What is Zeus Malware?
Zeus malware, also known as Zbot, is a dangerous form of malware that targets computers running on Microsoft Windows operating systems. It was first identified in 2007 and quickly gained notoriety for its sophisticated capabilities and widespread distribution.
Zeus malware is primarily designed for financial fraud and identity theft. Once it infiltrates a system, it aims to steal sensitive information such as online banking credentials, credit card details, and personal data. This stolen information can then be used by cybercriminals to make unauthorized transactions, commit identity theft, or sell the data on the black market.
Zeus malware is typically spread through various means, including malicious email attachments, infected websites, drive-by downloads, and social engineering tactics. Once a user unknowingly installs the malware on their system, it remains hidden, making it difficult to detect and remove.
One of the key characteristics of Zeus malware is its ability to operate in a stealthy manner. It can evade detection by traditional antivirus software and firewall systems, making it challenging for users to identify its presence on their computers.
Once Zeus malware successfully infects a system, it establishes a connection with a command and control (C&C) server. This connection enables the malware authors to remotely control the infected computer, monitor user activities, and extract sensitive information.
The Zeus malware is constantly evolving, with new variants and techniques emerging regularly. Over the years, it has become increasingly sophisticated, making it more challenging for security experts to combat. Cybercriminals behind Zeus malware are continuously refining their techniques, employing encryption, obfuscation, and anti-analysis mechanisms to stay one step ahead of security measures.
It is crucial to be aware of the threat posed by Zeus malware and take proactive measures to protect your computer and personal information from its damaging effects.
How Does Zeus Malware Infect Your Computer?
Zeus malware employs various methods to infect computers and compromise their security. Understanding these infection vectors can help users take appropriate precautions to mitigate the risk.
One primary method used by Zeus malware is through phishing emails. Cybercriminals send emails that appear to be from reputable sources, luring recipients into clicking on malicious links or downloading infected attachments. These emails often mimic legitimate organizations, such as banks or financial institutions, tricking users into divulging sensitive information or unwittingly installing the malware.
Another common infection vector is through infected websites. Cybercriminals inject malicious code into legitimate websites, making them capable of exploiting vulnerabilities in browsing software. When unsuspecting users visit these compromised websites, the malware is silently downloaded onto their computers, without their knowledge or consent.
Zeus malware can also exploit software vulnerabilities through drive-by downloads. By infecting legitimate websites with exploit code, the malware gains unauthorized access to the victim’s system when they visit the compromised website. These exploits take advantage of outdated software versions, browser plugins, or plugins within other software to gain access to the user’s computer.
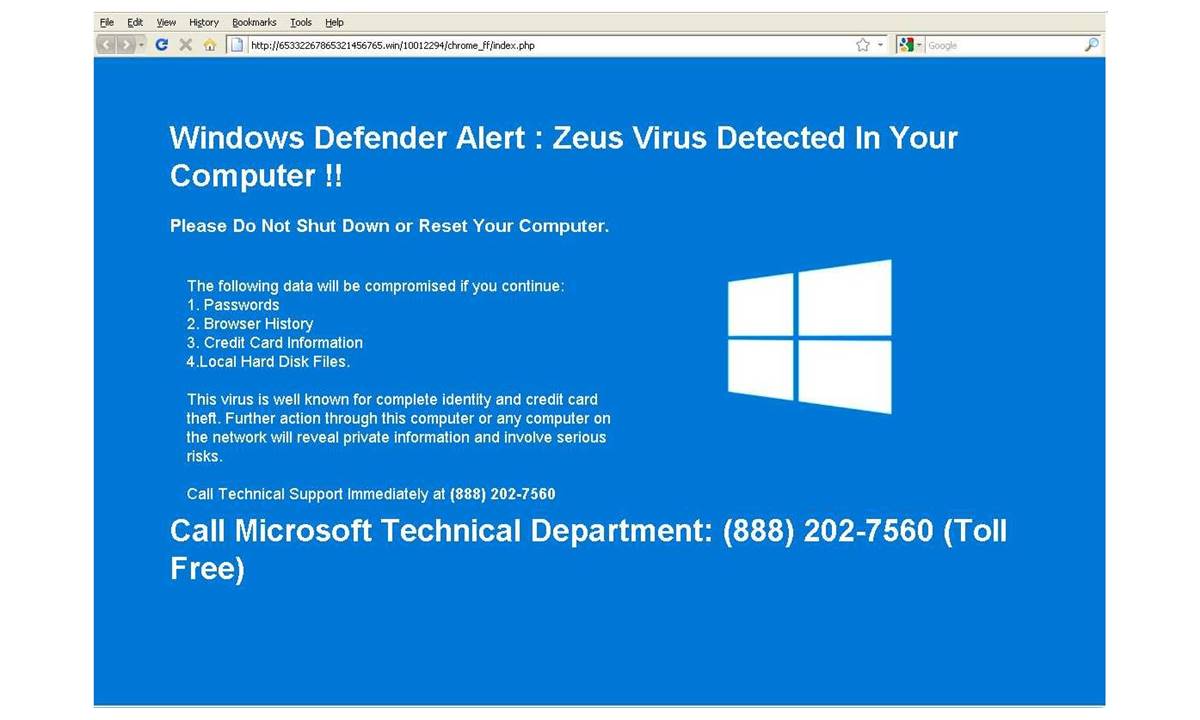
Social engineering is another technique used by Zeus malware to infect computers. Through social engineering tactics, cybercriminals manipulate users into willingly providing access to their systems. This can be done through deceptive websites, fake update alerts, or enticing offers, effectively tricking users into downloading and installing the malware themselves.
Once Zeus malware infects a computer, it can spread through various means, such as through removable media, network shares, or even via botnets. This facilitates the malware’s ability to move laterally within a network, infecting additional devices and compromising an organization’s security infrastructure.
It is crucial for users to exercise caution while browsing the internet, opening emails, or downloading attachments. Regularly updating software and using robust antivirus software can help protect against known vulnerabilities and detect potential threats.
By understanding the infection vectors employed by Zeus malware and adopting security best practices, users can reduce the risk of falling victim to this insidious threat.
Signs and Symptoms of Zeus Malware Infection
Detecting the presence of Zeus malware on your computer is crucial for taking prompt action to protect your sensitive information. Although the malware is designed to operate covertly, there are several signs and symptoms that can indicate a possible infection.
One common symptom of a Zeus malware infection is a noticeable decrease in your computer’s performance. The malware operates in the background, consuming system resources to carry out its malicious activities. This can result in sluggish performance, slow startup times, and unresponsive applications.
Unexpected system crashes and frequent system freezes are also red flags of a possible Zeus malware infection. The malware may disrupt the stability of your computer, leading to these frustrating issues.
If you notice unfamiliar or suspicious programs running on your computer, it could be a sign of Zeus malware. The malware often disguises itself as legitimate processes or applications, making it difficult to identify without thorough inspection.
Browsers being redirected to unfamiliar or malicious websites can be an indication of Zeus malware infection. The malware may alter your browser settings or inject malicious code, leading to unwanted redirects to phishing sites or spreading further malware.
Unexplained changes in your web browser, such as the appearance of new toolbars, extensions, or search engines, can also be indicative of Zeus malware. These changes are often made without the user’s consent or knowledge.
Another symptom is the sudden emergence of pop-up advertisements and spam messages. Zeus malware may display intrusive ads or flood your inbox with unsolicited emails, promoting potentially harmful products or services.
If you notice unusual network activity on your computer, including large amounts of data being sent or received, it could be a sign of Zeus malware. The malware often communicates with its command and control (C&C) server, transferring stolen information or receiving new instructions.
Additionally, if you find that your personal files, such as documents, photos, or videos, have become inaccessible or encrypted, it could be a result of Zeus malware. Some variants of the malware incorporate ransomware capabilities to extort money from victims.
If you experience any of these signs or symptoms, it is important to take immediate action to remove the Zeus malware from your system and protect your sensitive information.
Steps to Remove Zeus Malware
Removing Zeus malware from your computer is essential to safeguard your sensitive information and restore your system’s security. Follow these steps to effectively remove Zeus malware:
- Disconnect from the internet: Start by disconnecting your computer from the internet to prevent the malware from communicating with its command and control server, minimizing the risk of further damage.
- Run a thorough antivirus scan: Use a reputable antivirus software with the latest virus definitions to perform a comprehensive scan of your entire system. This scan will help detect and remove any traces of Zeus malware present on your computer. Follow the prompts provided by the antivirus software to quarantine or delete the detected threats.
- Utilize anti-malware tools: Consider using specialized anti-malware tools that specifically target and remove Zeus malware. These tools are designed to detect and eliminate even the most sophisticated variants of Zeus malware that may have evaded traditional antivirus software.
- Remove suspicious or unfamiliar programs: Access the Control Panel on your computer and uninstall any suspicious or unfamiliar programs that you suspect may be related to Zeus malware. Look for programs with random or unusual names, as well as those that were installed without your knowledge or consent.
- Delete malicious files and folders: Use your antivirus software or an anti-malware tool to scan and delete any malicious files and folders associated with Zeus malware. Pay attention to system folders and directories where malware components may be hidden.
- Update your operating system and software: Ensure that your operating system, as well as all installed software and applications, are up to date with the latest security patches and updates. This helps close any vulnerabilities that might have been exploited by the Zeus malware.
- Change passwords: As a precautionary measure, change the passwords for your online accounts, especially those related to banking, email, social media, and any other important services that may have been compromised by Zeus malware. Use strong, unique passwords and consider enabling two-factor authentication for added security.
- Reconnect to the internet and monitor: Once you have completed the removal steps, you can reconnect to the internet. However, proceed with caution and closely monitor your computer for any unusual activity or signs of a recurring Zeus malware infection. Be vigilant about maintaining good security practices to prevent future infections.
By following these steps and remaining proactive in your cybersecurity efforts, you can effectively remove Zeus malware from your computer and minimize the risk of future infections.
Antivirus Software and Tools to Eliminate Zeus Malware
When dealing with Zeus malware, having reliable antivirus software and specialized tools is crucial for effective detection and elimination. Here are some recommended options:
- Comprehensive Antivirus Software: Look for reputable antivirus software that offers robust malware detection and removal capabilities. Some well-known antivirus solutions include Norton, McAfee, Avast, and Bitdefender. Ensure that your chosen software is regularly updated with the latest virus definitions to effectively combat Zeus malware and other emerging threats.
- Malware Removal Tools: Consider using specialized malware removal tools that specifically target Zeus malware. Tools such as Malwarebytes and Spybot Search & Destroy are designed to detect and remove various types of malware, including Zeus. These tools often have advanced detection mechanisms and can thoroughly scan your system to identify and eliminate any traces of the malware.
- Online Virus Scanners: Online virus scanners offer an additional layer of protection against Zeus malware. Websites like VirusTotal and ESET Online Scanner allow you to upload suspicious files or URLs for scanning and detection of malware. These online scanners utilize multiple antivirus engines to provide comprehensive results, helping you identify and eliminate Zeus malware from your system.
- Real-Time Protection: Look for antivirus software that provides real-time protection against malware, including Zeus. Real-time protection actively monitors your system, scans incoming files, and blocks malicious activities, ensuring that any potential threats are detected and neutralized immediately.
- Firewalls: A robust firewall can help prevent unauthorized access to your system and block malicious traffic. Configuring your firewall to restrict inbound and outbound connections can provide an additional layer of defense against Zeus malware. Many antivirus software packages also include firewall capabilities, offering comprehensive protection in a single solution.
Remember, the effectiveness of antivirus software and tools in eliminating Zeus malware depends on their regular updates and use of the latest threat intelligence. Additionally, it is essential to exercise caution while browsing the internet, downloading files, and opening email attachments to minimize the risk of encountering Zeus malware and other forms of malware.
By leveraging reputable antivirus software and specialized tools, you can enhance your computer’s security and effectively eliminate Zeus malware from your system.
Manual Removal of Zeus Malware
If you suspect that your computer is infected with Zeus malware and want to manually remove it, here are some steps you can take:
- Enter Safe Mode: Restart your computer and enter Safe Mode. This helps prevent any malicious processes from running and allows you to have more control over your system.
- Identify Malicious Processes: Open the Task Manager (Ctrl+Shift+Esc) and look for any suspicious or unfamiliar processes running in the background. Pay attention to processes with random names or high CPU usage that you cannot attribute to legitimate software.
- Terminate Malicious Processes: Right-click on the suspicious processes and select “End Task” to stop them. Note down the names of these processes for further investigation.
- Remove Startup Entries: Open the System Configuration tool by typing “msconfig” in the Run dialog box (Windows Key+R). Go to the Startup tab and disable any entries that you suspect may be related to Zeus malware. These entries may appear with random names or have no clear description.
- Delete Malicious Files and Folders: Use File Explorer to navigate to locations such as the AppData, Temp, and ProgramData directories. Look for any suspicious files or folders associated with Zeus malware. Delete them permanently, taking caution not to delete any important system files.
- Modify Registry Entries: Open the Registry Editor by typing “regedit” in the Run dialog box (Windows Key+R). Navigate to the HKEY_LOCAL_MACHINE and HKEY_CURRENT_USER branches and search for registry keys related to Zeus malware. Delete any keys or values associated with the malware, but exercise caution as modifying the registry incorrectly can cause system instability.
- Clear Browser Cache and Extensions: In your web browser, go to the settings menu and clear your browser cache and cookies. Additionally, remove any suspicious or unwanted browser extensions or plugins that may have been installed without your knowledge.
- Restart Your Computer: After performing the manual removal steps, restart your computer in normal mode to ensure that the changes take effect.
It is important to note that manual removal of Zeus malware can be challenging and time-consuming. There is a risk of accidentally deleting important system files or leaving behind hidden malware components. Therefore, it is highly recommended to use reliable antivirus software or seek the assistance of a cybersecurity professional if you are unsure about performing manual removal.
By following these steps, you can attempt to manually remove Zeus malware from your computer. However, it is crucial to remain vigilant and regularly update your security software to prevent future infections.
Preventing Future Infections of Zeus Malware
To protect your computer from future infections of Zeus malware and other similar threats, it is crucial to adopt proactive security measures. Here are some steps you can take to minimize the risk:
- Keep Your Software Up to Date: Regularly update your operating system, web browsers, and all installed software to ensure you have the latest security patches and bug fixes. Cybercriminals often exploit vulnerabilities in outdated software versions.
- Use Reliable Antivirus Software: Install reputable antivirus software and keep it up to date with the latest virus definitions. Regularly scan your system for malware and ensure real-time protection is enabled to detect and block threats as they arise.
- Exercise Caution when Opening Emails: Be wary of unsolicited emails, especially those with attachments or links. Avoid opening emails from unknown senders and never download or execute attachments if you are unsure of their legitimacy. Additionally, be cautious of phishing attempts and carefully examine email addresses and content for signs of deception.
- Practice Safe Browsing Habits: Be cautious when visiting unfamiliar websites or downloading files from the internet. Stick to reputable websites and avoid clicking on suspicious links or pop-up ads. Utilize browser extensions that provide website reputation ratings and block known malicious sites.
- Use Strong and Unique Passwords: Use strong, complex passwords for all your online accounts. Avoid using common passwords or reusing passwords across multiple accounts. Consider using a password manager to securely store and generate unique passwords.
- Enable Two-Factor Authentication: Enabling two-factor authentication adds an extra layer of security to your online accounts. It requires you to provide a second form of verification, such as a verification code sent to your mobile device, in addition to your password.
- Regularly Backup Your Data: Create regular backups of your important files and store them in a separate location, either offline or in the cloud. This ensures that even if your system is compromised, you can recover your data without having to pay ransomware or suffer permanent loss.
- Be Cautious with External Devices: Scan any external devices, such as USB drives or external hard drives, for malware before connecting them to your computer. These devices can be a potential source of infection if they are already compromised.
- Educate Yourself: Stay informed about the latest online threats and phishing techniques. Regularly educate yourself about best practices for staying safe online and share this knowledge with family and friends to help them protect their systems as well.
By implementing these preventive measures and maintaining good cybersecurity hygiene, you can significantly reduce the risk of future infections of Zeus malware and other malicious threats.
Additional Security Measures for Protection Against Malware
In addition to the fundamental preventive measures, there are several additional security measures you can take to enhance your protection against malware, including Zeus malware:
- Enable Firewall Protection: Ensure that your computer’s built-in firewall is enabled or consider using a reputable third-party firewall. Firewalls monitor incoming and outgoing network traffic, providing an extra layer of defense against malicious activity.
- Use a Virtual Private Network (VPN): A VPN encrypts your internet connection, keeping your online activities private and secure. This can be particularly useful when using public Wi-Fi networks, as it prevents eavesdropping and helps protect against malware attacks.
- Enable Automatic Updates: Enable automatic updates for your operating system and software applications. This ensures that you receive the latest security patches and bug fixes, closing any potential vulnerabilities that malware can exploit.
- Practice Least Privilege: Limit user privileges on your computer to reduce the impact of potential malware infections. Use standard user accounts for day-to-day activities and reserve administrator privileges for specific tasks that require elevated access.
- Implement Web Filtering: Consider using web filtering software or browser extensions that block access to known malicious websites. These tools can provide an extra layer of protection by preventing you from inadvertently visiting harmful websites hosting malware.
- Implement Email Filtering: Use email filtering mechanisms or services that scan incoming emails for malicious attachments and links. These filters can help identify and quarantine potentially dangerous emails, reducing the risk of malware infections via email.
- Regularly Review and Update Privacy Settings: Review the privacy settings of your operating system, web browsers, and applications. Configure these settings to limit the amount of personal information shared and minimize the potential for unauthorized access or data harvesting.
- Perform Regular System Scans: Conduct regular scans of your computer, using both antivirus software and specialized anti-malware tools, to detect any potential threats that may have evaded real-time protection. This helps ensure early detection and removal of malware.
- Implement Network Segmentation: If applicable, segment your network into different zones or subnets to isolate critical systems and limit the potential spread of malware in case of an infection. This helps contain the impact and prevents lateral movement within your network.
- Stay Informed About Emerging Threats: Keep abreast of the latest security news and updates regarding malware, including Zeus malware. Follow reputable cybersecurity blogs and sources to stay informed about emerging threats and new attack techniques.
By implementing these additional security measures and remaining vigilant, you can significantly reduce the risk of malware infections, protecting your computer and sensitive data from the damaging effects of Zeus malware and other malicious threats.
Staying Informed About the Latest Malware Threats
As cyber threats continue to evolve, staying informed about the latest malware threats, including Zeus malware, is essential for maintaining robust cybersecurity. Here are some ways to stay up to date:
- Follow Reputable Cybersecurity Sources: Regularly follow reputable cybersecurity blogs, websites, and industry experts who provide insights and updates on the latest malware threats. Examples include security-focused publications, vendor blogs, and official security advisories from antivirus companies.
- Subscribe to Security Newsletters: Subscribe to newsletters from trusted sources in the cybersecurity community. These newsletters often deliver curated content, including news, analysis, and alerts about emerging malware threats, keeping you informed on the latest developments.
- Participate in Security Forums and Communities: Join security forums and online communities where cybersecurity professionals and enthusiasts discuss malware threats and share insights. Engage in discussions, ask questions, and share your own knowledge to stay informed about the evolving threat landscape.
- Attend Cybersecurity Conferences and Webinars: Attend industry conferences and webinars dedicated to cybersecurity. These events often include presentations and workshops on the latest malware trends, providing valuable insights from industry experts. Take advantage of the networking opportunities to connect with other professionals and exchange information.
- Monitor Security Vendor Blogs and Alerts: Keep an eye on the blogs and alerts published by your antivirus software vendor. These resources often provide timely information about emerging malware threats and steps to protect against them.
- Join Threat Intelligence Sharing Communities: Consider joining threat intelligence sharing communities where organizations and individuals share information about new malware threats. These communities facilitate a collaborative approach to cybersecurity, allowing participants to receive real-time insights and indicators of compromise.
- Regularly Update Security Software: Ensure that your antivirus software and other security tools are regularly updated with the latest virus definitions and threat intelligence. Updated security software can effectively detect and protect against the latest malware threats, including Zeus.
- Stay Current with Security Best Practices: Continuously educate yourself about the latest security best practices, including safe browsing habits, strong password management, and data backup strategies. Adhering to these practices helps mitigate the risk of malware infections and strengthens your overall cybersecurity posture.
- Be Aware of Common Attack Techniques: Stay informed about common attack techniques employed by cybercriminals, such as phishing emails, social engineering, and drive-by downloads. Understanding these techniques can help you recognize and avoid potential malware threats.
- Report Suspicious Activity: If you encounter suspicious or malicious activity on your computer or across your network, report it to the appropriate authorities or the relevant security teams within your organization. Reporting incidents contributes to the collective effort in combating malware and helps other individuals and organizations stay protected.
By actively seeking out and consuming information from reputable sources, and staying engaged in the cybersecurity community, you can stay informed about the latest malware threats and better protect yourself and your systems against them.