for your Trezor wallet.
By taking advantage of these additional security features, you can maximize the protection and privacy of your Trezor wallet. Each feature adds a unique layer of defense against unauthorized access and ensures the safe storage of your cryptocurrency funds.
Consulting Expert Advice on Privacy and Security
When it comes to the privacy and security of your Trezor wallet and cryptocurrency investments, it’s always wise to seek expert advice. Consulting experts in the field can provide valuable insights, guidance, and best practices to enhance the protection of your funds. Here are some reasons why consulting expert advice on privacy and security is beneficial:
Stay Updated with Evolving Threats: Experts in privacy and security closely monitor the ever-changing landscape of cryptocurrency risks and vulnerabilities. By consulting with them, you can stay informed about the latest threats and security trends, ensuring that your security measures remain robust.
Receive Personalized Recommendations: Experts can provide personalized recommendations based on your specific circumstances and needs. They can assess your current security setup, identify potential weaknesses, and advise on the most effective strategies to enhance the protection of your Trezor wallet and funds.
Access In-depth Knowledge and Expertise: Experts possess deep knowledge and expertise in the field of cryptocurrency security. They can explain complex concepts, such as encryption, multi-signature wallets, and secure recovery processes, in a way that is easy to understand and implement.
Identify and Mitigate Risks: With their experience, experts can help identify potential risks and vulnerabilities in your security setup. They can guide you in implementing preventive measures and mitigating factors to minimize the likelihood of security breaches or unauthorized access.
Learn Best Practices and Industry Standards: Experts can provide invaluable insights into industry best practices and standards for securing Trezor wallets and cryptocurrencies. They can educate you on topics such as password management, phishing prevention, network security, and secure storage practices.
Address Specific Concerns: If you have specific concerns or questions about certain aspects of Trezor wallet security or privacy, experts can provide guidance and answers. Their expertise allows them to address your concerns with accuracy and authority, giving you peace of mind about the security of your funds.
Consulting expert advice on privacy and security can be done through various channels, such as forums, online communities, or even hiring professional security consultants. It’s important to ensure that the experts you consult are reputable and have a proven track record in the field.
By seeking expert advice, you can leverage the knowledge and experience of professionals to implement robust security measures and protect your Trezor wallet and cryptocurrency investments effectively.
A Final Word of Warning and Encouragement
As we conclude this guide on hiding your Trezor wallet and enhancing its security, it’s important to provide a final word of both warning and encouragement. While we’ve covered various strategies and measures to protect your cryptocurrency funds, it’s crucial to stay vigilant and be proactive in ensuring the security of your Trezor wallet. Here are a few key points to keep in mind:
Stay Informed: The world of cryptocurrency is constantly evolving, and new threats and vulnerabilities emerge regularly. Stay updated on the latest security practices, software updates, and industry news related to Trezor wallets. By staying informed, you can adapt your security measures to address new challenges effectively.
Practice Secure Habits: In addition to implementing security measures, develop secure habits in your day-to-day interactions with your Trezor wallet. This includes being cautious of phishing attempts, regularly updating passwords, avoiding public Wi-Fi networks, and exercising caution when sharing information related to your wallet.
Balance Convenience and Security: While it’s essential to prioritize security, finding a balance between security measures and convenient access to your funds is equally important. Strive to implement measures that offer a high level of protection without sacrificing usability or accessibility.
Backup and Test: Regularly backup your Trezor wallet’s recovery seed phrase and test the recovery process to ensure it’s functioning correctly. A proper backup allows you to recover your funds in case of device loss or damage, while testing ensures that you have retained the necessary information to restore your wallet.
Trust Your Gut: If something feels suspicious or too good to be true, trust your instincts. Be cautious of unsolicited messages, offers, or online resources claiming to provide additional security or enhanced wallet functionality. Stick to official Trezor channels and verified sources when seeking guidance or implementing new security practices.
Continuous Improvement: Remember that security is an ongoing process, and there is no one-size-fits-all solution. Regularly review and update your security measures to adapt to new threats and vulnerabilities. Embrace a mindset of continuous improvement to ensure the long-term security and protection of your cryptocurrency investments.
By following these guidelines and taking the necessary precautions, you can significantly enhance the privacy and security of your Trezor wallet. While no security measures can provide an absolute guarantee, implementing best practices and staying informed will go a long way in protecting your funds.
Remember, the ultimate responsibility for the security of your Trezor wallet rests with you. Stay proactive, be mindful of potential risks, and empower yourself with knowledge to safeguard your cryptocurrency investments effectively.